VPN Replacement Technologies and Security Analysis
MN610 Virtual Private Networks
Melbourne Institute of Technology, Australia
ORDER NEW VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT AT NOMINAL PRICE!
Assignment – VPN Technologies and Security issues
You should be able to demonstrate their achievements in the following unit learning outcomes:
a. Analyse and discuss the significance of VPN for contemporary organisations and how it addresses their concerns and security issues.
b.Explain the role of VPN, its limitations and works done to address these limitations as well as to supporting the security of businesses and corporations.
Assignment Description
Tasks:
There are two parts to this assignment, i.e. part A and part B.
A. Write a review article for the following topics depending on the last digit of your ID: select Topic 1 if it ends in an ‘odd’ number or Topic 2 if it ends in an ‘even’ number.
B. Presentation(to present in 5-8 slides only in 5-8 minutes during Laboratory time)
Question 1. Topic 1 - Cloud Computing Security with VPN
Discuss how to secure connectivity to public cloud networks with VPN. Evaluate public cloud performance considering varying security schemes of firewalls and VPNs under the four scenarios: no firewall no VPN, firewall-only, VPN-only and a combination of firewall and VPN. Investigate the impacts of using VPN together with firewall on cloud computing performance. Address the issue(s) of VPN security in details as described in common part section
Answer :
Introduction
Usage of VPN (Virtual Private Network) is on rise. With the growing volume of multimedia contents, people look out for VPNs that can allow them to stream information on the go without having to fear for the security concerns. However, the process of deploying this VPN involves many steps such as configuring the client VPN software, enabling the firewalls and configuring the VPN server to accept the traffic and allow legitimate sources to access resources thereby restricting the rest from access. Though the concept of VPN is to connect the trustworthy source to another portal via a network that is credible, there are still challenges involved.
Certain VPNs are easy to encrypt and this can lead to the compromise of data present in the client network. This is the reason for SSL used by the websites and other network VPNs in the recent times. Looking at how the VPN connection is established, a point to point connection is setup through tunnelling protocols. This is actually the process followed several years ago. In the recent times, VPN is available for cell phones as well where a VPN application can be downloaded and installed and once the setup is done, there are no geographical restrictions. It is possible to access data secured to Egyptians just from USA. There are different types of VPNs based on connection, security levels provided, tunnelling protocol involved, ability to connect devices simultaneously and OSI layer appropriate to connecting network. There were only host to network VPNs in the olden days but site to site VPN is becoming popular and this encourages collaborators to share data through the same VPN.
GET BENEFITTED WITH QUALITY VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Literature Review
Mohamed et al (2014) claims that VPNs are highly vulnerable to security issues. This is the reason for cryptography protocols to come into the picture. Company VPNs prefer private key to access data pertaining to the internal assets. VPNs are available at free of cost and such networks encourage access of arbitrary nodes to required information and the tunnelling protocol deployed here is ineffective to the extent that the customers cannot rely on it for information exchange.
On the other hand, the expensive VPNs available in the market apply stronger algorithms for security such as international data encryption algorithm, blowfish and advanced encryption standard that fragment the text into different blocks and then send to the recipient. Encryption-decryption technique is applied to tighten the security. Jyothi and Reddy (2018) have discussed about the legacy VPNs. Virtual private networks have evolved based on the availability of virtual circuit. According to the consumers, these are cost effective when compared to the leased lines to access data.
Due to the widespread availability of internet, mobile phones have also begun using VPNs and this has added ease to the communication. Companies who have developed VPNs work on different factors such as quality of service, reliability, response time, throughput and availability.
