BISY2002 Information Systems Networking Essentials Assignment - Australian Institute of Higher Education, Australia
Unit Learning Outcomes -
- Describe and discuss the key functions and various elements (routers, modems, etc.) of modern computer networks (LANs, WANs, and wireless networks).
- Design, configure, build, and troubleshoot a simple/basic local area network (LAN).
- Identify and critically assess key security and data verification issues related to the creation and maintenance of computer networks.
This report assesses a student's ability to assess information, formulate arguments and critically evaluate different alternatives to issues or problems.
DO YOU WANT TO EXCEL IN BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT - ORDER AT EXPERTSMINDS!
Answer -
Executive Summary
The report will discuss about the key functions and the elements of the modern computer network which will highlight about the different elements like the router, modem for LAN, WAN and the wireless network. It will also highlight about the designing, configuration, building and easily handling the LAN network to identify and then assess the key security issues with data verification issues. It is related to the creation and the maintenance of the different computer networks. The computer network is considered to be the collection of the computers, printers and the other equipment which includes the collection of the data with the communication with each other. The network standards are based on the formal standards with the network layer software with the organizations focusing on the including the International Organization for Standardization.
Introduction
The research has been on the networking standards where there are computer and the network to provide the effective solution for the hosts and then handling single network. The effective technology for the business aims to focus on increasing the productivity through planning about the right networking standards and then handling the business to be competitive with increased productivity and the costs of hardware. The hierarchical model design is important for the LAN network which can help in providing a better information and resources through easy sharing and providing a better security implementation.
SAVE TOP GRADE USING BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM!
Key Functions and Various Elements of Modern Computer Networks LAN, WAN & Wireless Network
There are different components and the equipment which help in working together. There are network infrastructures that help in providing a stable and the reliable channel for the communication. It comprises of the end devices, intermediary devices and the network media. there are different elements which includes the laptop, PC, switch, router, modem etc (Chow et al., 2017). The network components are based on providing the services and processes which are important to run on the networked devices. It helps in providing a better information, depending upon the email hosting services and the web hosting services. The services provide the functionality that directs and moves the messages in the network.
There are end deices for the hosts which help the computers, network printers and the VoIP phones to work on the security cameras or the mobile handheld devices. The host devices are for the sources and the destination of the message which is transmitted in the network. The host can work as the client or the server. The servers are considered to be the host where the software tend to enable and provide the proper information and service like the email or the web pages to be hosted.
The processes are based on handling the classification and the direct messages through the QoS priorities and then permitting or denying the flow of data (Chow et al., 2017). The network media is the medium of the channel that helps in providing with the different interconnection of the devices that is through setting the network representations and then displaying the devices or the media in the larger network frame.
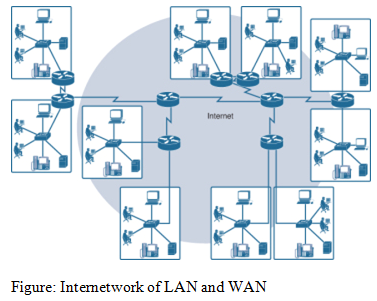
LAN is the Local Area Network which is able to provide the access to the different users and the end devices in a particular geographical area. This is interconnected to the end devices which is set in the limited area mainly of the school, office and the building area. It is mainly administered through the single organization and the individual which is based on controlling and then governing the security or the access control policies. LAN is able to provide the higher speed bandwidth for the internal end devices with handling the intermediary devices. LAN has been including the sharing of the data and the tools which are able to handle the connection to the computers with the devices that are connected by the switch or the private addressing schemes which are set by TCP/IP protocol. The private addressing is based on the computers for the local networks with routers that have been able to find the connection which is larger than WAN. The data tend to be transmitted with the faster rate with number of computers linking. The connections are done at a higher speed with the inexpensiveness of the hardware like the hubs, network adapters and the ethernet cables. They are found to be easy for the designing and communication (Nieet al., 2015).
WAN is the Wide Area Network which is able to provide the complete access for the network for the wider range of the geographical standards. They are able to handle the span of the wide geographical area where there are management of the service providers or the Internet service providers. There are different features where WAN is able to handle the geographical standards in between cities and the states or the provinces. There are different administered multiple service providers and so WAN leads to the slowing down of the speed links in between LANs. The connection tend to overextend with the larger geographical area that is confined with bounds and then handling the radio waves as well. There are switched WAN and Point-to-Point WAN that are found to be difficult to design and maintain. The fault tolerance of WAN is less and then there is a network congestion as well. WAN data rate is about 10th LAN speed which involves the increased distances and the increased server and the terminals as well. The speed of the WAN tend to range from the kilobits per second to the megabits.
