BN305 Virtual Private Networks Assignment - Secure Network Design and Implementation, Melbourne Institute of Technology, Australia
Learning Outcomes -
- Describe architectural VPN design for small, medium and large businesses and corporations.
- Report on the health of the existing VPN architecture, solution, data, application, and technology.
- Discuss the appropriate security design and solutions for varieties of organisations.
- Report on the current and future state of the management of VPN infrastructure and its technologies.
- Interpret a roadmap process to transform the VPN architecture to support long- term organisations' goals.
- Implement a process to support the administration and the management of VPN.
ORDER NEW BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT AT NOMINAL PRICE!
Task - Investigate, design and develop a suitable VPN network for a fictitious company in Australia (CyberVision Inc.).
1. Design a network for CyberVision Inc.
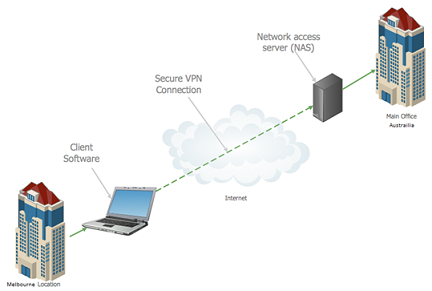
2. Build VPN services for the users. The network solution would be built on a simulator (such as Packet Tracer or NetSim) and include establishing a VPN from remote site to main branch in Sydney.
Answer - Virtual Private Networks - Secure Network Design and Implementation
Introduction
CyberVision Inc. is an invented organization in Australia and at present working in Sydney. As of now CyberVision Inc. is intending to extend their tasks in Melbourne. we have been contracted to dissect different choices and build up a VPN organize structure so the two locales can be associated safely and effectively . This is notwithstanding remote clients who ought to have the option to get to their work from the organization site while going for business reason and taking every necessary step
Fundamentally a virtual private framework (VPN) expands a private framework over an open framework, and enables customers to send and get data transversely over shared or open frameworks just as their figuring devices were really connected with the private framework. Applications running on a figuring device, for instance a workstation, work region, mobile phone, over a VPN may in like manner benefit by the value, security, and the officials of the private framework. Encryption is a normal anyway not a trademark bit of a VPN connection.[1]
Virtual private network advancement was made to allow remote customers and branch work environments to get to corporate applications and resources. To ensure security, the private framework affiliation is developed using an encoded layered tunneling show and VPN customers use affirmation methods, including passwords or supports, to get to the VPN. CyberVision Inc. is hoping to widen their endeavors in Melbourne. we have been contracted to investigate different choices and build up a VPN sort out structure so the two locales can be connected safely and effectively.In various applications, Internet customers may secure their trades with a VPN, to go around geo-imprisonments and oversight, or to interface with delegate servers to guarantee singular identity and region to stay secretive on the Internet.
GET BENEFITTED WITH QUALITY BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM!
Regardless, This is notwithstanding remote clients who should have the choice to get to their work from the affiliation site page while going for business reason and making each imperative walk a couple of destinations square access to known VPN development to thwart the circumvention of their geo-controls, and various VPN providers have been making frameworks to get around these hindrances.
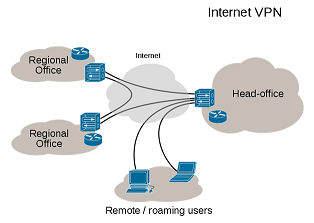
We can connect two or more remote networks using the VPN as shown in example below
Scope and limitations in VPN
We can understand the scope and limitations of the VPN using the following criteria as
Scope
- Upgraded security - The information is kept encoded and verified when you interface with the system through a VPN. Thusly, it wards off the data from programmer's eye.
- Remote control - One of the greatest focal points of having a VPN is that the data can be evaluated remotely even from home or some other spot in the event of organization. Along these lines, VPN expands the efficiency inside an organization.
- Offer records - If you have a gathering that requirements to share documents for quite a while period, at that point a VPN administration can be utilized.
