IoT Research Report, Charles Sturt University, Australia
DO YOU WANT TO EXCEL IN IOT RESEARCH REPORT ASSIGNMENT - ORDER AT EXPERTSMINDS!
Question: Prepare an IoT Research Report on the given topic - Future Of The Fog Domain.
Answer: Milestone 1
Topic- Future of the fog domain
Format of the report: The study consists of four milestones. In the first milestone, executive summary of the report, selected topic and problem statement of the topic are discussed. It helps to understand the background and necessity for doing research regarding the topic. In addition, executive summary of the report is discussed in the first milestone.
In the second milestone, problem or challenges regarding the future of fog computing is discussed. Third milestone will cover literature review and annotated bibliography about the future of fog computing. On the other hand, fourth milestone consists of final report regarding the future of fog computing, which will be based on current works regarding the topic and brief explanation of techniques, issues and solutions used in past and present about fog computing. Problem Statement:
The Internet of Things is defined as the network of home appliances, vehicles as well as other items, which are solely embedded with software, electronics, connectivity as well as sensors and actuators (Mahmud, Kotagiri & Buyya, 2018). It assists enabling the objects connected and exchanging data. Embedded computing system has the ability to recognize everything uniquely. On the other hand, the capability of interpretation in the internet infrastructure exists previously. However, one of the major issues in cloud computing is that the users are reliable on cloud repository and data access, which demands for internet connectivity as well as allocating bandwidth. It generally comes with a major issue for affording the technology. On the other hand, security is one of the significant issues in cloud computing. The data are being lost or hacked within cloud. On the other hand, the technological world becomes the witness of the most interesting as well as extraordinary change in the data generated digitally from every type of connected devices along with smart things (Luan et al., 2015). The rises of applications as well as smart phones enable the data access and managing real time devices. For computing assists empowering the edge node devices in order to carry out local data processing and latency reduction that helps in obtaining better quality service.
On the other hand, cloud computing is considered as the most accepted technology for deliveringsuccessful hosted services based on internet. It assists enabling the organizations to consume data in computing resources such as virtual machines. In addition, the applications as well as storages are considered as the primary utility (Vaquero & Rodero-Merino, 2014). On the contrary, it is required to implement the system to mitigate computer security. Software related bugs as well as cryptanalysis are known as the algorithm. On the other hand, the rise of advanced web 2.0 applications and SaaS as the service that have eventually raised probability of attacking hidden channel attacks over internet. It also occurs during transmissions are generally encrypted between server as well as web browser.
The internet of things is one of the specific concepts in computing that eventually explains regarding the concept of several physical objects, which are connected to internet. Hence, the ability of identification of the devices of the devices is important in this aspect. On the other hand, fog computing is the advancement after the use of cloud computing. It includes control plane attack as well as data plane. The attacks are prone to several attacks where are the attacks are dangerous for fog computing (Stojmenovic & Wen, 2014). On the other hand, the data plane is known as forwarding plane. It is responsible to the process of forward traffic to subsequent hop that follows the path of wanted location network according to the control plane logic. On the other side, the packets are included in data plane process through the routers. The routers as well as switches use any control plane developed through disposing the outgoing and incoming packets along with frames. In this perspective, it becomes important to analyze the security issues in fog computing and find out solutions for overcoming the issues.
Executive Summary: The internet of things is important as any of the objects have the ability for representing itself in digital way. The information related time and additional power consumption and electromagnetic leakages are responsible for the type of attacks as the information is exploited. The most important issue in cloud computing is that the users of cloud computing is relied on cloud repository and data access. It requires internet connectivity as well as allocating bandwidth. It becomes a major issue for users, as the users are able coping up with the limitations. In addition, cloud computing is expensive and becomes a main issue for affording the technology. Security is considered as an issue in the cloud computing. The data are getting lost within cloud. On the other hand, computer security and hidden channel attack are the vulnerable attack, which are based on data. It is gained from deploying the process and the type of attacks that are eventually exploited. The rise of web 2.0 applications and SaaS software service has the probability of hidden channel attack. Hence, the research covers with finding the issues involved with cloud computing and provide appropriate solutions.
