Intrusion,Detection and Prevention Assignment Help
Research the speculations on where the state-of-the-art will be in the near future for one of the following technologies. Your paper should include a description of the state-of-the-art in your technology, a discussion of where the sources that you read believe the technology is heading in the near future, and a discussion of how this technology will affect the choices you would make if you were making purchase recommendations for a client. Although there is room for personal opinion in your paper, you must justify your conclusions.
The paper should include a one paragraph abstract, an introduction, and a conclusion - think as if you were writing for a professional journal.
We Help Students to improve their grades! Avail TOP Quality Intrusion,Detection and Prevention Assignment Help solution and Homework Writing Services at Cheaper Rate!
Introduction
Intrusion Detection and Prevention Systems (IDPSs) are mainly focused to identify the all possible incidents in the computer. An IDPS can detect the eventwhich created by the attackers who successfully compromise the computer by exploit vulnerability. Log information of activity can report to the administrators of the security and they can start to take action to minimize the causes of system damages (K. Scarfone, 2007). Most of the IDPSs configure to recognize the violations of security policies. For instance, restrict to share the file peer to peer and transfer the large volume of the database on the mobile devices or secondary storage. An intrusion detection and prevention system are used to understand the threats and detect, especially the attacks characteristic and frequency of the attacks. By analysis the above characteristics will help to take the appropriate security measurements can identify. When new threats are detected then some of the IDPSs can change their security profiles. Intrusion Prevention System is differed from the intrusion detection system by the response to detect the threats by an attempt to prevent the system from succeeding. IPS has various response techniques are available which are classified as the following group
? Stops all attacks by IPS.
? Terminate the network connection affected by attackers
? Block the access to the target system from attackers IP address, some attributes of attackers and attackers accounts.
? The environment of the security can change by IPS
? The configuration can change by IPS
Methodologies in IDPS Detection
We have various methodologies are available in the IDPS technologies to detect the attacks. The detection strategies are primarily divided into three orders are anomaly detection, stateful protocol analysis, host-based, signature-based and (Whitman, 2010). The multiple methodologies are used in most of the IDPS technologies which can be used as separately or it can be used as an integrated way to provide an accurate result of intrusion detection. IDPS methodologies described given below
Signature-Based Detection
The signature-based detection method is a process the signatures which compare with observed signature to find any possible attacks. Here signature is represented as a pattern to known the type of the attack. An example of signature-based detection methodology is given below
? A telnet server tries to connect with the username as "root" which violate the security policy of an organization.
? The subject of the email is "Free pictures!" or file name of the attachment is "freepics.exe" which states that known form of malware (ISS, 2014).
? The status code of an operating system log entry value is 645 which represent the disabled state of the host.
Let we consider for an instance, in case the attacker can modify the malware such as the name of the file can be "freepics2.exe", for looking signature "freepics.exe" which not matched. This method could be a simple way to detect intrusion and compares with current activity status, for example, log entry and network packets to list the signature to compare using string comparison operation. In this methodology, we can understand the many networks and application protocol but we cannot track the state of communication. For example, a request pair not possible with the respective response which can remember only the previous request when processing the current request. When request not pair with the response can prevent signature-based method to detect the intrusion attacks which comprise the various events in communication.
Anomaly-Based Detection
Anomaly-based detection method will perform the process of comparing normal activity with observed events which help to find the significant deviations. This method in the IDPS detection profile could be between normal behavior of users, network connections, hosts and applications (Iftikhar Ahamad, 2010). This profile developed by monitoring the activity over a period of time. This method uses the statistical method of the result is compared with current activity to threshold values relating to the profile which detect when activities of web comprise significant bandwidth than expected then alert raise to an administrator of an anomaly. The profiles activity can develop by various behavioral attributes are the number of emails sent by the user, the number of logins attempts to fail. The primary benefits of anomaly-based detection method are very effective to detect the previously unknown attacks. Let we consider for an example in case the computer is infected by a new type of attacks or malware. This type of malware can consume the computer resources to process, send emails, start the number of connections in the network and further profile behavior could differ from the profile which are established. The profiles can classify as static and dynamic (Govindaraju, 2007). In static profile, once profile created then it is unchanged unless IDPS create new profile directly. The dynamic profile, constantly adjust profile while observing events. Due to changes in networks for a certain period of the time which measure the normal behavior and also changes in the behavior. A static profile becomes inaccurate so we need to regenerate periodically but dynamic profiles no need to regenerate but it is susceptible to evasion attempts from attackers.
