MN603 Wireless Networks and Security Assignment - Melbourne Institute of Technology, Australia
Assessment Title - Design and Implementation of Secure Enterprise Wireless Network for an Apartment Block
The purpose of this assignment is to design and implement a secure enterprise wireless network, considering the ethical implications. The assignment covers the following Unit Learning Outcomes:
- Apply and evaluate wireless network security techniques in consideration of ethical implications;
- Design and implement secure enterprise wireless networks.
Design and implement a secure enterprise wireless network for an apartment block, considering the ethical implications and the requirements of a modern apartment block.
ORDER NEW DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT AT NOMINAL PRICE!
Answer - Wireless Networks and Security
Introduction
Nowadays our system architecture is based on two networks such as WLAN (Wireless local network) along with LAN (local area network). This system network works only when all the devices are linked together which are in network. Though such services cost more the results are good. If all the devices are connected through WLAN (wireless local area network) it becomes easy to work. Such services make industrial work easy and more productive. User can do many new things when they are near the WLAN as they are connected to an internet network. In big companies, WLAN services are provided all over the campus so that all the users can work easily. As this network system provides many good things simultaneously there are changes of system break down, important data might get lost. In order to secure the network, outsourcing is done through a RADIUS system. This Radius system encodes the data in such a way that WPA2 data gets fully secured. They use IEEE-802-1x standard setup, these works when they are well connected to the internet. Along with IEEE 802, EAP helps to work in a network system. The user needs to verify its framework through a RADIUS system. This is a work of server along with other AP devices such as Laptop, mobile. These devices provide authentication to the system. This case study based on secure networking system.
Q1. Explore the ethical implications in the design and implementation of a secure enterprise wireless network for an apartment block.
Ethical implications in the design
In order to focus on a complete computer network system needs to be serviced. Persons working independently must take permission from the preferable network system. This assignment is dependent on each other for the proper execution of work. Database breaks down, theft all these has been increasing as everything is localized. A company needs to develop a strong network system. In order to follow government clause, it has to follow certain logic to secure the data. There is some system developed by governor clauses.
Hence our motto is to develop such a network to protect the network system. The developed system is to be developed in such a way that it should be flexible enough to handle by everyone. Employees working in the same network should not face any kind of difficulties while working on a network. A flow less design needs to be developed so that when all the computers are well connected in a network it should not get disconnected and anyone can work from anywhere of the company. As all the computers are connected to common server data becomes accessible for everyone. A system is developed in such a way that it should have a broad bandwidth and can be connected to the World Wide Web i.e., WWW along with the internet. This network is designed in such a way that it should be trustworthy. IT network is developed for the smooth functioning of person, organization, and business. There is always a chance to break down, this network system helps to secure a complete IT system.
GET BENEFITTED WITH QUALITY DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Q2. Identify and analyse the requirements of an apartment block, considering the issues of multi dwelling and justify the use of WLANs in this scenario.
Requirements
Our case study depends on a university campus according to their requirements. We will be working on a trustworthy along with security. With the help of IEEE level, we will meet the expectation. The main intention of the IEEE level is that each and every corner of the university campus should be accessible. We are providing with a complete wireless network so that person using the network should not face any difficulties occurred in the campus network. We need to develop a secure and safe database for the protection of data of the network. If any unknown user wants to access the data that should not be possible a system needs to be developed in such a way. Without networks permission, no one can be able to access the network. In the network, we might find many hackers who will try to break down or steal data. We need to protect from them. This can be executed by increasing the bandwidth of the computer network system. Access will be provided only to a reliable user. In this case study, we tried to meet the universities need and requirements and an increase in the university network.
Q3. Design a secure enterprise wireless network for an apartment block, employing a standard industry tool.
Network Design
Here we have makes the network design. This network design is made by the client requirements and this network design is decided on the company's growth. This network design is based on the company's growth; it is used in the future.