- Online obscurity - The web can be perused in complete secrecy through a VPN. Contrasted with web intermediaries or IP programming, VPN administration enables you to get to the two sites and web applications in complete lack of definition.
- Sidestep channels and unblock site - VPNs demonstrates to be incredible for bypassing Internet channels and getting to blocked sites.
- Change IP address - VPN is useful when you require an IP address from another nation.
- Better execution - Efficiency of the system and Bandwidth can be expanded once there is a usage of VPN arrangement.
- Decrease Costs - The support cost is extremely low once VPN organize is made. When a specialist organization has decided on you then the observation and system setup is no more a worry.
- Business Research - Businesses alongside restrictive data wouldn't like to offer an opportunity to the programmers to get to basic information. VPNs can likewise permit workers a safe arrangement and an unknown online encounter for encoding on the web interchanges.
ORDER NEW COPY OF BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT & GET HIGH QUALITY SOLUTIONS FROM SUBJECT'S TUTORS!
Limitations of VPN
Beyond so many advantages the VPN network has various limitations also as defined below:
- A definite comprehension of cautious arrangement/establishment and system security issues is required to guarantee ensure satisfactory confirmation on an open framework like the Internet.
- The presentation and enduring nature of an Internet-based VPN are not under direct control of an affiliation. Or maybe, the plan depends upon an ISP and their organization quality.
- Prior, on account of issues with VPN advancement benchmarks, the VPN things and plans from different dealers have not for the most part been great. An undertaking to mix and match apparatus may cause specific issues and the usage of equipment from one provider may not give as unimaginable a cost hold reserves.
- Slower VPN speeds could transform into a factor, dependent upon a switch, its set-up and different related contraptions to a switch. It is for each situation better to endeavor two or three different VPN servers to test which will reveal to you the best servers as shown by your necessities.
Requirements for building VPN network
To agree the network for a practical VPN, diverse different segments are required at various walks in transit - from the client, through the cloud, to as far as possible and into huge business frameworks. What do you need to set up a VPN? These are the principal VPN requirements and parts:
- User VPN programming to make an ensured for the remote affiliation.
- Hubs and Switches that think about the VPN and firewalls to permit bona fide VPN rush to pass unhindered.
- User's network VPN mechanical assembly, concentrator or server to manage and administer drawing nearer VPN traffic and to set up and direct VPN sessions and their passage to sort out resources.
SAVE TOP GRADE USING BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM!
Solution Design
Logical design
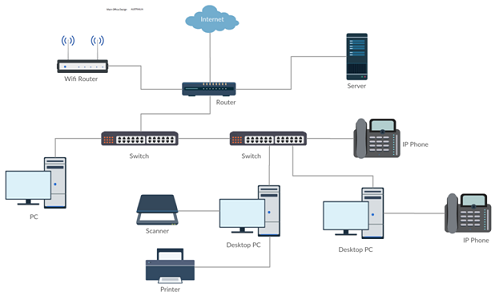
Physical Design for VPN network
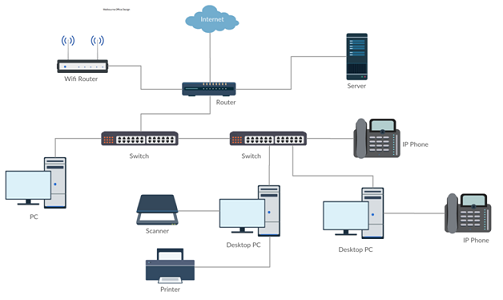
The Physical design will be same for both thee offices that is main office and the Melbourne office.
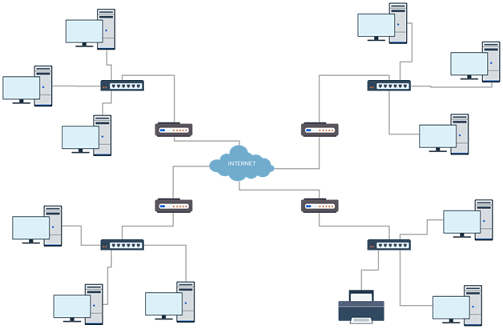
As shown below all the hardware devices will be connected through the internet and will work efficiently.