Milestone 2
Problem statement: One of the most important issues in cloud computing is dependency on cloud repository of cloud as well as accessing data. It requires connectivity of internet as well as allocating bandwidth. Hence, it becomes an issue for a user. In addition, cloud computing is expensive as well as becomes a major issue to afford the specific technology (Shin & Gu, 2013). Security is one of the major issues in cloud computing. The data are hacked in cloud that makes easy access of the devices. In this case, it would be helpful and dependent on cloud repository.
Structure of the report
Executive Summary
In this part of the report, concept of fog computing and its future will be discussed. In addition, what the report will cover will be discussed in this part.
Introduction of Milestone 2
In this part, overview of the milestone 2 will be presented.
Literature review regarding past and present work
This part of report deals with the literature review about current as well as previous work. In addition, theory and models related to the topic will be discussed.
Techniques/ solution/ issues: The techniques regarding the future of fog computing will be described in this part.
Best suited methodology: Amongst the discussed techniques or methodologies, the best-suited methodology will be described in this part.
Annotated bibliography: In this part, 5 articles related to the future of fog computing will be explained in this part.
Research findings: This part will cover findings of the research from above discussed part.
SAVE YOUR HIGHER GRADE WITH ACQUIRING IOT RESEARCH REPORT ASSIGNMENT HELP AND QUALITY ASSESSMENT WRITING SERVICES OF EXPERTSMINDS.COM!
Milestone 3
Article 1: References: Dastjerdi, A. V., Gupta, H., Calheiros, R. N., Ghosh, S. K., & Buyya, R. (2016). Fog computing: Principles, architectures, and applications. In Internet of Things (pp. 61-75).
Keywords- IoT, Internet of Things, Cloud of Things, Web of Things, IoT Applications, Fog and Edge Computing.
Fog computing process is a distributed paradigm of computing which is used for extending the capacities and services of the cloud at an edge of a certain network. This article is concerned with the Internet of everything which is providing solutions for every object of processing data and online. This also identifies the centralised cloud Technology which is not enough for the requirement of that environment. According to the explanation of this article, the main reason of this statement there is some application, but the impact of the performance can be measured in health monitoring and emergency responses. According to Bonomi, Milito, Natarajan & Zhu (2014), the cloud technology is slow enough latency which takes time in transferring data which is the reason for the performance. The cloud Technology has extended the age of its network for minimizing the effect of network congestion and latency. Fog computing has emerged. It is managed as the highly distributed computing process. The most possible virtualised environment is another factor of this computing technology. The main work area of fog computing services lies between the cloud data centers and sensors.
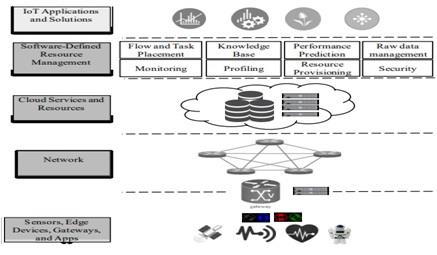
Figure 1: The Architecture Of Fog Computing
According to this article, the advantages of cloud computing is seen in the protection of network traffic, the internet of things queries and the task can be suitable is solved by this technology, scalability and low latency requirement. Except that, the architecture of Fog computing, the implementation of the fog computing within augmented reality, Healthcare, pre-processing and caching are discussed.
Article 2: References: Sarkar, S., Chatterjee, S., & Misra, S. (2018). Assessment of the Suitability of Fog Computing in the Context of Internet of Things. IEEE Transactions on Cloud Computing, 6(1), 46-59.
Keywords: Internet of things (IoT), Fog computing, service latency, cloud computing, carbon-dioxide emission and power consumption
This article focuses on developing comparative and rigorous analysis on the controversial paradigm of cloud and fog computing paradigm. The contexts which are selected are the internet of things where only formulation and mathematical approach of parameters is focused on the authors. It is stated by Giang, Blackstock, Lea, & Leung (2015), the traditional framework of cloud computing is facing challenges, and it is showing the dependency on cloud computing is affecting the massive amount of power as well as increasing the level of carbon dioxide in the air. But the use of fog computing is associated with latency sensitive application on the IoT. Utilisation of fog computing help in power consumption-carbon, dioxide emission, cost service, latency with internet connected device. A case study or research has been done on 100 populated cities in eight different geographical distributions. And the result of the entire investigation has shown that there is an enhancement in the real-time service application. In this process, the research also shows that fog computing paradigm is performing as an outperformer rather than the cloud computing process. Use of fog computing has minimised 50.09% environmental effect. And from this context, according to Waypa, Smith & Schumacker (2016), the application demanding for low latency services is the lower percentage at the time of using for computing rather than the traditional Cloud Computing process.