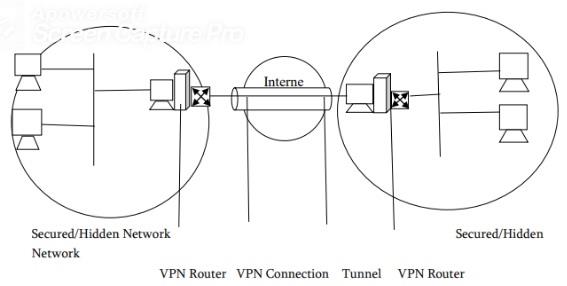
The typical architecture of VPN is here. Multi protocol label switching (MPLS) VPN is considered to be the most flexible procedure to allow data movements. According to this technology, the border gateway protocol is used to route the data and MPLS is used to increase the throughput and availability of data by forwarding packets easily. The reason for its significance in the market is due to the inbuilt components such as customer edge routers, provider routers, provider edge routers and routing information across the designed interface. The reason for terming it to be efficient is because it does not share the virtual routing and forwarding table for public access.
If you are to choose an excellent internet VPN to gain instant access to multimedia resources belonging to different parts of the world, it is important to look into characteristics like message authentication protocol, data integrity, data confidentiality and sender non-repudiation. IP packets tend to move across the routers in a dynamic manner and this eliminates the need for a physical setup. This flexibility has invited more people to take advantage of this technology. Unfortunately, there is also security issues closely associated with it.
ORDER NEW COPY OF VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT & GET HIGH QUALITY SOLUTIONS FROM SUBJECT’S TUTORS!
With business changing their focus from a private server to VPN technology to maximize the performance, the cheap technology makes it possible with a bottomline. The ideal VPN is the one that eliminates delay in packet transfer and has the ability to manage network load without having to worry about security. Further, it is also expected that this technology becomes flexible enough to accept additional hardware or upgrade the existing resources without affecting the response times to user requests. These can proliferate the usage of VPNs in the global market according to Powell (2010).
2. Topic 2 – VPN Replacement Technologies
Discuss the limitations/problems existed in legacy VPNs and recommendalternative options to resolve and overcome the problems of legacy VPNs. Address the issue of VPN security in details as described in common part section.
Answer :
Limitations in legacy VPNs
Legacy VPNs that work based on IPsec-based protocols are now obsolete. The reason is that such protocols could not handle proxies and firewalls efficiently. Again, the remote access problems doubled when the legacy VPNs tried to improve its infrastructure. The other limitation of traditional VPN is the key reuse danger. Though IPsec is termed as the reliable IP level VPN that can ensure peer authentication, integrity, access control and confidentiality, it turns out to be a problem when the attacks originate from unknown sources.
The other limitation of legacy VPN that needs to be highlighted here is the ability to compromise security easily. Since those VPN products are installed on remote workstations connected to local network, the encryption mechanism is unknown. Point to point tunnel protocol was the VPN mechanism used but it was found that this did not guarantee security. It could be due to weak encryption. It is clear that the vulnerability of legacy VPNs to security problems is too high that better mechanisms need to come into picture that can actually ensure flexibility to the users and at the same time has tight encryption mechanisms to control the access and overcome the attacks.
SAVE TOP GRADE USING VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM
Alternatives to solve limitations
It is evident that legacy VPNs encourage easy penetration of firewalls. For instance, Cisco IPsec VPNs were really expensive and did not guarantee compatibility. It is high time that such legacy VPNs either work on the limitations or people look for alternatives. In the global market, there are new VPNs but here are some alternatives to solve the limitations.
- Multi level encryption – This can secure the data at all times and can prevent unauthorized access.
- Continuous authentication – This eliminates the entry of unauthorized users at a random time to gain access to the data.
- Frequent key refresh – This can tighten the security systems and guarantee confidentiality to the users.
- Mutual authentication – When a user tries to access the network from a new device, the mutual authentication through fingerprints or distinct IDs can protect the data and also add value to the accessibility structure.
- Policy enforcement – Due to the widespread usage of mobile VPNs, the best solution is to enforce the policy on all devices. This will keep an eye on the version being used along with the protection of integrity.
DO YOU WANT TO EXCEL IN VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT – ORDER AT EXPERTSMINDS!
VPNs need to evaluate the technology/solution from the perspective of performance rather than features and concept. Even when features are limited, performance tops the list and makes them trustworthy.
