EXPERTSMINDS.COM ACCEPTS INSTANT AND SHORT DEADLINES ORDER FOR PENETRATION TESTING ASSIGNMENT - ORDER TODAY FOR EXCELLENCE!
Learning Objective
Appraise security posture of a fictional application by completing a team-based pen test.
Identify the focus of the framework and the sponsoring organization.
Interpret the impact of regulations, policies, and laws in the cybersecurity field.
Executive Summary
In this assignment, we have studied various tools and we have written information about the NMap. And this assignment is based on the network administrator. In this assignment, we have identified all the issues and provide the security that is necessary to solve the problems with security activities. In this assignment, first of all, we have downloaded and installed the Karli Linux tool with proper installation. This tool was downloaded from the internet. This Karli Linux is easy to download and easily available. Here we have taken the screenshots, and then we have installed this tool on the computer correctly.
Your task is to pick a target of your choice, perform a penetration test using the tools and techniques introduced with Nmap, OpenVas, and Armitage, and complete a penetration test report that summarizes the findings.
Install VMware
Configure OpenVas and install
In the above figure, we can see how to execute the OpenVas setup and next we are going to perform the Vulnerability.
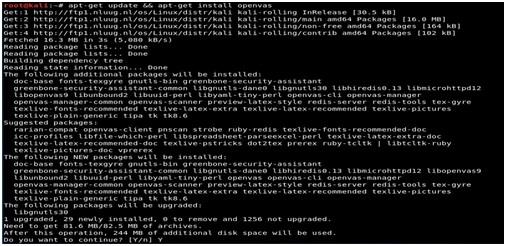
Openvas- Setup command is used for openvas installation

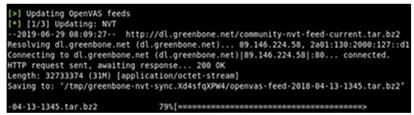
In above figure, we can see the update the OpenVas
NEVER BE CAUGHT IN PLAGIARISM, AVAIL PENETRATION TESTING ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM AND SAVE HIGHER MARKS!
Run OpenVas
We are running the openvas and configure the openvas. After started the interface it runs automatically and this interface run by using certain port. It will access the local host which is default server and run by the port. After run the setup, we run the update command which updates the openvas feed and we can see how to create the account. Here we can set the password automatically.
Dashboard
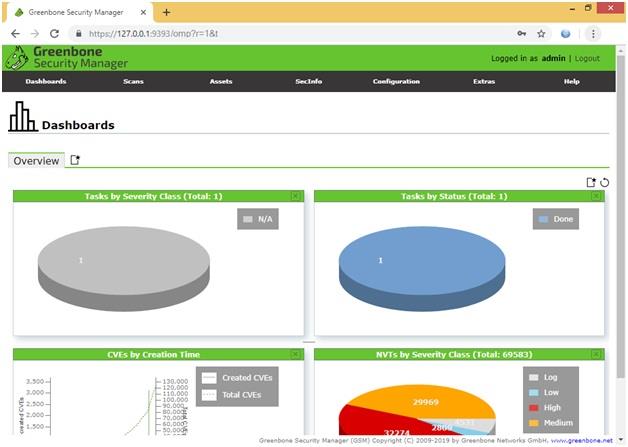
In the above figure, we can see the dashboard. In the dashboard, there are severity class, status, CVE, and NVT class. The dashboard helps to understand the issue and vulnerability. Here, we can also help to understand the high, low and medium of NVTs. The dashboard helps to understand the story of the current network security and helps to decision machining.
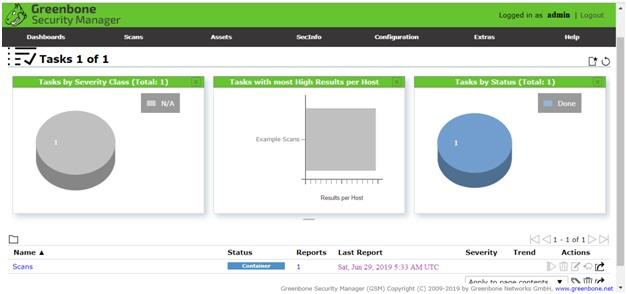
Task
In above figure, you can see the scan result
In screenshot, we can see the host, status and severity.
Scan
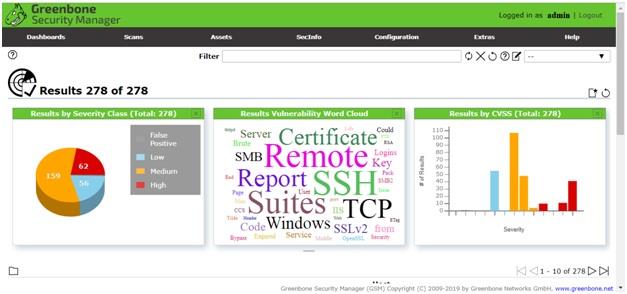
In above ,we can see the scan process where we can see the location ,date and vulnerability.