Article 3: References: Datta, S. K., Bonnet, C., & Haerri, J. (2015, June). Fog computing architecture to enable consumer-centric internet of things services. In Consumer Electronics (ISCE), 2015 IEEE International Symposium on (pp. 1-2). IEEE.
Keywords- Fog Computing, Smart Mobility, Connected Vehicles, Internet of Things;
The modern computing paradigm for computing and its customer-centric services is the central area of this research. There are various advantages of using for computing platforms which includes thick geographical distribution, open platform, proximity to the end users, high mobility support. But the mean area is the improvement of QoS and latency. All the internet of things application of this computing system is customer-centric, and therefore the real-time operations of this computing are increasing every day. According to Yannuzzi, Milito, Serral-Gracià, Montero & Nemirovsky (2014), the smart grid, connected devices and smartphone intersection management are the based operational areas still now. The primary purpose of this article is concentrated on how the architecture of fog computing is associated with M2M gateways and roadside units. M2m is mainly concentrated on smartphones and vehicles raw data which provide actionable intelligence. The distinct characteristic of fog computing is adequately measured by this article which is related to semantics management and discovery of connected devices. According to this research, all of these facilities of fog computing is customer-centric.
Article 4: References: Puliafito, C., Mingozzi, E., & Anastasi, G. (2017, May). Fog computing for the internet of mobile things: issues and challenges. In Smart Computing (SMARTCOMP), 2017 IEEE International Conference on (pp. 1-6). IEEE.
Keywords- Smart Cities; Internet of Things; Fog Computing; Edge Computing; Mobility Support; Service Migration
Internet of things is not only associated with everyday objects but also associated with the change of data into a process. In addition to that storing the data collecting them from the external and internal environment and the process of the intervention of the data is part of the internet of things. The change in the data storage process is seen where the cloud computing is changing into fog computing. Yi, Li & Li (2015) have described that the Fog computing can be best known as an edge computing ideal paradigm for the ultimate support of resource constrained. This support also helps in the information delivery and data processing. However, this article argued on the fog computing may not replace the centralised cloud computing process.
According to the research of this article Cloud Computing has its principles along with cloud two things Continuum. But the fog computing has the proximity to the internet of things devices. It also provides several advantages which are continuously enhancing the development of this area. The main three areas of investigation is the fog computing as well as IoT which has become the main direction of this research. The research area is the tourist as time travellers, drones of smart urban surveillance and citizen Healthcare. Finally, this study provides future research direction in several areas those are reactive v proactive service migration, fog Federation to enable mobile roaming, compliance with existing interpretability platforms, exploit contexts information to Trigger service migration, and visualisation and migration techniques.
Article 5: References: Kitanov, S., Monteiro, E., & Janevski, T. (2016, April). 5G and the Fog-Survey of related technologies and research directions. In Electrotechnical Conference (MELECON), 2016 18th Mediterranean (pp. 1-6). IEEE.
Keywords- 5G mobile communication, Cloud computing, Mobile computing, Internet of things, Computer architecture
The growth of smartphone all smart mobile devices is one of the most important areas of technological development. The mobile service providing organisations are trying to provide network like Broadband Internet. Therefore, According to Bonomi, Milito, Natarajan & Zhu (2014), for thinking about the development of networks 5G network development is one of the main concerns of these organisations.
