SAVE TOP GRADE USING TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Techniques Used in Database Administrations Assignment
Question: Prepare and present the result of scholarly research into emerging database systems and demonstrate research and analysis capabilities as well as communication skills.
What solutions can you propose to effectively manage database transactions, maintain security, and recover the data that are lost from system failure or downtime?
What is your rationale for the transaction management plan, database security procedure, backup plan, and recovery model that you proposed for the case study organization?
DO YOU WANT TO EXCEL IN TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT - ORDER AT EXPERTSMINDS!
Solution:
Introduction of Retail Shop
A retail shop has number of entities but in this model we have considered 6 entities
1) Owner
2) Suppliers
3) Customers
4) Employee
5) Product
6) Roles
7) Transactions
Owner entity represents the owner of the store. A retail store can have multiple owners. Only owners of the store will handle payroll that is owner will pay all the bills for the purchased goods and salaries to the employees employed in the store.
Supplier entity represents the group of suppliers who will supply various goods to the retail store and they will receive payments from the owner for the supplied goods.
Customer entity represents the group of customers who come to the store and select various goods from the store for their regular use. After, selecting various goods they move to cash counter where they are entertained by different employees for the purpose of billing.
Product entity represents the bunch of products which are available in the store with their number of units present in the warehouse. Whenever a supplier supply any item, then the received number of units of that particular item are added in their record and when any employee sells any product then the sold number of units are deducted from number of units of that product available in the store.
Roles entity is defined to eliminate the problem of security. All the owners, suppliers, customers, employees are assigned a particular userid and password to access their respective portals. Only a authorized person can access the respective data i.e. No customer can access any employees portal and no supplier can access customer portal. Also they given rights to database according to their respective roles. For example :-A customer is given permission to read only the customer table of data. He is not given any write permissions.
Transactions entity is defined to record all the transactions that occur in the store whole day. Transactions are recorded in their respective category so that it becomes easy to manage all the transactions.
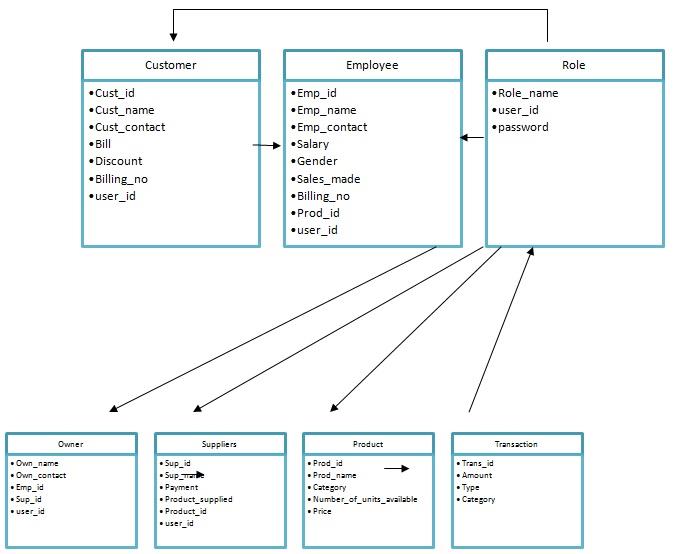
Figure 1 Database Model of Retail shop
DONT MISS YOUR CHANCE TO EXCEL IN TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT SOLUTIONS!
Solutions of various issues
1) Problem of transaction management
There are various transactions that occur in a retail store whole day but to manage all the transactions ia a difficult task. To solve this issue we will categorise all the transactions in three categories (Breitbart, Garcia-Molina & Silberschatz, 1992).
i) Supplier Transactions
The transactions which occur between the owner's account and the supplier's account when we purchase goods for the store are called supplier transactions.
ii) Employee Transaction
The transactions which occur between the owner's account and the employee's account when owner gives salaries and incentives to employees are called employee transactions.
iii) Customer Transactions
The transactions that occur between the owner's account and the customer's account when a customer purchase goods from the store are called customer transactions.
All the transactions that occur in a day are committed to save them permanently in their respective category in transaction table of database or rolled back in case of any error during a particular transaction.
2) Problem of Security
Authorization and Authentication are the two parameters that are required to be considered while keeping the security of database of retail store in mind (Bertino, Jajodia & Samarati, 1995). To solve the problem of authorization and authentication, roles entity is defined.
