GET ASSURED A++ GRADE IN EACH BN305 SSL VPN TECHNOLOGIES ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!
BN305 - Virtual Private Networks - Melbourne Institute of Technology
Assignment - SSL/TLS VPN Technologies
The purpose of this assignment is to review existing literatures on important VPN technologies and issues and write a report.
1. You need to explain the significance of VPN for contemporary organisations. This should cover the different encryption protocols for VPN implementation, including a comparison of SSL/VPN and IPSEC/VPN.
2. IPsec uses the Internet Key Exchange (IKE) protocol to negotiate and establish secured site to-site or remote-access VPN tunnels. Investigate how Cisco Adaptive Security Appliances (ASA 5500 Series) would support IPsec and IKE.
3. Discuss the role of VPN in supporting the security of businesses, and describe the advantages of SSL/VPN over IPSEC/VPN
4. The rapid proliferation of mobile devices increases on a daily basis, investigate how Cisco AnyConnect is designed to secure the connections from these mobile devices.
HIRE PROFESSIONAL WRITER FROM EXPERTSMINDS.COM AND GET BEST QUALITY BN305 SSL VPN TECHNOLOGIES ASSIGNMENT HELP AND HOMEWORK WRITING SERVICES!
Solution:
Introduction
When we communicate through the any internet mode first we have to analysis the security of information. Today many hackers are available for interrupting the messages. So the hackers easily identify our messages and use it for another purpose. In such cases we have to concentrate on the security while using internet facilities. Now a day many technologies are available for securing the information while transferring. In this assignment we have to analyse those techniques and it will be processed under the various categories. For that to analyse the significance of VPN for the various protocols and how the authentication is maintained for the various process involved in that. During the file access hoe it control and the way of maintaining the confidentiality and integrity are discussed here[1].
Literature Review
The following research results shows that what are the different kind of method available for securing information while transferring through the internet.
a. Explain the significance of VPN for contemporary organisations
Significance of VPN
The virtual private network mostly used for the communication in online. It uses the public network's infrastructure to make the connection in geographically. Instead of using cables it create the private network for communication. The significance of the virtual private network in the organization is maintained relationship among the employees. That is communication among the employee, the client and various comments are done using VPN technology. The virtual private network make the information are safe while transferring. It reduce the security risk of various cyber-attacks.
Encryption protocols for VPN implementation
When we click the link which is available in the internet the request passes to the server and get back the correct information from the corresponding server. When we use the VPN in our process the all the request is routed first through the private server. Like previous process it transfers the information but the website hold the VPN provider address only.
The following protocols are available for the VPN implementation
• OpenVPN
• L2TP/IPSec
• SSTP
• IKEv2
• PPTP
OpenVPN
It is the open source protocol. It is one of the most secure protocols. It allows the customer to protect the data using AES bit key encryption method.
L2TP/IPSec
It is the widely used protocol. The speed is very high. During the transmission it is easily blocked due to the reliance on the single port usage.
SSTP
It is very security protocol. During the transmission of information the blocking and detect is very difficult.
IKEv2
It is very fast working protocol. It is mobile friendly usage. It is supported with the several open source implements.
PPTP
It is also fast working protocol. It is widely supported to the user. But it has the full of security holes. So it is using only the web browsing and streaming purpose only[2].
ENDLESS SUPPORT IN BN305 SSL VPN TECHNOLOGIES ASSIGNMENTS WRITING SERVICES - YOU GET REVISED OR MODIFIED WORK TILL YOU ARE SATISFIED WITH OUR BN305 SSL VPN TECHNOLOGIES ASSIGNMENT HELP SERVICES!
Discuss the role of VPN to support the security of businesses
Cisco Adaptive Security Appliances
The IPSec uses the internet key exchange protocol to establish the secure site to site information.
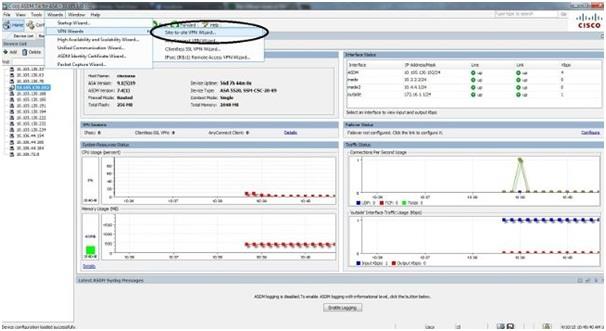
This diagram shows that the navigation the site to site VPN wizard.