However, this concept is going to impact on the life of the human, the digital society and economy. Because the Machines and devices will be developed because of these smart settings and the innovative tools will develop quickly. However, It is stated by Giang, Blackstock, Lea, & Leung (2015) that for this future internet process, the Machines and Technology have to be fast enough for adopting the runtime. Therefore, high mobility, production in latency, real-time execution is essential for this 5G network. The new fog computing superior Users experience which reduces the service latency improves the area of QoS and QoE. Therefore this study is associated with a survey including both the 5G as well as the fog computing technologies. Again the research directions have been analysed. The purpose is to lead beyond the 5G network in the fog computing.
Project deliverables: • Fog computing process is emerging because of its more advantages impact on the technological development. But the application of this technology is related to the Healthcare and Other industries where the transmission of data needs to be more faster than cloud Technology.
• One of the most advantageous aspects of using fog computing process is to reduce the environmental pollution and energy consumption. Therefore environment-friendly behaviour of this advanced technology is affecting the market of cloud computing process.
• The customer-centric service is developing benefits of using the fog computing process. The use like smartphone intersection management smart grid and connected device is taking the mechanism and internet of things a step ahead.
• The mobility support of three different areas by fog computing is changing the use of internet settings. The three areas include smart urban surveillance, tourist as time Travellers and citizen Healthcare. The challenges in using this technology need a proper mechanism in devices.
• Finally, the innovative idea of introducing a 5G network also need the smart settings for which the adaptation of fog computing process can be the future of the network development process.
ORDER NEW IOT RESEARCH REPORT ASSIGNMENT AND GET 100% ORIGINAL SOLUTION AND QUALITY WRITTEN CONTENTS IN WELL FORMATS AND PROPER REFERENCING!
Problem Statement: The cloud computing process is facing different difficulties related to the transferring time of data and environmental pollution. The use of this computing process is also affecting the energy consumption and serious environmental issues. Therefore the new advanced edge computing or fog computing may be a possible replacement of the cloud computing because of its customer-centric supporting process. But identifying the benefits will help the fog computing in replacing Cloud Computing process. The future application of the fog computing seems to be important for understanding before replacing the cloud computing which for the computing process.
Recommendations: The important understanding in using fog computing process is that this is the expansion of the cloud computing process. The use of cloud computing is avital part of information technology which has changed the total structure of data storage and information transformation. The advantages and beneficial impact of fog computing are currently proven as customer-centric and environmentally friendly. But the total replacement of cloud computing with fog computing process will not be a reasonable step of technological usage. Using both of these Technologies parallels will be helpful to properly examine the new fog computing process before increasing the dominance of this computing system.
Milestone 4: Executive Summary
The interface of fog cloud interface helps in providing several end to end services, which are involved in distributing cloud services in fog computing as well as appropriate collaboration of cloud based services. The study deals with finding out the issues involved in fog computing and provide effective solutions by which the issues can be mitigated or avoided.
Introduction from Milestone 2
Fog computing is the model included in cloud computing, where the resources are properly placed in order to deal with the establishment of connected devices. The applications of smart city such as predictive maintenance and health monitoring have introduced a new collection of stringent demands such as lower latency. On the other hand, the extensive of smart things provide unusual increase in digitally produced data. Hence, it becomes important to research the issues lied in fog computing and suggest probable solutions to overcome the issues. Fog computing is now considered as the extended part of the Cloud Computing process. In this research, the various area of fog computing will be properly understood to find out the future domain of this advanced technology. Hence, it is required to take proper actions to gain potential benefits from it.
Literature review: Fog computing is also considered as edge computing or fogging, procedures as well as accesses data rapidly, efficiently as well as minimizing risk of data latency. The devices as well as services develop internet of things (Shin & Gu, 2016). Data are not considered the issue. Fog computing aims in improvement of efficiency during minimization of the data amount sent to cloud in order to process, analyse and store data (Waypa et al., 2016). In addition, fog computing achieves the goal through keeping the data closer to ground in local devices, hardware as well as computers instead of directing data to a centralized data center in the cloud.
Benefits of fog computing: There are several benefits of fog computing like followed.
Privacy control: With fog computing, there is a better control of level regarding privacy. Fog computing helps in managing sensitive data can be processed as well as analysed compared to sending to a centralized cloud for analysis. Keeping procedure local, the team monitors, tracks as well as controls the devices collecting and storing data.