Analysis of security issues
Martindale (2015) highlights the DNS hijacking case that can simplify leak of data. In the study, he states that point to point tunnelling protocol along with MS-CHAPv2 authentication seems to be vulnerable to brute force attacks. It is astonishing to note that VPNs that guaranteed credibility and passive monitoring were easily hijacked by unauthorized sources and the entire information was leaked. The actual content was also misused or altered by the hijackers. This is just enough to take a call on the usage of this technology. Though the technology is good, the choice of VPNs is important.
Solutions proposed
Right from connectivity to data access, there are many security problems associated with VPN. Here are the key solutions proposed to address the problems.
- Categorize the security architecture based on the device (SoftEther VPN, 2019)
- Cisco routing platforms have proved to be efficient to enable topology hiding, encryption and origin authentication. These platforms can be used to enhance the efficiency of VPN technologies.
- Relying only on IPsec protocols cannot solve the problem. It is essential to implement service router at all the ends when it comes to corporate VPN.
- There is also tunnel-less VPN solution like GetVPN that can tighten the security of the systems.
For business VPN solutions, the ideal structure is to enable hub spoke model to spoke to spoke communication. This actually improves the quality of service as well. Most importantly, the intrusion detection module has to be linked to database and the switch that will further link to the router and enable communication and data exchange.
Conclusion
In this paper, we have learnt about the key security issues affecting VPNs. Though the idea of using virtual circuits to exchange data is great, there are growing concerns about the internal architecture and quality of service. The report has also covered about the recent attack of data by a hijacker to the DNS. If this is analysed in depth, it is seen that those algorithms that were proved to be efficient were the ones to be easily compromised. Hence, the users of VPN will have to be educated further on choosing the right platform to store, share or exchange data.
Cisco VPNs were once expensive. However, they have now developed customizable VPN solutions that allow data exchanges without any tunnels. The internal cryptographic algorithms have made it possible. The key is to virtualize link bandwidth, data plan and packet forwarding and establish bandwidth that will have guaranteed QoS. Further, the platform has to be worked on different levels – requirement level and implementation level. Once these levels are understood, it is possible to restructure the architecture to address the needs of users at that level.
DONT MISS YOUR CHANCE TO EXCEL IN VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT! HIRE TUTOR OF EXPERTSMINDS.COM FOR PERFECTLY WRITTEN VPN REPLACEMENT TECHNOLOGIES AND SECURITY ANALYSIS ASSIGNMENT SOLUTIONS!
Future Works
Developing VPNs keeping scalability in mind will evolve and sustain in the market. Authorizing ISP everytime the user enters the network will also help users to rely the platform and use it for development. Since the idea is to transform internet free of limits, VPNs can certainly serve as the best solutions to defend the online privacy problems. VPN specific protocols need to be developed so that they can directly be implemented and linked to the network without having the pain to configure or connect the devices. Further, VPNs should not be restricted to 256-bit encryption and the internet kill switch. Instead, they need to be strong enough as per the privacy bill and implement a degree of control to the users.
Customization of VPNs is important. It is essential to integrate it with Google tools so that users do not face restrictions and use it endlessly. These protocols and thoughts to enhance VPNs can guarantee success and sustainability in the global market as the future has great scope for VPN technologies.
Access our Melbourne Institute of Technology Assignment Help services for related units and courses such as:-
- MN501 Network Management in Organisations Assignment Help
- MN502 Overview of Network Security Assignment Help
- MN503 Overview of Internetworking Assignment Help
- MN603 Wireless Networks and Security Assignment Help
- MN623 Cyber Security and Analytics Assignment Help
- MN691 Research Methods and Project Design Assignment Help
- MN692 Capstone Project Assignment Help
- MN621 Advanced Network Design Assignment Help
- MN624 Digital Forensics Assignment Help
- MN504 Networked Application Management Assignment Help
- MN506 System Management Assignment Help
- MN604 IT Security Management Assignment Help
- MN507 Overview of Software Engineering Assignment Help
- MN611 System Architecture Assignment Help
- MN612 Enterprise Architecture Assignment Help