Authentication
Each Owner, Supplier, Employee and Customer is assigned a unique user id and password by the database administrator. Every person who login to the system has to put their user id and password to enter the system which solves the problem of authentication.
Authorization
Users are given access rights according their role.
1) Customers can access only customer table of database and they can only read data.
2) The users who are assigned the role of supplier has access to supplier tables and they can read as well write data in supplier table.
3) The users who are assigned the role of employee has access to employee table and can read data of employee table and can write data to only two columns of the table i.e. billing no and product id columns of employee table. The employees can also read and write data of customers table. Whenever they serve any customer , they will update data of the customer table. The employee also has access to product table. They can read and write data of product table.
4) The users who are assigned the role of owner has access to employee table , supplier table, customer table, product table, owner table. He can read and write data of all these tables.
5) The database administrators has access to owner table , customer table, supplier table, product table, employee table, roles table and transactions table. He can read and write of all the tables and he handles all the access permissions for various tables.
3) Problem of data loss or failure
Data loss or failure may occur at any time in the system due to human errors, viruses and malware , hard drive damage, Power outages, Computer theft, Liquid damage, Disasters ,Software Corruption, Hard drive formatting , Hackers and insiders (King, Halim, Garcia-Molina & Polyzois, 1991), So, it becomes very important to restore the original configuration of the system to prevent huge losses.
To solve this problem backup plan must be created. Full and differential backups of the system must be taken from time to time to restore original configuration of the system.
From these backups we can easily recover the whole data in shortest time.
Rationale behind transaction management plan, database security procedure , backup plan and Recovery model is to:
WORK TOGETHER WITH EXPERTSMIND'S TUTOR TO ACHIEVE SUCCESS IN TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT!
Transaction Management Plan
1) To name and assign valid category to every transaction so that there is no confusion to the users that which transaction belongs to which user.
2) To permanently save the changes done through transaction in the database to avoid the problem of inconsistency.
3) To follow the ACID Properties of transactions i.e. Atomicity, Consistency, Isolation, Durablity
4) To ensure no one transaction affect the other transaction.
Data Security Procedure
1) To prevent any unauthorized access to data of the retail store.
2) To provide authentication so that no intruder can enter the system and make changes in the data.
3) To provide access rights to the users so that only authorized users can write data.
Backup plan
1) To prevent the system from going standstill in case of data loss and failures due to hardware malfunctions, human errors, viruses and malware , hard drive damage, Power outages, Computer theft, Liquid damage, Disasters ,Software Corruption, Hard drive formatting , Hackers and insiders.
2) To provide recovery of data and to restore the system to its original configuration.
Recovery Model
1) To prevent the data loss in case of down time of system.
2) To get back the lost data and prevent losses
ARE YOU LOOKING FOR RELIABLE TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT HELP SERVICES? EXPERTSMINDS.COM IS RIGHT CHOICE AS YOUR STUDY PARTNER!
Database Administration Plan
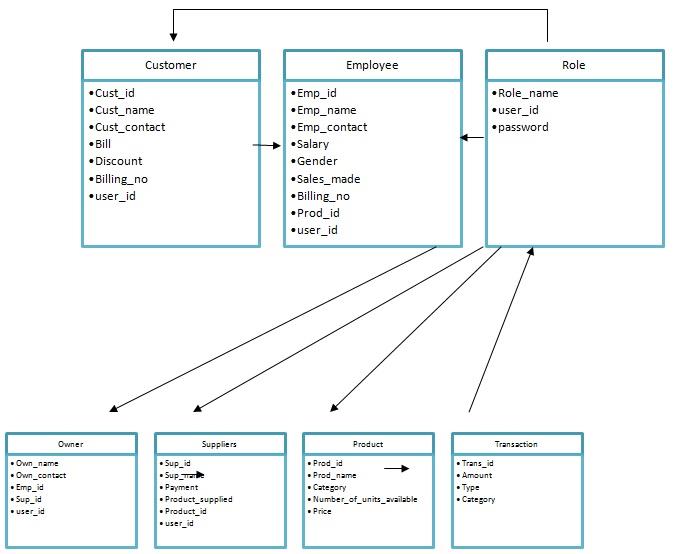
Figure 2:- Database Administration plan of Retail Shop
Transaction Management Plan
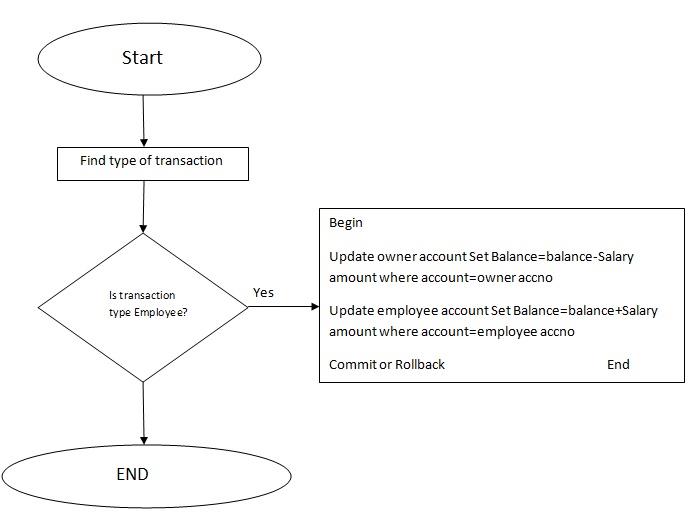
Figure 3 showing transaction management plan
Database Security procedure
1) Assign user id and password to every user.