DON'T MISS YOUR CHANCE TO EXCEL IN BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT SOLUTIONS!
The Internet is important for the benefits of the LAN and WAN where there are individuals who are able to communicate and then plan the resources which is based on the other network (Wu et al., 2015). The planning is done to ensure about the wider collection which is defined through handling the interconnected networks of information. It includes the use of common standards and through the telephone wires, fiber-optic cables or the wireless transmission where the users are able to exchange the information for the different forms of variety.
The internet has been of the networks which includes the planning and then handling the diversification of the infrastructure where the applications are consistent to handle the technologies or the different standards as well. There are forms of the organization which are working on maintaining the structure and the standardization of the protocols with the proper processes. It includes the different terms like:
a. Intranet: It is about the private connection of the network of LAN and WAN that helps in properly designing the accessibility by the organization. It helps in giving the authorization and then only accessing from the organization. They are able to publish intranet web pages with internal events, health and the other safety policies, which includes the class scheduling information or the other curriculum. This will help in eliminating the paperwork and then speeding up to the workflow. The organization Intranet has been working on the organization with the secured connection for the internal network.
b. Extranet: They are for providing the secured access to the individuals where there is a need to work on the different organizations. It requires the company data with handling the access to outside suppliers and the contractors. The hospital is able to provide the booking system for the doctors who tend to make the appointment with providing the education about the budget and the personnel information for the schools who are in the district (Chen et al., 2015).
Connecting to the Internet: Focusing on the different connection to the users, the organization tend to work on the home users, teleworkers and the small officers which require to set the connection to ISP with accessing the Internet. The connection options are for the variations depending upon how the ISP and the geographical location is able to choose the different standards. It works on the different internet connection options which includes the small and the home office users like:
a. Cable: They are able to handle the cable television service providers with the internet data that is for the signal which is carried through the use of coaxial cables and helps in delivering the cable television. With this, there are higher bandwidth of the data with always-on connection that is for carrying on the cable and providing the ethernet connection.
b. DSL has been able to provide with the higher bandwidth where there is always-on connection. It helps in providing a better connection through providing the channel to handle the voice calls without any disconnection from internet. The quality and the speed is based on the faster downloading of the channel which is able to receive the information from internet (Visser et al., 2017).
WORK TOGETHER WITH EXPERTSMIND'S TUTOR TO ACHIEVE SUCCESS IN BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT!
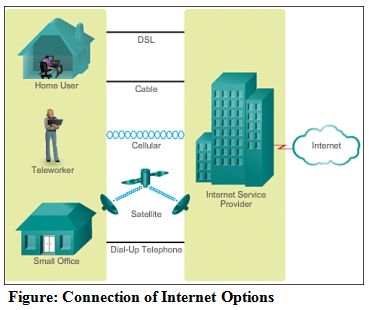
The connection of the business to the internet is based on the management of the services with connection options that are related to the organizations including:
a. The dedicated leased line: This is coming from the service provider to handle the customer premises. With this, there are reserved circuits with the connection that comes with the separated offices with private voice and the networking. The circuits with the rented that tends to make it expensive.
b. DSL: There are different formats which includes the symmetric planning with the same upload and the downloading speed. ADSL is about handling the delivering with the bandwidth that is found at the different rates with different range from 1.5 to 9 Mbps (Feghaliet al., 2016).
The modem is considered to be the device which is able to handle the transmission of the data over the telephone or the cable lines.
Router is able to handle the devices which carries the forwarding of the data packets along the network. Here, the connection is for the twice of network and then it is located at the gateways as well where there are placed about connecting the network at two or more positions.
Design & Configure a Simple LAN
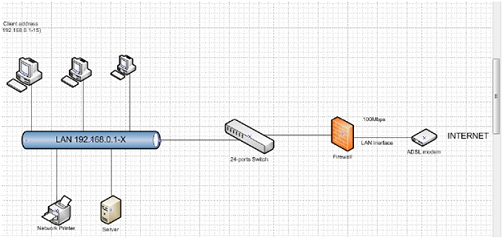
The network topology is for the laboratory work which includes the different effective operations which are consisting of the modem, switch PCs, firewall and the other connecting cables.
The application includes the installation of the Windows 7 OS on host computers where there are network that is bridged for using the local environment that is completely different from the network of the school. Hence, they are worked upon on VMWare.
