KIT711 Network Security Techniques and Technology Assignment - Data Network Security, University of Tasmania, Australia
Goal - To design and write the security policies for a small to medium enterprise
The task is to produce a printed consultancy report that is for establishing the security provisions for an organization described in a case study.
Your task is a creative process requiring everything to be imagined to achieve a realistic view of the company to understand its needs and threat profile.
Consultancy Report - The report will have two sections: the first will contain information common to the entire report, such as the threat and risk analysis, while the second section will address specific security issues facing the company.
EXPERTSMINDS.COM ACCEPTS INSTANT AND SHORT DEADLINES ORDER FOR KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT - ORDER TODAY FOR EXCELLENCE!
Answer - Consultancy Report: TechOn Company
Section 1 -
Executive Summary
TechOn firm will apply the various number of technologies in its reputation for Smart Homes. This organization is primarily pioneered for this particular industry and therefore it is expected to achieve a number of accomplishments. Additionally, it is our expectation that it will have received various forms of prizes by the end of this year in the accomplishment and engagements of its task. The organization will have two offices in Tasmania, whereby the head office will be located in Hobart and the other branch will be located in Launceston. The firm will be involved in providing supplies to various businesses through the use of Internet of Things (IoT). In addition, it will be offering services such as Smart Application to communicate with IoT devices, cameras, as well as sensors.
TechOn firm will be governed through a series of the formal structure of leadership which will comprise of, the Managing Director, Human Resource Manager, Marketing Manager, Finance Manager, and Information Technology Manager. This personnel can be broadly categorized into three departments; human resource, finance and Information Technology departments.
It is worth to note that, in order for any company which is pioneered in offering products and services need to have laid down policies which will protect it from in any form of attack or threats due to the current evolution of technology. TechOn firm will need to set out various policies which will be binding with the workers while within the premises of the company. Violation of these policies by any of the organization's employee will have serious consequences such as termination of contact or high penalties depending on which policy violated. The Internet of Things (IoT), as well as smart homes, is the two crucial technologies which are employed by TechOn firm. In order to achieve its goals and objectives, the organization will employ various policies which will govern employee handling while with the premises of the organization. The polices can be categorized into three broad categories, acceptable policy, device policy, and digital sanitization of media, reusing, as well as destruction policies which will be in accordance with the technology applied. Any additional policies will as well be clearly documented in the employee handbook and well-defined outcomes in case of any breach will be outlined.
NEVER LOSE YOUR CHANCE TO EXCEL IN KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT - HIRE BEST QUALITY TUTOR FOR ASSIGNMENT HELP!
Introduction
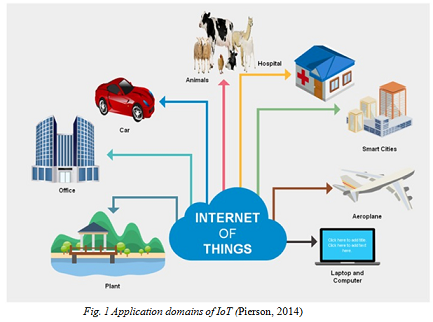
Currently, people have begun wondering what the Internet of Things (IoT) is as well as how it can aid them in enhancing their lives. IoT primarily can be defined as the virtual network of devices within our surrounding which enables objects or devices to have communication among them. This idea of IoT can be traced back I the year 1999, when one of the managers of Protector and gamble firm well known as Kevin Ashton provided a description of how the addition of sensors as well as devices for radio frequency detection to current objects or devices can create an IoT. Present technology has proved that Kevin's vision is on the right track since most of the technological devices or objects have been developed with the internet in terms of Wi-Fi or Ethernet. This is a great opportunity for implementation of IoT (Khan and Shahzad, 2017).
In the Internet of Things, the objects which are connected with sensors are capable of collecting as well as exchanging data or information with each other, study particular behaviors for each other, and provision of real-time information, notifications, as well as data from various applications. One of the most successful developments of IoT is the use of smartphones. However, the implementation of IoT is not limited only to the use of a smartphone, but as well to various applications which include smart homes, smart city, smart cars, as well as smart grid.