2) If the user is
1) Owner :- Give access to employee table, supplier table, customer table, product table and owner table and rights of insert, update , modify and select to owner for listed tables
2) Supplier:-Give access to supplier table and rights of insert, update, modify and select to supplier for supplier table.
3) Customer:- Give access to customer table and rights of select to customer for customer table.
4) Employee:-Give access to Employee table, Customer table, Product table and access rights of insert , update, modify and select for customer and product table and access rights of select for employee table.
5) Database administrator:- He has all rights in all table include create , update ,delete etc . he also controls user id , passwords and access rights to all users.
SAVE YOUR HIGHER GRADE WITH ACQUIRING TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT HELP & QUALITY HOMEWORK WRITING SERVICES OF EXPERTSMINDS.COM
Backup plan and recovery Model
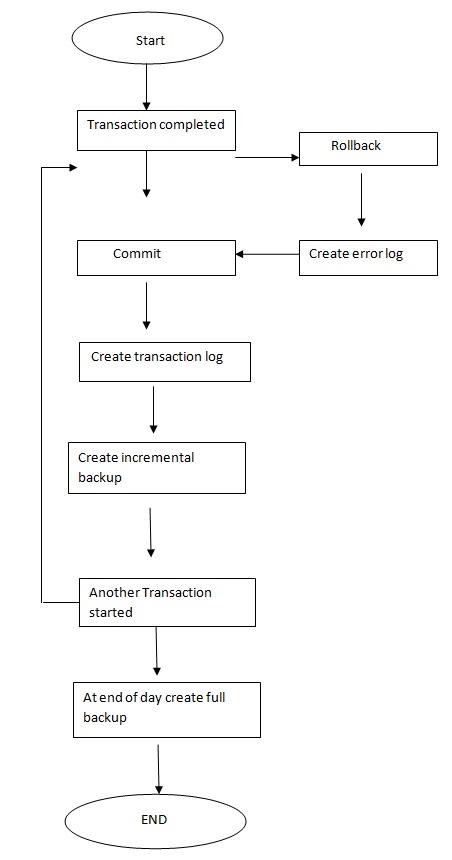
Figure 4 showing backup plan
Recovery model
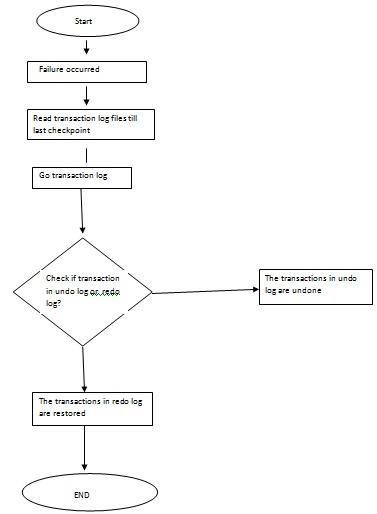
Figure 5 showing recovery model for retail store
CONCLUSION
This analysis helps in solving the problems of database administration of retail store, authentication and authorization of retail store and helps to recover data in case of loss of data due to network failure, disk failure and any other downtime situation.
DO YOU WANT TO EXCEL IN TECHNIQUES USED IN DATABASE ADMINISTRATIONS ASSIGNMENT? HIRE TRUSTED TUTORS FROM EXPERTSMINDS AND ACHIEVE SUCCESS!