NEVER BE CAUGHT IN PLAGIARISM, AVAIL NETWORKING PLAN ASSIGNMENT HELP SERVICE OF EXPERTSMINDS.COM AND SAVE HIGHER MARKS!
ICT703 Network Technology and Management - University Of The Sunshine Coast
Executive Summary
This report includes a complete description of networking and communication plan. It involves certain activities related to the project that involves proposing a computer system, fulfilling FTP requirements, developing a networking layout, procuring devices, security planning, and installing the relevant devices in the company. The main focus of the report is on VPN Routing security plan and have provided recommendations to the company to adopt it. Budget planning and summary have also been included in the report.
Introduction
In this world of advanced technology, every business wants to thrive in the best level. For this purpose, there is a need to enhance the technological measures to meet the needs of the customers (Lee, 2014). In this case, Priority Advertisement Company is working on a networking and communication plan, which is important for security purposes. The main objective of the project is to enhance the IT services and products of the company to satisfy customers and employees. Within the enhancement of the products, it is necessary to provide complete protection to the networking system and other I.T devices.
Basically, this report focuses on the certain concepts and services of a complete networking system which include certain controls and devices such as computer systems, routers, security plans, communication plans, networking plots etc. First of all, an interview is conducted with the management to understand the basic needs of I.T system in the company. Moreover, this report also focuses on secondary research, which is conducted to fulfil basic requirements of the company within network and communication plan.
Need Statement
Need a statement of the project is to provide proper planning for the advertising company in order to maintain the network plan, operation and network security. The main target is to serve the company with the highest level of integrity and solutions for the enhancement of business operations. Another significant need for the service is to plan the cost-efficient budget while reduction of total expenses of the operating systems. Advertisement of the products and amenities on the social sites and webpages of the company is also included in the targets of the plan.
Objectives
Objectives are to address all the communication requirement by providing an efficient networking plan conferring to the priority advertisement. Numerous objectives are there which are significant to be completed, and these include:
• Graphic production purpose
• Expansion of proper network layout plan
• Proposal for computer systems
• Documentation of security services
• Updating of networking services
• Developing the addressing and subnetting structures
• Proposing measured network access.
Methodology and Timetable
For the surety of network efficiency and productivity, desktop research was performed. Obtaining access to the latest and most recent technological advances, drifts, and security settings. Numerous websites, organizational webpages, courses and articles were visited while performing this survey. This survey also included in reviewing the templates, methodologies of the other competitive companies.
|
Task
|
Initiating Time
|
Completion Days required
|
|
Purchasing of Molding machines
|
25 Sept.
|
2
|
|
Interviews
|
27 Sept
|
2
|
|
Training
|
30 Sept
|
44
|
|
Reportage
|
08 Oct
|
1
|
|
Documentation
|
09 Oct
|
1
|
|
Performance Enhancement
|
11 Oct
|
3
|
|
Devices and Implementation
|
Price
|
|
System of computing for graphic production
|
$9,000
|
|
Computing Systems for General Utilization
|
$8,000
|
|
Proposed Network
|
$40,000
|
|
LED Monitoring Devices
|
$3,000
|
|
Implementation of Network Access Control
|
$20,000
|
|
Total Cost
|
$ 80,000
|
GET ASSURED A++ GRADE IN EACH NETWORKING PLAN ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!
Activity 1 Propose a computer system for each of the specific uses, i.e., general use, graphics production and film production. Search the Internet or local sources for availability and pricing information.
Solution:
In a company that is focused on the niche of priority advertising, there need to be various activities that are impossible to execute in the absence of a computer. The nature of the work that is being executed and the department that is working on the computer will be determining the variance of the activity. There are both kinds of tasks that will be executed as the task associated with general usage and the tasks that involve the execution of the daily operations. The communication on the emails is also executed on the basis of the internet and is impossible to attain without it (Stanko, Taryn and Sena, 2019). The making of the essential presentation and its delivery is also attained with the help of a computer. There needs to be specific research that will be associated with the campaign betterment and the fight to gain the most optimum work done. In the course of all these actions it is extremely essential to get the hang of a computer that will ease the working associated with all these tasks. Even the most fundamental organization ceases to work without computer systems. Our organization is based on the Priority advertisements has most of its function governance that will be executed solely with the help of a computer.