Stateful Protocol
Stateful protocol method can perform the process to compare the observed event with the predetermined profiles which can identify the difference or deviations of observed and predetermined events. (Govindaraju, 2007). This methodology differed from the previous method and stateful protocol is used in the host computer or specific profiles in the network.The stateful protocol analysis always relies on the vendor's universal profiles which specify how protocols should not and should be used. This protocol state that IDPS has the capacity to understand and track the state of the network layer, transport layer and application protocols which has the notation of the network state. Let we assume, the user starts the session of File Transfer Protocol which could be unauthenticated state initially. In this state, the user can perform only a few commands such as view help information, provide user name and password. The most significant part is to understand the state pairing request with the response when FTP session has authentication occurs which determine the success of status code with the respective response. Once authentication is confirmed by the user the state of the session is authenticated and users can perform any and more commands. In the state of unauthenticated, perform many commands would be considered as a suspicious attack but in the authenticated state, perform many commands is considered as benign. The primary drawback of this method is complexity analysis and perform the state tracking for more simultaneous sessions (ISS, 2014). The next issue of this method cannot detect the attacks that do not violate the general behavior protocol. Another issue of this method is used in IDPS may conflict with the way of implementation of the protocol for a particular version of the operating system.
Components of IDPS
An IDPS has following components are:
? Agent or Sensor: An activity can monitor and analyze by an agent or sensor. The sensors are used for monitor the networks and agents of IDPS technologies to monitor a host.
? Management Server: This component is one of the devices which can receive the data from the various sensors or agents to manage all data. This can perform an analysis the received information and identify the incidents which are presented in an individual sensor (K. Scarfone, 2007). A piece of event information can match from various sensors or agents so that we can find the event triggered by the same IP address is called a correlation. The management servers will not use in the small IDPS deployments. But in large deployments of IDPS can use the multiple management servers and also, they can be used as tiers
? Database Server: This server can act as a data storage repository of event information which is recorded by the various agents, sensors and management servers. The database server uses in many IDPSs to support the repository system.
? Console: An interface between administrator and users of IDPS is called a console which software program to install on the laptop or desktop computers. But some of the console programs used for IDPS by administrators only (K. Scarfone, 2007). For example, sensors or agent configuration and apply for updates of software while console programs are used to monitor and analyze. The IDPS console programs have capabilities to handle both administration and monitor the system.
An above four IDPS components are connected each and every other through the regular networks otherwise unique design of network for security management software is called management network. In case, management network use in an agent host or sensor which add the network interface is called management interface to make a connection to the management network. Once host are configured then it cannot transfer the network traffic between management interfaces and network interfaces. In management, the network has management server, consoles program and a database server which are IDPS components (Govindaraju, 2007). This management network design is very effective from the production network and hides the IDPS form the intruders which ensure that IDPS has enough bandwidth to handle any conditions. In case, deployment of IDPS not in network management separately then improvement of IDPS security can create a virtual management network using Virtual Local Area Network (VLAN) which provides the protection communication of IDPS but more protection not possible in a separate management network.
