EXPERTSMINDS.COM ACCEPTS INSTANT AND SHORT DEADLINES ORDER FOR STATIC ANALYSIS TOOL ASSIGNMENT - ORDER TODAY FOR EXCELLENCE!
Lab - Exploring the Static Analysis Tool
Question: Write a report on your evaluation of the Fortify On Demand Code Analysis software that includes a screen shot of the report and the sample scan. Discuss how you would incorporate this type of testing in your software development plan.
Solution: Evaluation of the Fortify On Demand Code Analysis software
Fortify Static Code Analyzer (SCA) is a tool that is used to help in the creation of secure application by discovering the present vulnerabilities with less effort and time, all the while, maintaining the quality of code. It is capable of detecting many issues which might go unnoticed by other static testing technologies.
Not only it recognizes the security vulnerabilities in the source code, but it also sorts them by severity and importance, highlighting the root cause providing the line of code details, and gives best suggestions to help developers remove these vulnerabilities that pose the most significant threats.
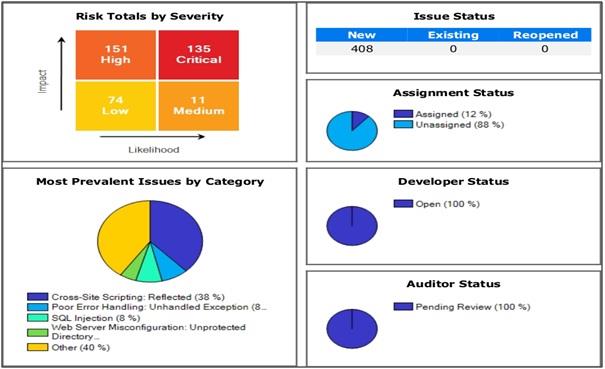
Image 1: Screenshot from the report providing ‘Executive Summary.'
The software offers a 5-star assessment rating to the tested application. This is a measure of the likelihood and impact of problems detected in the application. For example, it gave 1 star to the software tested in our case, which means that high likelihood and high impact(critical) issues were detected. The term likelihood here is a probability measure that indicates the likeness of any detected vulnerability being accurately determined.While the impact measures the possible damage, an attacker could do to the resources of any organization by using the above-found vulnerabilities successfully. High impact and represent the primary issue and alarming the most significant damage. The SCA software orders the issues into four priority labels: Critical, High, Medium, and Low, based on the above two parameters and also tell whether the issue was detected using static or dynamic testing. Critical-priority issues can be easily identified and exploited and therefore, cause substantial harm to the assets. These issues fall under the highest security risks to any application. As such, there is alarming need to correct them all and as per the rules defined earlier so that no issue arises. A well-known example is SQL Injection. Next, we have the most important matters to be insight, they produce large effect with less interest. those matters are not very often detectable and that's why not generally used also but then also give much devastation of valuable things. And therefore, it is suggested that they should be corrected before subsequent releases.
An example of this would be improper password management like a hardcoded password. Next, in line are the medium-priority issues that are characterized by less effect values. generally some matters are important, which can be detected very often and corrected, commonly cause small resource devastation. Generally some matters are often important brought to resolved with upcoming time table of object release. Lastly, are low-priority issues. They are for identifying to utilize which cause very less devastation of valuable things.They can be corrected as the developer wishes. A low-issue example is dead/unreachable code.
NEVER BE CAUGHT IN PLAGIARISM, AVAIL STATIC ANALYSIS TOOL ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM AND SAVE HIGHER MARKS!
The detected issues are presented in the report in two categories: by OWASP Top 10 and by analysis. The OWASP Top 10 list comprises the ten most seen application vulnerabilities like Injection, Cross-site scripting, Broken authentication, etc. In the section ‘Issue Breakdown by Analysis', the issues are classified as static, dynamic, network or monitoring. The report also has an ‘Issue Status' section which can have three values: New(any issue that is recognized very first in the study we perform for the good results as per expectation),Some present(errors common to the previous and the latest analysis) and Reopened(issues that were found during some last analysis, then went dormant, and surfaced the recent analysis again). This software has comprehensive reporting capabilities. Report types include simple executive summaries, compliance reports, and detailed vulnerability information. In the complete report, it gives a summary, an explanation of the issue, recommendations, and a list of references.
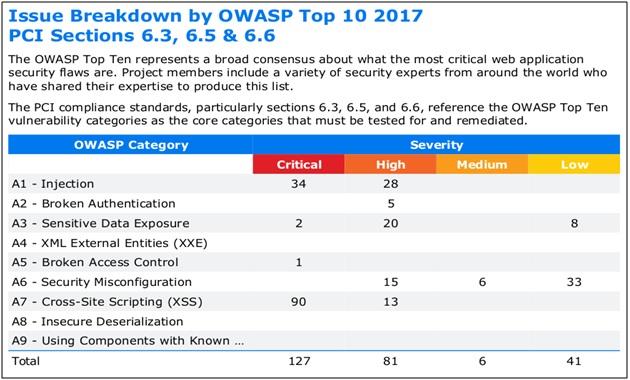
Image 2: Screenshot of the report giving ‘Issue breakdown by OWASP Top Ten.'
SDLC is the process of planning, creating, testing, and deploying software. The process helps to develop a set of defined requirements within each phase of the lifecycle so that in the end, we have a high-quality product. Implementing this also ensures that security is inherent in the software design and development phases. This approach identifies vulnerabilities early in the lifecycle when they are the least expensive to fix, and educates developers about creating more secure software.
Analysis of the source code identifies security vulnerabilities efficiently. When done early in the development lifecycle, it identifies and helps resolve issues with less effort, time, and cost. It is recommended to be used continuously throughout the life of the application. This Static Code Analysis technology gives instant feedback on issues present in the source code in the development phase, discovers vulnerabilities, and aids programmers to create a more secure and robust software.
Since it shows us the bugs before the software has gone into production, it saves a lot of cost to the organization. Helps produce good results with accurate result which is a good thing about this study. Not only this, it helps the developers understand their software better and improve it to get enhanced outputs and satisfy their clients better.
It does not provide unnecessary information and does not generate a massive number of false positives. Also, cleaning out the false positives from the results manually is very easy("With Great Effort," 2018). One of it's greatest strengths is that it addresses the source code scanning and dynamic scanning in a distinct, correlated way.
Summary
In this project, we studied about performing static analysis using the Fortify Static Code Analyzer software available online. We chose an application(WebGoat(.NET)) and obtained a static assessment report after passing it through the scanning software. Then we analyzed this report to understand the various terms used and their significance. We also studied how static analysis could be of relevance to the software development process.
GET ASSURED A++ GRADE IN EACH STATIC ANALYSIS TOOL ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!