The Adaptive Security Appliances makes the use of the IPSec tunnelling standards to create the secure connection among remote users. The Adaptive Security Appliances functions as the tunnel end point. It can receive the various packets from the private network and analysis sends the packets into the various level of security.
Adaptive Security Appliances uses the IPSec for the LAN to LAN connectivity and provide the various connections to the customers on the different task. It builds the security association for the various tasks that will be analysis produce the encryption method. That encryption support and gives the security for the customer.
The hashed message authentication method codes (HAMC) to ensure the identification of the sender and also ensure the message that has not been modified then transmit the process.
The role of VPN in supporting the securityof businesses
When we use the VPN in our process the all the request is routed first through the private server. Like previous process it transfers the information but the website hold the VPN provider address only.
Even the secured internet connections are hacked by the hacker. So we have to concentrate on the various method involved in the antivirus process. The VPN produce the end to end encryption of the all the data that is transferred in to the sender. It products the sensitive customers and their information and other secrets of the organization will be protected using the VPN. It supports safe and secure data sharing, remote data access, avoid the international censorship, setups and costs.
Advantages of SSL/VPN over IPSEC/VPN
|
Features
|
IPSec VPN
|
SSL VPN
|
|
Network Layers
|
It performs at layer 3
|
It performs at layer 4 - 7
|
|
Connectivity
|
It entirely connects the remote host to the entire network
|
It connects only the user which is specific to the process.
|
|
Applications
|
It can support all the IP - based applications.
|
It cannot support all the IP - based applications. but suitable for the email, file sharing, web browsing process.
|
|
Gateway location
|
The gateway is usually deployed on the firewall process.
|
The gateway is usually deployed behind the firewall process.
|
|
Security control
|
Broad access to the security concerns access.
|
More controls for the more management process.
|
|
End points
|
It supports the host based clients.
|
It supports with Browser based with optional user requirements.
|
Cisco AnyConnect
Now a days mostly all people are used mobile phone for the all the purpose. That is mainly internet oriented activities. During this type situation how the cisco design the anyconnect design for secure access[4].
MDM solution
Every time the user use the device for transferring process it try to attempt the MDM tool and the follow the process.
Cisco ISE
After the MDM it evaluate the mobile devices security and policies which related to the all the devices.
Cisco AnyConnect mobile client
The employee who is wishing to access their service in the intranet mode they have to download and install anyconnect form the Cisco eStore. It supports the various secure connections using the IPsec internet key exchange and the important security socket layer protocols. It is connect using ASA authenticates mode then encrypt the data stream.
HELPING STUDENTS TO WRITE QUALITY BN305 SSL VPN TECHNOLOGIES ASSIGNMENT AT LOW COST!
Authentication and Access control
Browser communicate to the right server
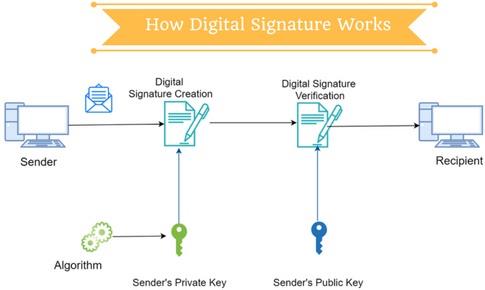
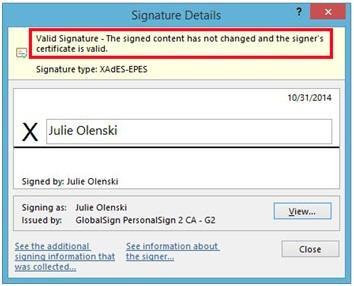
The SSL and the TLS provide the various to authenticate the server linking process. For it requires the client authentication then the server verify the identity of the client. It is done by verify the digital certificate with respect to the public key of the CA[5].
The personal certificate is process to the customer security. If the both client and server authentication is need means the server have to perform the following task. Here the client is B.