Our TechOn firm has come up at the right time when there is tremendous growth of technology in Tasmania City leading to high demand for smart homes. This is due to the need for houses and buildings with secure connections and systems which are safe and more important with gadgets which use energy efficiently as well as which are self-sustainable. With this view in mind, TechOn will be delighted to offer these products and services to the people of Tasmania City and its environments at affordable and cheap prices. The goal of our firm is to ensure the city of Tasmania is well connected and their houses are safe and the environment is safe and well maintained through the power of IoT and smart home technologies. Having realized this gap in this city, this will be work in progress by Techno firm for estimation of one year to ensure that Tasmania city has smart homes and IoT connectivity.
Threat and Risk Analysis
One of the topmost barriers for the realization of the vision of secure smart homes as well as buildings which are energy efficient is the enforcement of security in IoT's facilities. I this particular context, comprehension of the risks which are correlated to the utilization as well as misuse of the data and information about the homes, partners, the customers and formation of ways of integration of the measures to enhance security is not in the correct design and which is an indicator for threat to IoT's. The business of IoT's has been tremendously increased for the last three years, with great impact on both the firms and the customers in sectors around the globe. Despite technology being adopted, a thorough pattern of security has not been well discussed in ensuring future growth and increase of sophisticated landscape of threats and risks for IoT's. Most of the smart devices which are available in the markets of late are vulnerable to intrusions by third parties. Since software to enforce security for these devices can't defend them from attacks, home and buildings networks are vulnerable to attacks.
ORDER NEW KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT & GET 100% ORIGINAL SOLUTION AND QUALITY WRITTEN CONTENTS IN WELL FORMATS AND PROPER REFERENCING.
This being said, we at TechOn we carried a threat and risk analysis and we have identified the following threats and risks which our company is exposed to:
Spoofing: This can be described as the disguisement if packets which are spoofed from a source which is unknown as one seemed to be known which entirely influences the functioning of the device. This is one of the threats which is exposed to our organization and might emanate from the workers whom might get into the premises of the company with their own gadgets and use them to alter information in the systems.
Man-in-the-middle attack: Due to increased cyber-attacks in the continent, our hardware and software will be on exposure to attacks. This primarily happens when the "attacker" interferes and modifies communication between two devices in order to suit his own gain.
Data Breach: This can be defined as the accessing of data or information by third unknown parties without the consent of the owner and releasing confidential information to untrusted parties. After keen analysis, we have realized that data within our databases are prone to breach if not well-organized policies are put in place.
Lack of Updates: Data within our databases will be at risk if it is not up to date and this can be realized through updating it and ensuring passwords are updated on a regular basis.
Unsafe communication: There will be high risks involved if there will be sharing of data which is not encrypted over the network which makes it vulnerable to cyber-attacks.
Home Invasion: If in any case one our client's home is attacked the entire data in the network will be easily compromised and this is a potential risk to the whole organization.
Human Factor: If the personnel of the organization will not be well informed of the security of IoT devices or one of them going rogue, can be a threat to the entire organization due to leakage of information and data.
Main Security Goals for TechOn Organisation and Accompanying Set of High-Level Security Policies
Main Security Goals for TechOn Organisation
The main security goals for TechOn organization will be:
- Provision of quality products and services of IoT's
- Ensure smart homes are secure from cyber-attacks
- Ensuring and guarantee security for the data and information of our client's
- Enhancing standards of IoT's in Tasmania City
GET GUARANTEED SATISFACTION OR MONEY BACK UNDER KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT HELP SERVICES OF EXPERTSMINDS.COM - ORDER TODAY NEW COPY OF THIS ASSIGNMENT!
