ENDLESS SUPPORT IN RESEARCH METHOD - CYBER SECURITY ASSIGNMENTS WRITING SERVICES - YOU GET REVISED OR MODIFIED WORK TILL YOU ARE SATISFIED WITH OUR RESEARCH METHOD - CYBER SECURITY ASSIGNMENT HELP SERVICES!
NIT6130 - Introduction to Research - Victoria University
Assignment - Proposal, Literature Review, Research Method, Ethics
Solution:
Proposal, Literature Review, Research Method: Cyber Security
Abstract
Today's world is heavily dependent on the Cyber grid and naturally with such dependency comes the issues regarding their security. Hence cyber security is a massive field of research and innovation, currently. This research highlights the current challenges and the limitations into the field of cyber security. This paper presents a theory-based literature review of the current scenarios into the word of cyber security. The paper follows a qualitative approach for a deeper and intricate understanding of the research. A field with constant changes of requirements needs to be understood in a deeper level, thus the mentioned approach was selected. A research methodology is described as an organized or hypothetical method functional to a ground of study or research.Thus the mixed research approach seems best suited for the research. The research is aimed at understanding the limitations of the cyber world. Concluding, an intricate level of understanding and the ways of overcoming the current limitations are the prime objective.
Introduction
The threats in the field of cyber security are real and growing with every possible moment. Allocating effective resources are difficult as the field itself is evidently new and grows complex and unpredictable with every passing moment. In this ever changing world of cyber grid, everything we know and understand changes with every moment. The current cyber world faces numerous threats as there are very limited number of threat remedies and people who are already a part of the grid are not well informed enough about the threats they are prone to. More or less nowadays everyone is a part of the cyber world, somehow or the other, however rarely do they know the everlasting threats they might be facing even without them being present onto the world.The cyber security research needs to cover a full spectrum of possibilities as the term itself may sound tiny but in reality it does cover a huge magnitude of the cyber world, from security policies to security tools.
NEVER MISS YOUR CHANCE TO EXCEL IN RESEARCH METHOD - CYBER SECURITY ASSIGNMENT! AVAIL AFFORDABLE AND RELIABLE RESEARCH METHOD - CYBER SECURITY ASSIGNMENTS HELP SERVICES OF EXPERTSMINDS.COM
Related work
The research needs the appropriate and an effective support of resources for the understanding and improvement thus the mixed methodology approach is best suited to put on an enhanced perceptive of the connections and the contradictions between the cyber world and the threats related to them (Nassar, Thom & Parry, 2016). The policies and distinctive characteristics of cyber security are multidisciplinary and hence global, accordingly an array of research documents, organizations, and academic personals needs to be taken into account for providing a much more trustworthy cyber system to the people (Knowles, Prince, Hutchison, Disso, & Jones, 2015). Research can help bring up the level of play between the attackers and the security provided to the target as it is also an important way for ensuring a better scope of allocating better security to people. The cyber security research needs to cover a full spectrum of possibilities as the term itself may sound tiny but in reality it does cover a huge magnitude of the cyber world, from security policies to security tools. A clear research would push forward the fundamental understanding and developing newer and better ways of encryption for driving forward the field of cyber security. An attacker or an intruder needs just a single vulnerability for a successful attack and a system of network may remain vulnerable unless all are fixed and thus a detailed research is always reasonable.
As discussed earlier the methodology selected for such a research is the approach of the mixed methodology. That is, both methods quantitative and qualitative would be taken into account for the research. The approach of mixed methodology was taken into consideration in regards to the undefined complexity of the research, allowing the researchers to discover the relations between the intricate layersbetween the cyber world and the targets. Mixed methodology approach requires a meaningful mixing between method implications and data collection (O'Brien, Jacobs, Pasquali, Gaynor, Karamlou, Welke, & Jacobs, 2015). The most important step in a mixed methodology approach is data integration or data linkage, which needs to be applied at an appropriate stage of the research.
According to the journal ‘Progress and research in cybersecurity: Supporting a resilient and trustworthy system for the UK'.The cyber world has already transformed our world in humongous manner and will continue to transform our world in ways never seen before. From social networks to self-driving cars, the field itself has no boundaries for innovation. The UK government well understands that and has very smartly placed itself into this field, hence the government can hugely benefit from it (Stoddart, 2016). The UK government has a huge amount of resources to utilize into the field and eventually this may ensure trust into the target audience.