The computers will have a specific recommendation. That would be sufficient enough to carry out the assignments associating the tasks that are carried out on an everyday basis by the general computer. In these certain and specific recommendations including the processor of Intel i5 of the seventh generation, or AMD ryzen 5 there needs to be the time frame base of the 3.9 gigahertz. The memory should be sufficient enough as 4GB and cache 6 MB. The system hard drive needs to have the work commencement ability of the 550GBs internal to external(Noel, Babor and Grady, 2018). CD-ROM that can read and write the CD/ DVD format files. For the sake of graphical usage, we need to have a system that is a little bit of further fetched recommendations. For the sake of the proper execution of the system framework that can carry out the tasks associated with advanced nature of work. AMD Ryzen 8. 4 gigahertz ad 7 cores RAM. Sufficient memory of 5-8GB.
Activity 2 Use the following form to propose a server that can support their email and FTP requirements. Server Planning Form
Solution:
|
Location
|
Brisbane
|
|
Component
|
Recommendations
|
|
Processor
|
Intel i7 with 2.4GHz
|
|
Memory
|
8MB Cache and 8GB RAM
|
|
Hard Drive
|
1TB Internal Hard Drive and 500GB of External Hard Drive
|
|
CD-ROM/DVD
|
8X 12X Read and Write CD/DVD ROM (Amazon, 2019).
|
|
USB Ports
|
8USB ports hub (Amazon, 2019), These ports will be located on the standard location 1 which is the front of the tower, and there will be a 4 USB ports hub which will be located on the back of the tower (Hose, 2017).
|
|
Video Card
|
NVIDIA GTX 1080 Ti 8GB (Nvidia, 2019).
|
|
Sound Card
|
Creative Sound Blaster Omni (Kimari, 2019).
|
|
Modem
|
Net Gear CM400, speed up to 343Mbps that features almost 8 downstream and upstream with 4 channels which contribute greatly to making the internet system more reliable (Phillips, 2019).
|
|
Network Card
|
TP-Link TL-WDN 4800 network card, profile bracket that is low, the dual-band that is durable, three antennas, plug and use design, faster speed (Pech, 2019).
|
|
Operating System
|
Windows 10 Enterprise (Microsoft, 2019).
|
|
Monitor
|
Dell Ultra Sharp u2414H, 23.8 inch screen size, LED monitor (Amazon, 2019).
|
|
Printer
|
Brother HL L8360 CDW, overall printing quality is excellent, faster printing speed, low running cost, and paper capacity are highly expandable (Harrel, 2017).
|
|
Speakers
|
KEF LS50 Wireless speakers, Wi-Fi streaming is supported, audio can be streamed up to 192KHz and 24Bit resolution. RCA, USB-A, and optical supported (Parker Hall; Quentyn Kennemer;, 2019).
|
|
Internet Connection
|
Internet connection will be both Ethernet and Wireless. This will be based on requirement and ease in providing network services to relevant departments and their usage.
|
ORDER NEW COPY OF NETWORKING PLAN ASSIGNMENT AND SECURE HIGHER MARKS!
Activity 3 Develop and demonstrate a complete network layout plan for Priority Advertising requirements. Because the company has limited funds available for this project, it is important that where possible only equipment designed for the small business and home markets be used.
Solution: Network Layout Plan
The network layout plan for Priority Advertising is provided below.
