GET BENEFITTED WITH QUALITY MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
MN623 Data Analytics for Intrusion Detection - Melbourne Institute Of Technology
Cyber Security and Analytics Assignment
Learning Outcome 1: Evaluate intelligent security solutions based on data analytics.
Learning Outcome 2: Analyse and interpret results from descriptive and predictive data analysis.
Evaluate one of the publicly available Network Intrusion datasets.
SAVE TOP GRADE USING MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Solution:
Introduction
In the respective report, there will be analysis of a given data and the process of data intrusion will be explained in a detailed manner. The data set chosen for this report is the UNSW-NB15 data set, it has been created by the IXIA Platform tool in an Australian Centre for analysing facts of Cyber Security. This was developed to fight the contemporary attacks done on data's and analyse the activities of normal activities to prevent the data intrusion. This type of data tool has been applied in various business filed to manage data such as in fields of business organisations and have been readily applied in the modern data intrusion techniques. Therefore, this study will generalise about the data set and the attacks on the set, which will solve by the data intrusion techniques and machine oriented solutions to solve the data intrusion activities. This will be concluded by the help of solutions which will help in providing security dataset.
1. Discuss all the attacks on your selected public intrusion dataset.
This data set was created in the raw form in the IXIA Platform tool in the Australian Centre for Cyber Security, which transformed into the formation of the hybrid network, to analyse the attacks on data sets in the modern era. Thus datasets have namely nine types of attacks, they are as follows:
• Fuzzers- it is an attack by which the attacker determines the loopholes, this can be solved by operating the system with a massive input of random data.
• Backdoors- it is attack which by passes the authentication in determining data, and this makes authorised access to the data set.
• DoS- this attack disrupts the computer data and information. This attack gets collided through the process of memory and then access the data.
• Exploits- this comes a line of commands which creates unwanted activities on the network.
• Generic- this attacks using the hash function and are used against block cipher
• Reconnaissance- also named as probe, which collects data to hamper the security controls
• Shellcode- acts as a malware to attack the whole system
• Worms- this acts a replica to spread throughout the system and hamper the security control.
This was solved by installing the Argus, Bro-IDS tool accompanying with two algorithms to help them generate 49 features with a class label. In the data set of UNSW-NB15 feature it was recorded to be more than two million and 540,044 data set which can be resolved by the usage of Argus, Bro-IDS tool. In another dataset named as UNSW_NB15 Training set and UNSW_NB15 testing csv file. It was recorded that there were 175341 training set and 82332 testing set.
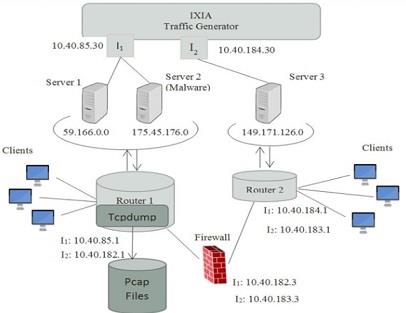
Figure 1: the data set testbed
In here the Tcpdumb Tool which was utilised by capturing 100 GB and helped in analysing raw traffic and helps in data intrusion, which will be described in the Pcap files. The further analysis was done on the various types of attacks which was described above.
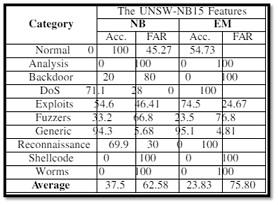
Figure 2: the cluster analysis of the UNSW-NB15 Data set
The data set is analysed by the ARM algorithm which is developed in the Visual Studio. The ARM technique has helped in featuring frequent itemsets and finding the strongest rules in te item-sets. The ARM helps in achieving the strongest item set, and this can be found with the support of the rule is more than the user specified minimum support
This technique is applied in two procedures; they are as follows:
• First, it helps in finding out iteratively in all the item set that are frequent by the calculation of sup>=minsup.
• Second, finding the rules that are associated with conf>= minconf. The algorithm for analysing it is given below:
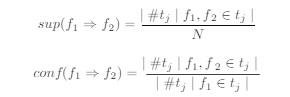
Figure 3: the algorithm of ARM technique for UNSW-NB15 Data set
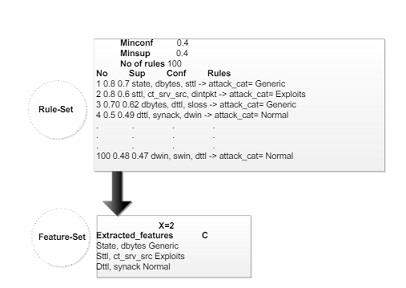
Figure 4: the feature selection through ARM selection
By the application of the techniques it has been demonstrated that the unsw-nb15 is a better featured dataset than the typical KDD99 feature and is much less complex[6]. It has been also stated that there are better tools and techniques for this type of data set to fight data intrusion, but the disadvantage is that the usage of decision tree cannot analyse its existing records, as there are many similarities in the records value.