Cyber security developments
The cyber world is a never constant, ever changing world and the research deals with the current implications of security measures related to the cyber world, ie Cyber Security. The point to focus on is the policies and applicable measures to ensure an individual's security into the cyber grid.
The main focus of the research is to understand the basic needs to keep an individual safe online and educate people of the threats they are dealing with, without their knowledge. The field of cyber security is vast given the growth rate it currently is maintaining as according to an article, ‘There is a hacker attack every 39 seconds' , hence it is high time to step up to the game and provide the necessary information and help to the people who need it.
The research being basically an insight to the real world matter which needs to be addressed and needs to be overcome, it would provide the information which would in turn help people get educated into the matter and thus help people know their dos and don'ts. However this research would provide just some hard research facts in regards to pre held researches and current records and according the world needs to act (Gheyas& Abdallah, 2016).As already discussed the approach best suited for this research would be that of the mixed approach and eventually taking qualitative and quantitative approach into account.
DO WANT TO HIRE TUTOR FOR ORIGINAL RESEARCH METHOD - CYBER SECURITY ASSIGNMENT SOLUTION? AVAIL QUALITY RESEARCH METHOD - CYBER SECURITY ASSIGNMENT WRITING SERVICE AT BEST RATES!
Architecture Diagram of Proposed Method
The architecture diagram for the proposed security measure is given in the diagram below,
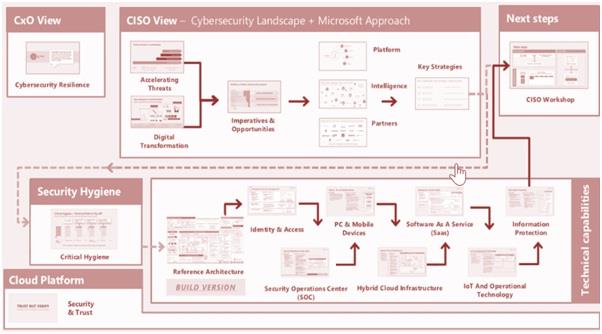
Figure 1: Security Design for Cyber Security
The security design for the implementation of the cyber security would be done considering the CxOthat involves the cybersecurity resilience. The security would be done for enduring the management of the works and the security work alignment. The cyber security development would be done for enabling the accelerating work alignment and forming management of the works. The cyber security would be done for ensuring the management and information management. The continuation of the security alignment would be done for enabling the management of the works. The design development would be done for enabling the works and managing and continuation of the security management. According to reports the gap in the education about cyber security, there would be a vast number of unfilled jobs in the field of cyber security worth 3.5million by the year 2021. Hence the first thing that needs to be met is the minimization of this huge gap of information and this research has been conducted to battle this very scenario.Hence cyber security is a massive field of research and innovation, currently.The current cyber world faces numerous threats as there are very limited number of threat remedies and people who are already a part of the grid are not well informed enough about the threats they are prone to. More or less nowadays everyone is a part of the cyber world, somehow or the other, however rarely do they know the everlasting threats they might be facing even without them being present onto the world.
Implementation Design
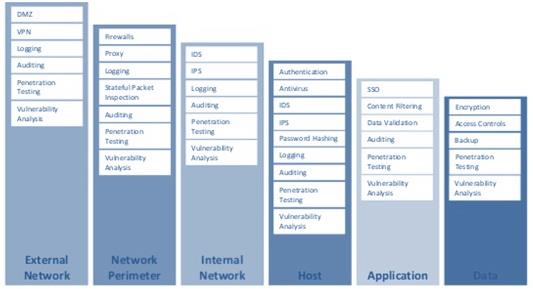
Figure 2: Implementation Design for the Cyber Security
The design of the security would be done for enduring the management of the works and the design of the security work alignment. The cyber design of the security development would be done for enabling the accelerating work alignment and forming management of the works. The cyber design of the security would be done for ensuring the management and information management. The continuation of the design of the security alignment would be done for enabling the management of the works. The design development would be done for enabling the works and managing and continuation of the design of the security management. The current cyber world faces numerous threats as there are very limited number of threat remedies and people who are already a part of the grid are not well informed enough about the threats they are prone to. More or less nowadays everyone is a part of the cyber world, somehow or the other, however rarely do they know the everlasting threats they might be facing even without them being present onto the world.According to reports the gap in the education about cyber security, there would be a vast number of unfilled jobs in the field of cyber security worth 3.5million by the year 2021. Hence the first thing that needs to be met is the minimization of this huge gap of information and this research has been conducted to battle this very scenario.Hence cyber security is a massive field of research and innovation, currently.