Accompanying Set of High-Level Security Policies
In order to achieve its goals and objectives, the organization will employ various policies which will govern employee handling while with the premises of the organization. The polices can be categorized into three broad categories, acceptable policy, device policy, and digital sanitization of media, reusing, as well as destruction policies which will be in accordance with the technology applied.
a) Information Technology acceptable use policy
This policy will aim at ensuring that it is well known by all the worker's matters pertaining to handing off all the resources of information technology within the premises of the company. Any activities which are not correlated to the firm will not be supposed to be done using the organization's equipment. Any spotted misuse will need to be reported and could result in serious penalties. Penalties for guilt worker will be disciplined by a committee set out by the HR manager and will be mandated to relegate the worker (s) involved.
b) Bring Your Own Device/gadget Policy
The aim of this policy will be to ensure that workers who have their own electronic devices within the premises will use them as per the instructions outlined under this policy. Workers will be able to use their own gadgets in their work floors when they have been granted permission to do so (Durfee, 2015). Some of the devices are inclusive of laptop and smartphones. Only specific persons will be allowed to use their personal devices within the organization's premises as outlined by the HR department. Severe penalties will be issued to the culprit workers who will be found guilty of their actions.
i) Device protocols
Persons granted with the privilege of using their gadgets will be required to install antivirus software for the purpose of securing as well as securing data information of TechOn firm. Any information about the company will be stored in the MDM installed (Pierson, 2014).
ii) Restrictions on use authorized devices
Devices owned by individuals within the organization's premises which can picture as well as record videos will not be allowed to be used with the premises of the firm and communication which is not made for the company should be done at free time.
iii) Privacy and firm access
The privileged works should be using their personal devices as if possessed by TechOn firm in authenticating the worker's communication every time (Davis & Fisher, 2014). This will aid the firm in ensuring the protection of the organization's private data as well as information.
iv) Penalties and Punishments to workers who will violate the rules for usage of electronic devices
Termination of employment: in case a worker is dismissed, their gadgets will be confiscated and checked by TechOn firm, and private data or information for the company which is inclusive of business deals and any transactions will be cleared from the device.
DO WANT TO HIRE TUTOR FOR ORIGINAL KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT SOLUTION? AVAIL QUALITY KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT WRITING SERVICE AT BEST RATES!
c) Sanitization of Digital Media, Reuse Purposes as well as Destruction Policy
The goal of this policy will be to safeguard private data of the firm. It is primarily intended in securing crucial information in the gadgets which might during operations such as the destruction of the data from personal devices by dismissed workers, reuse, as well as the processes for retrieval of the information for reuse purposes. Any information deleted could be retrieved by third parties and end up in untrusted persons who will make the company to breach the laws pertaining the protection of information and regulations as outlined in the countries laws (Abrahamson et al., 2013).
The policy will be applicable to all workers employed on a permanent or contract basis. The workers should ensure that data or information is removed from the gadgets which are taken out of the user's departments, for disposal purposes, for utilization on other business or recycling purposes. Experts will be consulted before the information is deleted.
Appendix
Case Study: TechOn Company
"TechOn" is an IoT based company which provides IoT devices for homes to make them smart homes such as smart lightbulbs, smart refrigerator, washing machine, door locks, etc that can communicate within and outside the home environment. The company is offering both products and services such as a Smart Application to communicate with IoT devices, sensors, and cameras. The company will also provide supplies to businesses using IoT devices. TechOn has two offices in Tasmania, the head office is in Hobart and the other branch is in Launceston. Employees of the company are as follow:
- Managing Director: At the top position the company has a managing director who is responsible for the performance of the company and decision-making. He will also formulate and implement company policies and strategic plans for profitable growth. Under him, there will be several managers.
- HR Manager: Responsible for recruitment, hiring, and retention of skilled and qualified employees in the company.
- Marketing Manager: Responsible for all marketing campaigns for the company provides information on customer needs and preferences to development teams for improvements in the products. He will also set prices and create a plan to launch the product.
- Finance Manager: Responsible for monitoring of accounts, reviewing financial reports and financial forecasts.
- IT Manager: Responsible for regular checks on the network, data security and system audits, design training programs and workshops for staff and provide directions for IT team members. The team members include network administrator, database administrator, developer, and technicians.
GETTING STUCK WITH SIMILAR KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT? ENROL WITH EXPERTSMINDS'S KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT HELP SERVICES AND GET DISTRESSED WITH YOUR ASSIGNMENT WORRIES!
Non-ICT goals
The Non-ICT goal of TechOn is to provide a smart environment, which is energy efficient, time-saving and suitable for all age people.
IT Infrastructure
TechOn contains various components that play an important role in IT-enabled operations. The IT infrastructure has the following components:
- Hardware: Computers, servers, hubs, switches, routers and data centers.