• The personal certificate has to issue to the server by CA of B
• Then generate the private key for the server
Then SSL or TLS clients requires CA certificate for the process of CA B.
If the SSL and the TLS needs client authentication, the personal certificate is process to the customer security. If the both client and server authentication is need means the server have to perform the following task. Here the client is A.
• The personal certificate has to issue to the server by CA of B
• Then generate the private key for the server
• Then CA certificate checked to CA A client.
Then SSL or TLS clients requires CA certificate for the process of making the chain processing to the root of CA certificate.
GET READYMADE BN305 SSL VPN TECHNOLOGIES ASSIGNMENT SOLUTIONS - 100% PLAGIARISM FREE WORK DOCUMENT AT NOMINAL CHARGES!
Confidentiality and integrity
The confidentiality of user information is maintained using the SSL security process. The SSL secure the data in the various level of process. It uses the combination of the symmetric and asymmetric encryption to validate the message originality. During the communication of the SSL with server and the client it accept the encryption of the algorithm which is to convert then it shared the secret key which is created for using in the one session[6].
After that is encrypted and transfers again it is checked the message is private. The SSL supports the wide range of the various cryptographic algorithms which is used to secret key. The SSL use the Asymmetric encryption for the sharing process of the secret key.
The integrity of the data is founded by the message digest process. The cipherspec is used maintaining the integrity of the data through the hash algorithms. If the algorithm is marked as none it is not suitable for maintaining the security of particular process.
VPN Client software options
There are following client software of VPN are available.
• Ios Version 10
• Andriod Version 6
• OS X 10.11 El Caption
• Windows 7 and Windows 10
• Other Open source software.
MOST RELIABLE AND TRUSTWORTHY BN305 SSL VPN TECHNOLOGIES ASSIGNMENT HELP & HOMEWORK WRITING SERVICES AT YOUR DOORSTEPS!
Anti - Replay
Using SSL wee make the information sharing is very secure. But in some cases it will be not allowed. Because some hackers hack the information and then transform it for various purpose.so finally the original message cannot be received to the customer[7].
That is replay attack the information through using the packet sniffer for the intercept the data related to the use information. The anti - replay supports the various data that related to the various task.
It is the sub protocol of the IPSec. So it is avoid the hacking process. That is internet engineering task force support to avoid hackers injection of the various task involved in the message transferred by the sender. The anti - replay protocol uses the unidirectional security association for the establishment of the secure connection between sender and the receiver. The anti - replay protocol uses the packet sequence number for the attack processing. That when the source sends the message to the destination it first set the sequence numbers then it validates the receiver packet if the packet having the lowest sequence number it will be rejecting. Then it will accept after the packet evaluated.
Remote Access to database server
The remote access to the data base of business is supported for the secure information process.
• It allowing the employee for accessing their customer database from the home.
• Then setting a project workspace where ever the client required to process.
• It allows the employee to access their email that sends and receive the email from any computer.
It makes easy for the people to make their work very easy manner. Before the remote access starting process it is evaluate whatever wants.
Possible attacks
The most of the website attacked done by the various hacker used for information gathering
• Password attack
• Malware
• Ransomware
• DDos
• Inside attack
• APT
• Phishing
These are attack possible to attack the information for the purpose. It will be avoided using various methods involved.
Conclusion
Using VPN technology analysed, those techniques and it will be processed under the various categories. For that information to analyse the significance of VPN protocols and the authentication is maintained for the various process involved in that. During the file access it control and the way of maintaining the confidentiality and integrity are discussed.
SAVE DISTINCTION MARKS IN EACH BN305 SSL VPN TECHNOLOGIES ASSIGNMENT WHICH IS WRITTEN BY OUR PROFESSIONAL WRITER!
Get our Melbourne Institute of Technology Assignment Help for the below mentioned courses like:-
- BN104 Operating Systems Assignment Help
- BN204 Database Technologies Assignment Help
- BN109 Web and Multimedia Systems Assignment Help
- BN202 Internetworking Technologies Assignment Help
- BN103 Platform Technologies Assignment Help
- BN110 Information Systems Fundamentals Assignment Help
- BN200 Network Security Fundamentals Assignment Help
- BN108 Programming for Networking Assignment Help