Increased productivity and agility of business: Fog computing assists in enhancing productivity as well as increase speed of business procedures. For instance, applications of fog computing flag data when the anomalies are present (Yi et al., 2015) They allow retrieval of data, which need immediate interaction with human compared to the all data minimizing time as well as efforts needed for finding possible issues.
Data security: It is considered as one of the vital aspects of business. The type of computing allows connecting several devices to a specific network. It makes easier identifying threats like infected files and possible hacks. Moreover, the threats are detected earlier as well as can be contained at the particular level of device instead of infecting or risking the entire network.
Limitations of fog computing: Although there are several benefits of fog computing, there are few limitations as well.
Confusing and complicated: The concept of fog computing seems complicated as well as confusing (Yannuzzi et al., 2014). A specific system including several devices can store as well as analyse own data, which could be located at any place and time. It also adds complexity to the network.
Increased connections: With several devise as well as users, the risks for corrupted and infected files, applications or data leaking into main data stream increased dramatically. The staffs probably don't utilize the devices for work that helps to increase possible risks to the device as well as the organization.
Information leaving the premises: Use of fog computing helps to store large volume of data. The devices are located outside physical location as well as several organizations or business managers feeling the increase of configuration in terms of risks of data breach.
Findings and conclusion: In light of the above discussion, it can be deduced that the fog computing is growing rapidly because of its various advantages and customer-centric applications. However, like the cloud computing process, this new fog computing will face challenging issues in its future development process.The technological world witnessed for most of the interesting as well as extraordinary changes in the processing of digitally produced data from connected devices (Yannuzzi et al. 2017). Fog computing assists empowering the edge node devices, which helps to carry out processing local data as well as minimization of better service quality. Hence, possible measures need to be taken so that its potential benefits can be obtained. In addition, there is any standard or comparative analysis in the process where IoT devices have an important par. In addition, computer security in the hidden channel attack as well as information gained through the process is based on the hidden channel attack (Roman, Lopez & Mambo, 2018).
The advancement of fog computing helps to develop several applications. Connected car is one of the applications that works as semi-autonomous as well as self-driving car that increase the huge amount of data created by vehicles. In addition, the cars can operate independently and has capability to analyse specific data in real-time. In addition, smart cities as well as smart grids such as connected cars and utility systems are utilizing the data to be more efficient in terms of running the systems. The data resides in remote areas can be processed through the channel. On the other hand, fog computing has a remarkable role in 5G computing. Hence, it is required to use the applications of fog computing, minimize the risks so that potential advantages of using fog computing can be obtained.
24/7 AVAILABILITY OF TRUSTED IOT RESEARCH REPORT ASSIGNMENT WRITERS! ORDER ASSIGNMENTS FOR BETTER RESULTS!
The cloud is becoming congested for more devices connecting to the internet. Implementation of fog computing can differentiate the data gained from the closed internet of things devices on the specific aspect that is time. The data that time critical includes alarm status, fault warnings as well as device status. Software bugs as well as cryptanalysis are considered as important algorithm. Additional power consumption, sound as well as electromagnetic leaks are exploited in this. In addition, development of the web 2.0 application has an important role in this. It generally occurs during transmissions are properly encrypted between server as well as web browser between server along with web browser. In addition, fog computing usually comprises with the control plane attack as well as data plane attack (Gubbi et al., 2013). There are several attacks where it is important to consider the process and develop the process of disposing the packets. There are also several attacks in the data plane, where it is important to consider the process and moved to the routers involved with the data plane. The major issue has been found where it is important to focus the vulnerabilities of attacks. Hence, it is important to analyze the problems involved with the use of fog domain.
Access our Charles Sturt University, Australia Assignment Help for related courses and major academic units such as -
- ACC100 - Accounting Assignment Help
- LAW220 - Business Organisations Law Assignment Help
- MGT100 - Organisations And Management Assignment Help
- MGT340 - International Management Assignment Help
- ITC105 - Communication And Information Management Assignment Help
- MGT230 - Ethics, Sustainability And Culture Assignment Help
- ITC354 - Routing And Switching Assignment Help
- QBM117 - Business Statistics Assignment Help
- ACC210 - Management Accounting Assignment Help
- LAW110 - Business Law Assignment Help