- Software: Productivity application, customer relationship management, Enterprise resource planning.
- Network: Firewall, security, internet connectivity.
- Meat-ware: Network administrator, database administrator, developers, technicians and end users.
Threat Analysis
The most important computing asset of TechOn will be the personal information which will be stored in our databases and the hardware i.e., the IoT devices which the company is selling. Both hardware and software (and data) are valuable.
Following are the major threats which can harm the organization and its assets:
- Spoofing: Disguising spoofed packets from an unknown source as being from a known, trusted source and influencing the functioning of a device.
- Man-in-the-middle Attack: Attackers placing themselves between the two devices (parties) and intercepting and modifying the communication between the two. The victim is not aware of the man in the middle attack.
- Data Breach: Accessing of information by the unknown party(s), without the authorization of the owner and releasing private/confidential information to an untrusted environment.
- Lack of Updates: Current security measures become vulnerable and insecure as the new technology rolls out, failing to provide security updates regularly will make the device prone to a data breach.
- Unsafe Communication: Sharing of unencrypted data over the network can be a big security challenge as it becomes vulnerable to cyber-attacks.
- Home Invasion: IoT devices reduce the gap between the digital and physical worlds. Unsecured IoT device(s) can leak the IP address, which can be used to find the physical location of the person or device.
- Human Factor: Lack of knowledge among the employees or an employee going rouge, is not an outright threat, but it is something to be checked upon from time to time.
ORDER NEW COPY OF KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT AND SECURE HIGHER MARKS!
Risk Analysis
Risk analysis can be defined as the process which helps to detect and manage probable problems or adverse events occurring in an organization when starting a project.
Following are the risks which may impact the organization the most:
- Spoofing: In this type of malicious activity, the third-party member contacts the user to disclose the personal information pretending an employee of "TechOn".
- Man-in-the-Middle Attack: It is a form of overhearing or observing the data or communication between the sender and receiver. It is a dangerous attack where the attacker comes between the network of TechOn and its customers and sends his own messages.
- Data Breach: As personal information is being the main computing asset of TechOn, it is the most valuable entity for the hackers as well, protecting which is the topmost priority.
- Lack of updates: If the company fails to provide regular security updates to its systems and devices, then the system can become vulnerable to hackers and cyber-attacks.
- Unsafe communication: If TechOn does not encrypt its messages which are being sent to its customers over the network, it possesses a risk for both the users and the company of being breached.
- Home Invasion: TechOn should focus on safeguarding the IP addresses and digital presence of its users on its servers. Failing to do so may result in a direct or indirect threat to customers.
- Human Factor: If employees lack knowledge about their products and services, they will not be able to perform efficiently and will make mistakes.
Section 2 -
Physical Security
It is important to note that, IoT has continued to have new integrations which exist in vast growing array systems which include sensors. Due to enhanced connectivity of sensors to individuals, things as well as process, once in the systems, such a physical guard is a crucial part of smart homes and IoT (Pierson, 2014). TechOn firm will enhance the physical security of its premises through the integration of sensors, access, and video systems. This is a result of the threats which are posed to the network as well as hardware infrastructure for our company. In addition, the company will deploy cloud-based systems and hybrid systems as a solution to the risk and threat which is posed to our entire infrastructure to monitor on a real-time basis. This will guard our systems from any of the internal or external intrusion and compromise our systems. As a way of protection of our databases, various steps will be taken into consideration. Major chips will be epoxied to the boards of the circuit so that they will be destroyed in the attempt of removing it. Additionally, the entire circuit will be embedded in resin block which renders it from been accessed to all but to the authorized persons. It is important to note that, many devices can be tampered in the process of supplying or the transit or warehouse. This case will be managed by applying anti-tamper seal or package in order to provide a visual indicator when there is an attempt of interfering with any of the devices. As well, the casing of devices will be another physical security measure which will be employed by our company. This primarily will protect the devices physically in innards, from the initial mounting step of assembling and aid in detecting any emanations.
NEVER BE CAUGHT IN PLAGIARISM, AVAIL KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM AND SAVE HIGHER MARKS!