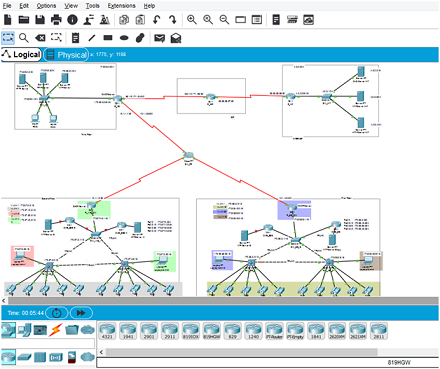
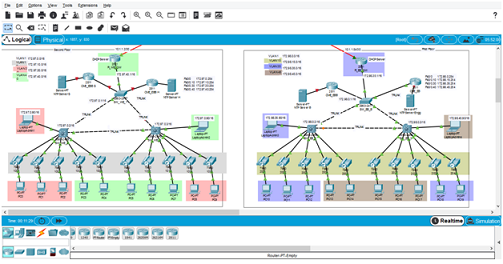
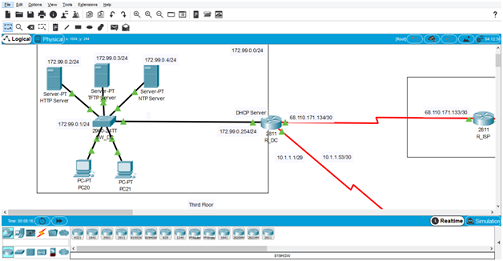
Network diagram
First floor and Second floor
Third floor
Justification:
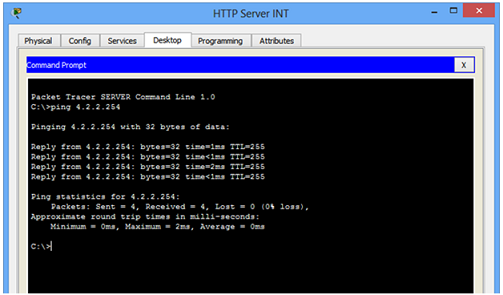
Authentication: Authentication is to see if the construction system is correct. Here the system that has been developed completes the expected rationale and meets the user for which it has been developed. Here we have executed the validation process at the end of the entire work. Use of such authentication is used to see if the system has achieved the intended use. This shows the purpose of the meeting and the client's need.
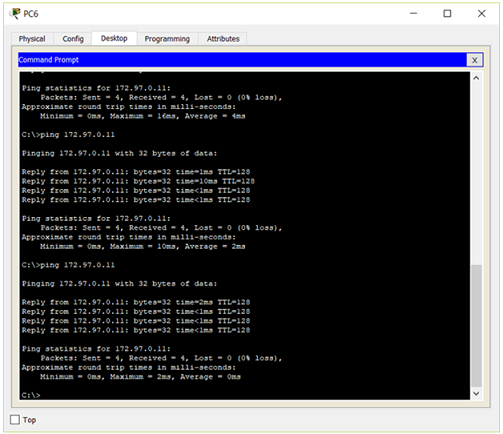
PC6
ORDER NEW COPY OF DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT & GET HIGH QUALITY SOLUTIONS FROM SUBJECT'S TUTORS!
Q4. Analysis of the secure enterprise wireless network using WPA2 and the RADIUS server, considering the following aspects:
Analysis of the secure enterprise wireless network
Wi-Fi is the wireless security mechanism and it is protected to access WPA enterprise or enterprise for small to medium (or extra large) enterprise wireless networks. This is the WPA security protocol by using the advanced encryption and authentication.
Confidentiality
In the IT sector, the database is the most important thing in the company. A strong network system is developed to secure the data. So that it should not be used by any other unknown person. A well-balanced database system has been developed so that without permission no other person can access the data. Data distribution is done according to the requirement of the user and a good safety measure is taken. Limited access is provided to a person. Limited permission is given according to the work and designation. Some privacy is developed which will protect data theft and can be recorded. If any mischievous things appear in the system alert will show. So that safety measures can be taken to lesser data theft risk. There are various types of protection used by different users. A sample is created to understand the user. This sample provides the information regarding protection such as protection through password etc. the campus needs to be secured. Such privacy-related rules which can protect sudden damage are done in this assignment. Campus communication needs to be secured. All the information is stored in the form of coding which is the best way to secure the data. Safety measures are made such as biometric authentication, allotting tokens, etc. The main purpose of our case study is to protect and secure the data.
Integrity
Our data is said to be safe and secure when it is been used by a permitted user. Data handling should be done very minutely. To maintain the quality of computer network data is very important. Whenever the next person is using the computer network it expects the quality of data. To provide the best quality of network-wide bandwidth is required. The user expects a flawless internet connection for better performance of the activity and to work easily. It becomes very important for us to maintain the good quality of the network. A student (user) can be able to work on network with permission from the security service. To increase the website traffic user need to be satisfied so that a large number of people can access the website. Here the majority of the users are students who use book and videos to large extents. Students take advantages as well as disadvantages of the network provided to them. It become very important to control the unwanted activities and encourage the positive things on the campus. Network security plays a vital role here in controlling. No user can theft the data and should not be able to harm the network system. All these activities are performed under the system network management. The wireless network made up of waved radio and signals of a microwave. Routers connect all the WLAN points centralize so that every point is well connected to it. A router helps to change the Local area network to WLAN. Though the wireless devices are connected to router but router is cabled to wire modem. When all the computers are in WLAN is becomes easy to work as they are well connected to each other.
SAVE TOP GRADE USING DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Availability
Network availability is the term which relates to the quality of being able to be used. When the student who is the major user in the campus needs to be provided with the quality of network along with time. User can be able to access the network from any corner of the campus with the same speed. A high degree of quality of network availability is maintained by parallel processing along with communication changes. To provide better availability it needs monetary help. Campus needs to be flexible and trustworthy to develop better network quality. When the network system is maintained very well then the accessibility of more network is always seen. Computer network needs updates to form higher resources for updated changes such operations are performed by doing an audit in the computer network. Every network develops its own kind of availability hence it should be maintained regularly. Regular maintenance of the network to increase the bandwidth and better availability. All the network system is dependent on cables and routers; some are directly connected to cables or connected wirelessly. In the campus buildings, trees and like other hurdles may occur, hence it should be maintained regularly.