Melbourne Office design will also be same as they will be interconnected with the VPN through internet
Topologies
The topology will be used as shown below for both the offices
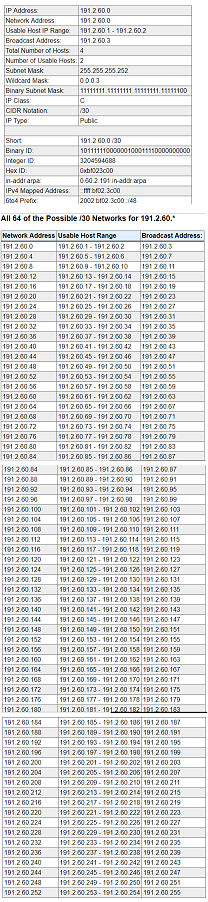
IP addressing is done as with subnet mask and all other requirements as Ip address is taken as 191.2.60.0
Security features and policies
The security features and policies are:
- Center usefulness: File encryption and document get to blocking
- UX approach implementation: Restricting duplicate/glue, drag/drop, and sharing tasks
- WIP organize arrangement implementation: Protecting intranet assets over the corporate system and VPN
- System strategy implementation: Protecting SMB and Internet cloud assets over the corporate system and VPN
DO YOU WANT TO EXCEL IN BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT - ORDER AT EXPERTSMINDS!
Redundancy and Failover plans
A VPN is a system that utilizes the mutual open media transmission foundation to associate hubs and set up secure access between the Internet and an association's inward system. VPN associations empower associations to likewise have secure associations over the Internet with different associations, which are arranged in topographically various areas. A VPN association over the Internet, capacities as a different WAN connection. VPNs can isolate the system traffic of the shifted client bunches over a basic system and give solid security highlights.
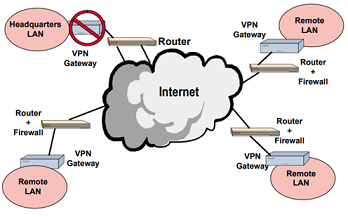
VPN, as a private system keeps up protection through utilizing security techniques and burrowing conventions. In light of the burrowing idea, the burrowing convention (AKA Encapsulation convention) is a system innovation that incorporates setting up and keeping up a sensible system association. The most broadly utilized VPN burrowing conventions are, Layer Two Tunneling Protocol (L2TP), IP Security (IP Sec), and point to point network is configured for the failover plan to overcome the failure.
Deployment
1. Assemble necessities Port numbers and classes of clients Areas and servers
2. Get upper dimension the executives included
3. Decide innovation and items
4. Introduce a proving ground
5. Measure the frameworks
6. Structure security and VPN arrangement
7. Decide update system
8. Introduce and design
9. Screen and oversee and change as required
DON'T MISS YOUR CHANCE TO EXCEL IN BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN BN305 SECURE NETWORK DESIGN AND IMPLEMENTATION ASSIGNMENT SOLUTIONS!
Get our Melbourne Institute of Technology, Australia Assignment Help services for below mentioned courses like:-
- BN301 Industry-Based Project Assignment Help
- BN303 Wireless Networks and Security Assignment Help
- BN321 Advanced Network Design Assignment Help
- BN309 Computer Forensics Assignment Help
- BN311 IT Security Management Assignment Help
- BN223 Cyber Security Principles Assignment Help
- BN323 Ethical Hacking and Security Governance Assignment Help
- BN324 Enterprise Cyber Security and Management Assignment Help
- BN314 System Architecture Assignment Help
- BN315 Enterprise Architecture Assignment Help
- BN322 Software Defined Networking Assignment Help