Logical Security
It will quite essential for TechOn firm to foresee security measures in terms of its infrastructure. Through the enhancement of the logical security of the company, it will ensure that all the devices within its infrastructure are highly protected. It is recommendable for TechOn firm to use internal memory and external memory but only to specified persons. Despite being technique which is not cryptographic it is effective as well. It is important for the management to have storage of the firmware and crucial data in internal memories as well as protecting programming API blocks. All devices within the company's infrastructure need to be controlled from one access point but not from multiple points as this will lead to compromising of private data and information. Additionally, all data and information from the servers need to be synced on a real-time basis to ensure every detailed of any signal is captured wholly and on a frequent basis.

It is crucial for the employees if TechOn company to have in depth the knowledge of the elements of IoT. This will ensure that every worker will be geared in working towards the realization of the goals of the company with the best interest and knowledge of the elements. Additionally, this will ensure no breach of data within the systems will be done due to lack of knowledge of what goes around the whole infrastructure.
Data and System Security
Security for TechOn firm data and systems is crucial and at stake all the times. The top management will be expected to have all the measures deemed possible to be put in place to ensure that the systems and data are secure. The following process of the command line will put implemented to safeguard the systems and data within our databases.
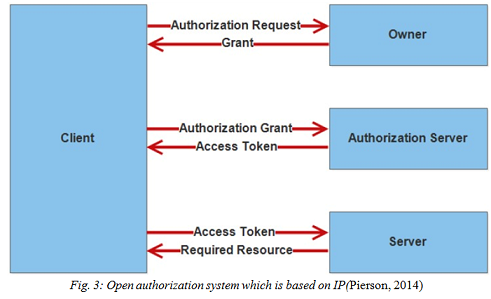
In order for TechOn firm to implement the above mechanism of authorization, several questions will be addressed before any access of data or system is granted:
- Which individuals have been authorized to access or use particular data, information or system?
- What mechanisms will be used in accessing the data, information or systems?
- What type of operational mechanisms will be used by the specified individuals? Perera et al., 2014).
Once these questions have been addressed fully access of the data, information or systems will be granted. This authentication process will be of great aid for TechOn firm in protecting private data and information as well as the entire systems.
Network Security
Network security needs to be as put in consideration for TechOn firm to be secure. If the network is secured, this will bar off any intruders from accessing any systems or data making it accessible to untrusted third parties. If this is not put I consideration, data and information for the company might be comprised and this is quite dangerous for TechOn firm. Therefore, with this being said, various security measures need to be put in place and adhered to according. It will be required by all the employees of TechOn firm to check settings and ensure that they are updated regular basis. This measure is essential since most of the devices come with settings which are the default and it is essential for them to be changed. It is worth noting that, not all producers have good intentions in their mind and the default configurations might allow them to access the systems and compromise any data or information in them. Another measure to ensure the network for TechOn firm is secure is through disabling of the UPnP features within the devices (Zhang et al., 2016). Despite this features being convenient and does away the need of configuring one device at a time, the protocol primarily relies on any local network to connectivity, it makes the network vulnerable to attackers who might be third parties. This will minimize any intrusion into the servers and databases by third-party persons which lead to compromising of data and systems.
EXPERTSMINDS.COM GIVES ACCOUNTABILITY OF YOUR TIME AND MONEY - AVAIL TOP RESULTS ORIGINATED KIT711 NETWORK SECURITY TECHNIQUES AND TECHNOLOGY ASSIGNMENT HELP SERVICES AT BEST RATES!
We at Expertsminds offer best University of Tasmania, Australia Assignment Help service for different units, such as -
- KIT501 ICT Systems Administration Fundamentals Assignment Help
- KIT503 ICT Professional Practices and Project Management Assignment Help
- KIT506 Software Application Design and Implementation Assignment Help
- KIT701 ICT Research Methods Assignment Help
- KIT707 Knowledge and Information Management Assignment Help
- KIT708 ICT Systems Strategy and Management Assignment Help
- KIT709 Enterprise Architecture and Systems Assignment Help
- KIT710 eLogistics Assignment Help
- KIT712 Data Management Technology Assignment Help
- KIT713 Multi-perspective ICT Project Assignment Help
- KIT714 ICT Research Principles Assignment Help