Privacy algorithm- when all the network computers are connected in a network they use WI-Fi network which is totally wireless and gives wide bandwidth for network. Hence it reduces the cost of cabling in USA based workshops. In a country like Europe Compared frequency distribution network is needed. Many famous hospitals prefer wireless network system. Computers in hospitals are made connected to each other wirelessly such networks are found in nonresidential areas.
Security
An important term in computer science is Security. This helps to protect the system from unusual theft and problems. It reduces network risk and breaks down. Security provides proper permission to the user according to the requirement. For smooth functioning of network security plays a very vital role.
Privacy
A Protected network will always provide you relief. Any data stored in the network is important to one or else. That needs to be secured by using network design. Any computer which is not protected can damage the whole network system. In the campus all the data is related to students, college and other administrative work, both are very important and their data too. In college campus, online work is performed and crossed checked with the use of paperwork. So system privacy is a very important and crucial part of the system. Network security is maintained by providing limited access to the user. Various privacy plans is developed in order to reduce the problems. Attacks are of two types
1. Internal attack
2. External attack
These attacks are categorized depending on their activities. The attacks which are performed in the system are called as internal and the attack which is observed outside is called an external attack.
These attackers take care of the attacks which are occurring in the system. An attack can occur at any time without any one's knowledge. Such attackers are not good for the system. Security is indirectly proportional to Privacy. Privacy is very important in the organization as it is directly related to security services. Poor security can damage the system soon whereas strong security system will protect it.
DO YOU WANT TO EXCEL IN DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT - ORDER AT EXPERTSMINDS!
Q5. Implementation of a secure enterprise wireless network using WPA2 and the RADIUS server for an apartment block.
WPA2 is the protected Wi-Fi network which takes care of the safety of the network by increasing the level of security by a wireless network. Here the wired network uses the cables that are connected with the devices like computer, laptop or desktop over the internet or another network. Here the wireless networks allow many devices which are connected over the network. For connecting to the network the router is important to access over the network.
Modify the Default key (Password)
Password is provided to secure the system and is given to all the users by default. All the users are requested to modify the given password with the combination of alphabet, numerical values, and numbers.
Network Close
A system called service set identifier (SSID) helps to maintain the safety of the system. This SSID comes into the frame when the network proceeds to close. It secures the system and protects from the system theft.
RADIUS
Remote access dial-up user service helps to use the system network. It is provided with id and password which provided limited access. Before entering in the system RADIUS checks the credentials and then allows to access.
Q6. Demonstrate the network security against attacks.
Testing and verification
Karli Linux Metasploit is provided network security service. To control the network one more device is used called as snort and Wireshark. To control the traffic and protect from hackers and damage to the system. This is the open source project and it is maintained by the offensive security. It provides security to test network errors. And it provides penetration testing and security training services. Here the Karli Linux also provides the security that maintains the Metasploit unleashed and exploits database. Here the Linux includes the metapackages that is used for the software-defined radio, password cracking, web application, wireless and number of the application. This Linux is easy and quick to define metapackages. Kali Linux is used for the testing. Here the Karli Linux helps to control the network one or more devices are used called Wireshark.
Conclusion
This case study is about university computer network, RADIUS server, and WAP2. The concept of computer security is studied here. The relation between privacy and security is very well explained. In campus wireless computer network has implemented and executed with authentication from the administration. IEEE 802.1 is the basic thing to develop a wireless local area network. This helps to connect the devices wirelessly. There are some local area connections such as LAWN this is also termed as WLAN. WLAN is abbreviated as Wireless local area network. CSMA/CA and Ethernet protocol are used by 802.11 levels. Carriers sense multiple is the full form of CSMA/CA, this is made up of encryption method and make pathway distribution works easy.
DON'T MISS YOUR CHANCE TO EXCEL IN DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN DESIGN AND IMPLEMENTATION OF SECURE ENTERPRISE WIRELESS NETWORK ASSIGNMENT SOLUTIONS!
We at Expertsminds offer best Melbourne Institute of Technology, Australia Assignment Help service for different units, such as -
- MN404 Fundamentals of Operating Systems and Programming Assignment Help
- MN405 Data and Information Management Assignment Help
- MN501 Network Management in Organisations Assignment Help
- MN502 Overview of Network Security Assignment Help
- MN503 Overview of Internetworking Assignment Help
- MN504 Networked Application Management Assignment Help
- MN506 System Management Assignment Help
- MN507 Overview of Software Engineering Assignment Help
- MN601 Network Project Management Assignment Help
- MN621 Advanced network Design Assignment Help