ARE YOU LOOKING FOR RELIABLE BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT HELP SERVICES? EXPERTSMINDS.COM IS RIGHT CHOICE AS YOUR STUDY PARTNER!
Assess-key security and data verificationissues
The security policies for the LAN network is based on the exchange of the resources and then planning about how the network is able to ensure the transactions. They are set for working on protecting the network and then planning the needs for the security policy guidance. It will help in serving the organization network with policy statement that includes the protection and the integrity for the educational data and the other proprietary system. They tend to ensure about the data availability and the programs which are defined for the authorization of the users and the members of the staff.
The assessing of the internet and the other external services need to be authorized at the personnel only. It includes the authorization which includes the installation and then working over the passwords which are given by the administrator for the log0in and then focusing on the changing after they have been logged into it. There are cases related to the hardware and the software replacement measures which includes how the measures need to be taken for handling the drives or the other removable media from the different resources (Ren et al., 2018). The users needs to also fill the network log with monitoring it and then handling the performance based on detecting the performance. The server and the workstations are protected from the virus threats with scanning the software and the tasks are considered important for the system administrator. The users need to be informed for the security policies and the procurements where the virus infection and the users shall report to the administrator for the prevention of the effects of multiplication.
Firewall: They are considered to be handling the multiple networks with the communication that is done to one another. They are for handling the focus on protecting and managing the investments where the organizations are deemed to protect the network. There are devices which are generally protected and then ensured about the proper security (Koptiet al., 2015). The LAN offers the resource sharing and it offers a wider degree of the network to secure the operations. There are different solutions of the security in the network with centralizing the security solutions. Hence, there are workstations which are able to handle the installation of the software-based firewalls along with protecting them against the threats which are coming from the threats or the internet. The windows firewall is including the Windows 7 OS where there is a need to prevent any of the unauthorized planning of the traffic to be passed through firewall. With this, there are software based and the hardware-based software which are able to handle the designing to guide the computer and then handle the general network planning as well. There is a need to plan about handling the blocks as well.
Network Address Translation: This is the Internet Protocol which works on the RFC planning and then handling the devices of the network like the firewall. It helps in assigning different orders and address for the public in the private network where the aim is to focus on NAT and then reduce the different public IP address of the private network. NAT has been seen to be important for the hosts with private IP address to access public network like the internet. There have been network address ranges which comes from 10.0.0.0-10.255.255.255. Here, the network is used for the common implementation with use of the private addresses as well. The effectiveness is based on planning about the resources and then handling the different schedules of the pool of addresses which helps in hosting the use for translation when the hosts are set in the network (Indovinaet al., 2015).
NAT is able to focus on the concepts related to the firewall security where the measures need to be taken for the private IP address and the public address as well. They are for the communication with the internet and then providing or allowing the strict measures of access to the different resources.
SAVE YOUR HIGHER GRADE WITH ACQUIRING BISY2002 INFORMATION SYSTEMS NETWORKING ESSENTIALS ASSIGNMENT HELP & QUALITY HOMEWORK WRITING SERVICES OF EXPERTSMINDS.COM!
Conclusion
The research has been on the networking standards where there are computer and the network to provide the effective solution for the hosts and then handling single network. It helps in enabling the easy backup of the facilities with the subject of working that includes the field of application. The topology is important for the grouping of the hosts by function and then implementing the security standards as well (Manel et al., 2017). It includes the network address planning which is to be carried by the hosts and the network devices. The VLAN can be configured through the Cisco switches which tend to berunning with reducing the broadcasting domains and then allowing the groups or the users to group without any need of being physically located at the same place.
Get our best Australian Institute of Higher Education, Australia Assignment Help services for different courses and academic units such as:
- BISY1001 Professional and Ethical Practice Assignment Help
- BISY1002 Database Management for Business Assignment Help
- BISY1003 Foundations of Programming Assignment Help
- BISY2001 Systems Analysis & Design Assignment Help
- BISY2002 Information Systems Networking Essentials Assignment Help
- BISY2003 Object Oriented Programming Assignment Help
- BISY2004 Project Management Assignment Help
- BISY2005 Enterprise Systems Assignment Help
- BISY2006 Management Information Systems Assignment Help
- BISY3001 Data Mining & Business Intelligence Assignment Help
- BISY3004 E-Commerce & E-Business Applications Assignment Help
- BISY3005 Knowledge Management Assignment Help
- BISY3006 Information Security Assignment Help