ITECH 4101 Network Security Assignment Help
Firewalls
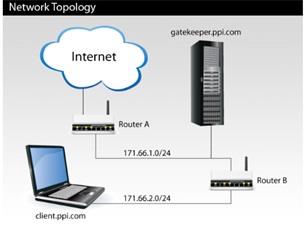
Your company, Plush Packet, Inc., has the following network topology:
Plush Packet is worried that a Trojan virus infecting one of its internal machines may steal proprietary source code and send it outside the internal network. Therefore, every employee is issued a small hardware authentication device. Any communication to the outside world must be authenticated by a human typing in a security code computed by and displayed on this device. To enforce the policy, the administrators set up a single machine, gatekeeper.ppi.com, that manages interactions between internal company machines and the rest of the Internet.
Employees can log into gatekeeper from internal machines using SSH and their hardware authentication device. From gatekeeper, they can SSH to the rest of the Internet. Internal machines are on a separate subnet (171.66.2.0/24) and can exchange packets with gatekeeper but not with the outside world. Machines on the outside Internet are not able to SSH to gatekeeper.
Question 1. Describe how to enforce this policy with simple (or stateless) packet filtering on Router A and/or Router B. Describe the precise packet filtering rules you would put in place at each router.
Question 2. After several days of this new policy, employees become annoyed that many applications seem to lock up for periods of a minute or so. IT suspects that the problem is caused by attempts to create TCP connections to the outside world, which, instead of failing instantly, take approximately 1 minute. After all, clients' TCP implementations treat packets dropped by the firewall policy just the same as packets dropped because of congestion-they back off and keep trying. To solve the problem, the administrators reconfigure their routers not just to drop packets silently, but in certain cases to send packets back to the source of a dropped packet. Describe precisely what the routers can send back to make prohibited outgoing TCP connections fail quickly. (Assume they cannot make any changes to the TCP implementation on clients.)
Expertsminds.com accepts instant and short deadlines order for ITECH 4101 Network Security Assignment Help services - order today for excellence!
Introduction
Plush Packet is a company that operates with lots of workstations and recently they have faced an issue related to attacks of Trojan Virus which can leak their confidential information to the outer networks hampering their confidentiality. The problem is going to solves by handing hardware authentication devices which they will use to intercept the outside communication, which will have authenticated by writing a security code. Therefore, this report will consist of the communication among the devices and the outside world, by a packet filtering policy applied on Router A and Router B. Lastly, the report will also describe the functionalities of the routers in stopping the outgoing TCP connections.
1. Describe how to enforce this policy with simple (or stateless) packet filtering on Router A and/or Router B. Describe the precise packet filtering rules you would put in place at each router.
There are two major types of Filtering policies which can stop the unwanted bugging or unplanned protocol operations. The two most common type of filtering which can be applied on routers to control data traffic as well alien information from disrupting the system are Proxy Firewall and Packet Filtering Firewall (Wang & Kissel, (2015)). This works according to the layers in the protocol stack, and used IP addresses and port numbers to verify the user or the person accessing the information. The packet filtering firewall will be most preferable in the case of Plush packet as it has been attacked by a Trojan horse which is only acquired through unwanted internet sites. Packet Filtering will help in analyzing the internet routers, Router A and Router B and automatically filter the traffic. They work according to the discarding of certain packets or forward packet to filter traffic or unwanted access and safe it from viruses.
The packet filter firewall applied on the Routers will be stateless, and they will analyses each datagram coming from both the routers. The imposition of another Router will be helpful in decreasing the data traffic. The following figure will show the treating of routers through the implementation of stateless packet filtering firewalls. The network interfaces will be given as follows:
- "Inside"
- "Outside"
- "DMZ"
The DMZ subnet gives allowance to extranet, in which place the servers are nit allowed for access to any random users (Liu, (2015)). The stateless firewall will send one packet at a time, so that the network administrator can access control lists like ACLS, the packet list also should be verified before sending so that they can successfully fight the viruses or data traffic. The packet will send according to analyses which traffic is safe for the access and thus allow it from inside top outside.
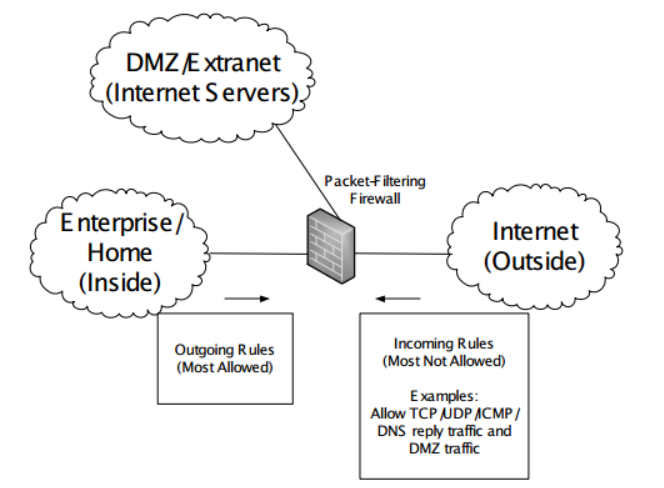
Figure 1: The implementation of the packet filtering firewall
(Source: Sairam & Kumar, (2019) )
Rules of packet filtering
The machine of Plush Packet is on a separate subnet of 171.66.2.0/24, and it is a 24-bit subnet, which will match with any addresses starting from 171 and is equivalent to 171.66.2.0. The specification of packet filtering product as the rules vary from the type of subnet they are situated and the IP addresses (Hsu & Wang, (2015)). Therefore, the rules regarding this situation can be given as follows:
- The filtering rules should be decided before installing any packages on the routers, Plush packet can use TCP wrapper to control the hosts
- The rules should be verified and renewed every time
- The usage of IP addresses is most preferable than the usage of hostnames
2. Describe precisely what the routers can send back to make prohibited outgoing TCP connections fail quickly. (Assume they cannot make any changes to the TCP implementation on clients.)
There are mainly two options for the router when they get packets, without changing any TCP configuration. They are as follows:
Forwards the packet- If the packet matches the criteria, the router will forward the packet to the destination (Kaur Chahal & Behal, (2019))
Dropping the packet- The mismatch in the configuration will tend the router to drop the packet and it will not reach its destination folder
Actions taken in Logging- Even though many applications forward or drop the packets, the action must be forced by the user, this tends the router to run a foul. In case of dropping of packet, the router sends an ICMP code which is an error code which will show the message rejected. The ICMP Code refers in not sending same type of package.
Conclusion
In the following report, the methods of controlling data traffic and attacking of viruses have been mentioned. Therefore, it can be said that packet filtering and setting rules can help the company Plush Packet in gaining more security and prevent their system from Trojan horses. The further analysis has been done on the implementation of packets and the type of response the routers will send. The procedure have been enunciated in a varied way and also explained about the return of the routers while handling packages and reaching them out to the destination.
Getting Stuck with Similar Assignment? Enrol with Expertsmind's ITECH 4101 Network Security Assignment Help services and Get distressed with your assignment worries!