DO YOU WANT TO EXCEL IN MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT - ORDER AT EXPERTSMINDS!
2. Perform intrusion detection using the available data analytics techniques using WEKA or other platforms.
The following process of intrusion detection has been shown below with the usage of the WEKA platform, they are shown below:

The initialisation has been done which uses Java and Werka.jar file
The loading of data has been done in the following step to perform the data intrusion
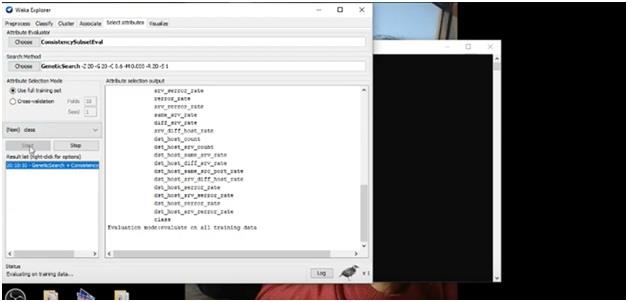
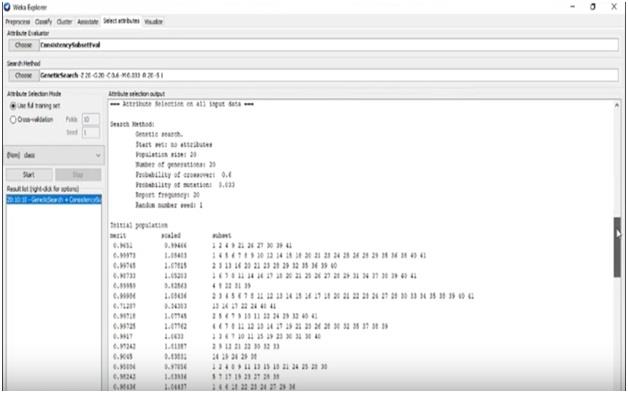
The data intrusion has been done by Genetic Search and Consistency Subset in the Weka platform, the systematic procedure has been given here. The classifiers used in the following report , it has been done according to J48, SVM and NAÏVE bayes classification.
Genetic Search are generally used in natural selection and the theory is totally dependent on the theory of Darwin's theory of survival to the fittest[5]. Intrusion detection in the genetic search has been done by extraction procedure which helps in scrutinising the weights from chosen data set.
DONT MISS YOUR CHANCE TO EXCEL IN MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT SOLUTIONS!
3. Choose at least three data analytic techniques for network intrusion detection and prepare a technical report. In the report, evaluate the performance of data analytic techniques in intrusion detection using comparative analysis.
There are mainly three types of data analytic techniques that can be used for data intrusion and that is
• Signature based detection
• Anomaly based detection
• Hybrid intrusion detection
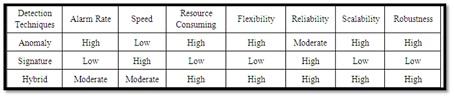
Figure 5: differentiation of selection techniques
4. Recommend the security solution using selected data analytic technique
• There should be large amount of heterogeneous data usage
• It should perform real time security analysis
• The application of anomaly detection can be useful in understanding the network intrusion or attacks on the particular dataset
Conclusion
The report has stated the data intrusion techniques along with the usage of anomaly techniques and ARM techniques. It has been resolved by the data intrusion procedures done in the Weka platform and have also been used in clearing out by the help of the algorithm. The training set and the selection procedures has been mentioned by the use of specific data analysis tools and have been demonstrated in the platform of Weka.
ORDER NEW COPY OF MN623 DATA ANALYTICS FOR INTRUSION DETECTION ASSIGNMENT & GET HIGH QUALITY SOLUTIONS FROM SUBJECT'S TUTORS!
Below are the related courses in which we offer Assignment Help Service:
- MN501 Network Management in Organisations Assignment Help
- MN621 Advanced Network Design Assignment Help
- MN603 Wireless Networks and Security Assignment Help
- MN601 Network Project Management Assignment Help
- MN502 Overview of Network Security Assignment Help
- MN692 Capstone Project Assignment Help
- MN624 Digital Forensics Assignment Help
- MN503 Overview of Internetworking Assignment Help
- MN623 Cyber Security and Analytics Assignment Help
- MN691 Research Methods and Project Design Assignment Help