IDPS Technologies & Types
An IDPS technology types are classified as four groups and groups are based on types of monitoring the events and deployment of technology way:
Network-Based:
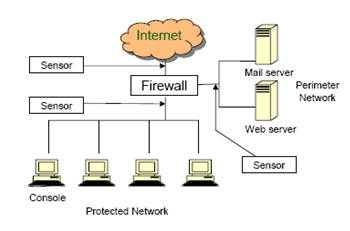
The network-based technology is used to monitor the network traffic for the specific segment of the network or network devices. It is also used to analyze the network and identify the suspicious activity by an application protocol layer which identifies the various types of events (Govindaraju, 2007). This can be deployed between networks, for example, this can be close to the border of the firewall or network routers, wireless networks, and remote servers. The following figure 1 shows the network-based IDPS technology which deployed between two networks ad close to the firewall with a remote access server.
Wireless:
Wireless technology is used to monitor the traffics in the wireless networks and also analyzes the wireless network protocols to identify the suspicious activity between protocols. The suspicious activity cannot be identified in the application and TCP, UDP layer protocol in the wireless network transfer the traffic (Elson, 2012). This technology mostly deployed within the organization range of the wireless network to monitor but also, we can deploy to locations where unauthorized access occurs in the wireless network.
NBA (Network Behavior Analysis):
Network behavior analysis technology can use to examines traffic which is in the network to identify threats in the network and it will generate the unusual flow of network traffic, for example, DDoS (Distributed Denial of Service) attacks, back doors, worms is called as malware and violations of security policies, for example, a client system can provide network services by unauthorized to other systems (Iftikhar Ahamad, 2010). The NBA technology is mostly deployed to monitor the flows on internal networks in the organization, and it is also deployed to monitor between external networks and internal networks such as the internet and networks of business partners.
Host-Based:
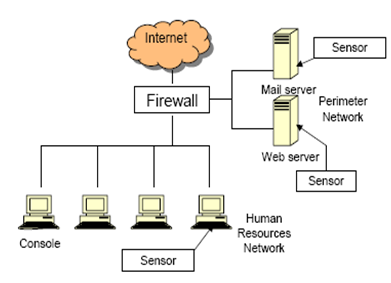
Host-based technology is used to monitors the single host characteristics and any events happens in a host then it states suspicious activity. Such as this type can monitor the network traffic, status of running processes, system logs, activities of application, modification and access the file, and changes in the configuration of system and application (ISS, 2014). This Host-based IDPSs technology can be deployed commonly on critical hosts for example servers can access publicly accessible and sensitive information are available in servers.
The following figure 2 shows the host-based IDPS technology
Conclusion
The intrusion detection system (IDS) is the procedure to monitor the occasions which happen in a PC or system. It is used to analyze the sign of incidents which are possible to violate or up and coming dangers of PC arrangements for security. An IDS is a software to automate the process of detecting intrusion. An Intrusion prevention system is a program which represented as software has capabilities to detect the intrusion and possibility to stop the attack events in the system. Many technologies for the IDS and IPS can offer the above capabilities and network administrators have rights to disable the features of prevention system in the intrusion prevention system which cause the function of IDSs. Intrusion Detection and Prevention Systems (IDPSs) are mainly focused to identify the all possible incidents in the computer. An IDPS can detect the incident by the attackers who successfully compromise the computer by exploit vulnerability. Log information of activity can report to the administrators of the security can take the actions to reduce the causes of damage. This report given the detailed information about intrusion detection and prevention which has IDPS methodologies are classified into three categories are anomaly based, signature-based, and stateful protocol analysis. The first method is signature-based detection which process the signatures compares with observed signature to find any possible attacks. Here signature is represented as a pattern to known the type of the attack. Anomaly-based detection method performs the comparison between observed events with the normal activity which help to find the difference or deviations. This method in the IDPS detection profile which profile could be between normal behavior of users, network connections, hosts and applications. The last method is stateful protocol is compares and identify the deviation between observed events and predetermined profiles. The IDPS technology names are wireless, host-based, network-based and network behavior analysis, Host-based and components of IDPS are Agent or sensor, management server, data server, and console program.
Never miss your chance to excel in Intrusion, Detection and Prevention Assignment Help solution from Expertsmind! We provide 24/7 academic assistance as per your convenience.