HIRE PROFESSIONAL WRITER FROM EXPERTSMINDS.COM AND GET BEST QUALITY RESEARCH METHOD - CYBER SECURITY ASSIGNMENT HELP AND HOMEWORK WRITING SERVICES!
Preliminary study/proof of Implementation
In a typical scenario the target generally does not know about the system vulnerabilities and hence the person does not know or feel the need of taking any precautions beforehand. As some research suggests most attacks, precisely, 64% of organizations have faced web based attacks and in most cases the organizations were not even aware of them and worse, they weren't even prepared for such a scenario. ‘158,727 per hour, 2,645 per minute and 44 every second of every day' reports Cybersecurity Ventures
Use any programming outputs
public RreadFileBuffered(
InputStreamHandler handler
) throws IOException {
try (final InputStream in = Files.newInputStream(path)) {
handler.handle(new BufferedInputStream(in));
}
}
public R locked(Action action) {
lock.lock();
try {
returnaction.run();
} finally {
lock.unlock();
}
}
public void writeFile(
OutputStreamHandler handler
) throws IOException {
try (final OutputStreamrawOut = Files.newOutputStream(path)) {
finalBufferedOutputStream out =
newBufferedOutputStream(rawOut);
handler.handle(out);
out.flush();
}
}
public void bufferedWriteGzipFile(
OutputStreamHandler handler
) throws IOException {
try (
finalOutputStreamrawOut = Files.newOutputStream(path);
finalOutputStreamcompressedOut =
newGzipOutputStream(rawOut);
) {
finalBufferedOutputStream out =
newBufferedOutputStream(compressedOut);
handler.handle(out);
out.flush();
}
}
Highlight the expected improvement in the outputs produced
Screenshots of the preliminary study/programming output
Conclusion
In conclusion it is safe to say that the cyber security world has a huge field of improvement and the current practices and policies are without any doubt, flawed to a certain extent. With the current rate of research and innovations to defend people are alarmingly low to the current growth in the rate of attacks people face every day. According to reports the gap in the education about cyber security, there would be a vast number of unfilled jobs in the field of cyber security worth 3.5million by the year 2021. Hence the first thing that needs to be met is the minimization of this huge gap of information and this research has been conducted to battle this very scenario.Hence cyber security is a massive field of research and innovation, currently. This research highlights the current challenges and the limitations into the field of cyber security. This paper presents a theory-based literature review of the current scenarios into the word of cyber security. The paper follows a qualitative approach for a deeper and intricate understanding of the research. A field with constant changes of requirements needs to be understood in a deeper level, thus the mentioned approach was selected. A research methodology is described as an organized or hypothetical method functional to a ground of study or research.Thus the mixed research approach seems best suited for the research. The research is aimed at understanding the limitations of the cyber world. Concluding, an intricate level of understanding and the ways of overcoming the current limitations are the prime objective.
MOST RELIABLE AND TRUSTWORTHY RESEARCH METHOD - CYBER SECURITY ASSIGNMENT HELP & HOMEWORK WRITING SERVICES AT YOUR DOORSTEPS!
Listed below some of the major courses cover under our Victoria University Assignment Help Service:-
- EPM5600 Principles of Project Management Assignment Help
- NIT6150 Advanced Project Assignment Help
- NIT5110 Networking Systems Assignment Help
- NIT5081 Fundamentals of Cyber Security Assignment Help
- NIT5083 Enterprise Security Management Assignment Help
- NIT6130 Introduction to Research Assignment Help
- NIT5082 Cloud Security Assignment Help
- NIT5130 Database Analysis and Design Assignment Help
- EPM5700 Project Management and Information Technology Assignment Help
- NIT5150 Advanced Object Oriented Programming Assignment Help