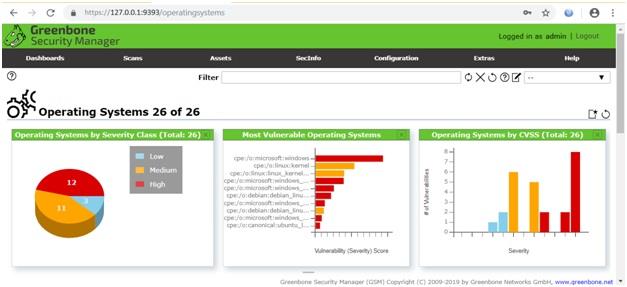
Here we can see the operating system scan vulnerability.

In above, we can see the host severity and host topology
CPE
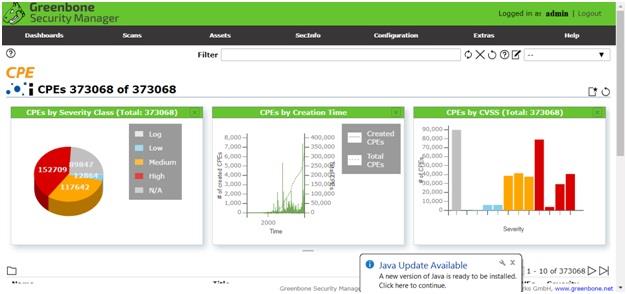
Here, we can see CPEs by CVSS
CVE
Authentication or permission
Report
NMap is the open sources and free network scanner and we need to identify the installation. Then we have to check the configuration of the Metasploit (network vulnerability scanning tool). We have to install this tool over the network. Then we have to check the network vulnerabilities in network adjacent to the hackers. We can use the vulnerabilities because it is prominent. After the completion of the installation of Metasploit software this tool is used for scanning and starts the analysis of the security that the security would be subjected. Here, we have to write the name of the target website and then click on the scan button. Then Metasploit tool is ready to scan and then start the scan after that we obtain the information about the security problems.
WORK TOGETHER WITH EXPERTSMIND'S TUTOR TO ACHIEVE SUCCESS IN PENETRATION TESTING ASSIGNMENT!
Vulnerability concerns and Weakness and of the network
In this assignment, we have developed the network system as per the client requirement. We have developed our own website over the network. This website is free from attacks. We have analyzed the case- study, there are many security holes in the website. So, our requirement is strong with the security policy. Here the hacker can hack our website which has a strong security policy. Then the website password is secure by the hacker. Our website password is the combination of the two-factor for authentication and we need to secure the website. Then we have to check the patches and plug-in in our website. If the plug-in is de-activate which lead to the hacking website.
For secure our website we need to check and it helps to secure the over the network. In this report, there is much malware which needs to be detected the issues. Here, we need to protect and secure our website. Protect the website against the website hacking and malicious code by using our own web application firewall. Every day the hackers provide and discover the vulnerabilities. For that, we need to secure and protect our website and prevent suspicious behaviour. Then we need to check the website and website password regularly. And then stop password cracking and brute force attacks to prevent to neglect website.
For protecting our website form the hackers so we need to check the security patches regularly. If we released the website security patch then the hacker will hack our website. Then we cannot update the patch to our website so maybe leaded to hack the website by the hacker. We need to create a security policy to update patches and protect or secure the website and prevent server rules and update our website regularly. Then we need to insert the other protection layer with enabling the Protected Page feature to the sensitive page. We need to protect our site from the hacker. So we need to write the IP addresses. This IP address is used to protect with the unauthorized user. We need to list IP addresses. Here the authorized user is used to access the entire website. All the team member of the website will be used for the admin panel. To protect our website we need to provide the features to protect and secure the website form the vulnerability. Vulnerability exploitation efforts which are we detect the hacker tool or malicious bot, this is trying to attacks on our website which will be blocked and secure our website.
Network Security issue and their resolution
In this report, there are many problems which find or search the website security. Here the hacker hacks the website very easily with many problems and there are many problems. Our website hack by the hacker so, we need to protect or secure our website from the hacker. Many hackers hack our website by using website layers. Hacker can be used website layer to the inject command. Hacker led to much information. So, we have secured our website. We have to provide the security or protection with website from visitor safe and malware free. We have to gives the password that helps to prevent and secure from the hacker.
Conclusion
In this assignment, we have studied and analysis of the security tool. There are many security tools are available. These tools are used for the company for solving the issues. For the security problems, we have installed and configure the snort tool and Metasploit tool. We have used many activities which are used to prevent the website as the hacker activities. The Metasploit tool is the power tool and it is used for penetration testing. We have used Metasploit tool and by using this tool we are doing penetration testing and doing everything in the web application. This tool cannot be used for testing every type of vulnerability. Here we have used another tool that supports web application framework. We make the backdoor payload PHP for the web application. The Metasploit tool is good for the learner because it is good software to learn very easily.
GET ASSURED A++ GRADE IN EACH PENETRATION TESTING ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!