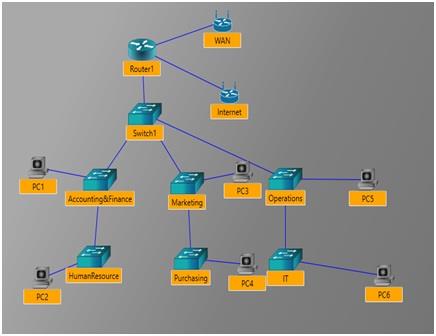

Above is the network layout plan that is proposed for the Priority Advertising Company. This network layout plan should be considered for all the floors of Priority Advertising. It is prepared in accordance with the requirement of Priority Advertisement and their need for having an effective and efficient plan that will provide better, faster and effective communication through such network layout.
The network configuration diagram of the network plan is provided below for the whole network.
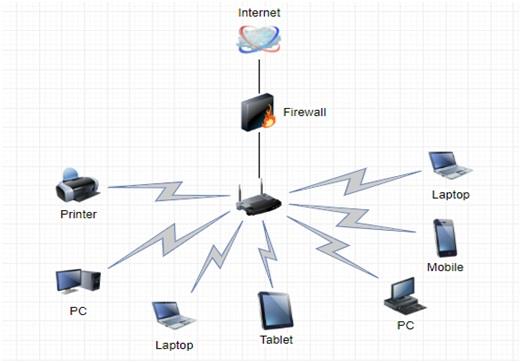
Figure 1 Network Configuration Diagram for Priority Advertising Company
Activity 4 After the end-user systems and network layout have been selected, it is time to look at the workflow and decide on any shared components and network technology to support this workflow.
Solution:
Printers/Scanners
There are certain best printers/scanners in the market with some latest specifications. A business requires a different type of printer/scanner at an affordable price (insight, 2018). Some of the printers are presented with low tier offers to price under 500 dollars. Such type of printers/scanners is ideal for small work-groups. One of the best choices of a medium-sized company is HP's M552DN as it has decent print speed and healthy paper capacity. It is a good choice for the organizations that wanted to protect their sensitive data. It is available in the market for 390.96 dollars. Similarly, Canon Image Runner printer can also be the best choice available at $15,000.
Access Points
The access points that can be selected for the Priority Advertising Company is Zyxel NAP303 Nebula (B, 2019). It is a wireless access point that relies on the smart antenna to eliminate any kind of interference. It was created to integrate a larger network of compatible access points. However, it is operated within the Nebula management platform to be remotely managed and monitored alongside other devices. It gives an option to its users to be updated easily; that's why the designing of the access point is considered as more industrial. It is available at an affordable price in the market of about 146.57 dollars. Just like Zyxel Ubiquiti, UAP-AC-PRO is also wireless access points with the same specification but with a low price of $125 (amazon, 2019).
Switches
There are different types of switches that can be useful for the company, such as TRENDnet TPE-LG80 Ethernet Switch (B, 2019). It allows the users to connect to a large number of devices in a plug and play manner. It is built-in common way like other switches and supports about eight of the ports. It offers QoS and VLAN port isolation. It can be extended up to 656 feet and at 10 Mbps full-duplex. It has a perfect design and surface which allows the user to place the router on a float mount on the wall. Similarly, TP-LINK TL is a switch port which manages some of the best networking products with features of rectangular metallic case available in $109.99 (amazon, 2019).
Routers
The D-Link AC2600 can be the best choice of routers for the Priority Advertising Company. It is a dual-band router that offers tight security with robust parental controls (Delaney, 2019). The Intel of the router is based on Wi-Fi chipset. It is a cube-shaped router that uses MacAfee's Secure Home Platform to protect every single device. It has good speed as it is installed in minutes and performs faster. It can be procured by the company for just 199.99 dollars. On the other hand, TP-Link Archer C7 AC1750 is another router that can be of best use for the company available in the lowest price of $69.99 (Delaney, 2017). It scores between 2.4GHZ and 5GHz throughput tests.
EXPERTSMINDS.COM GIVES ACCOUNTABILITY OF YOUR TIME AND MONEY - AVAIL TOP RESULTS ORIGINATED NETWORKING PLAN ASSIGNMENT HELP SERVICES AT BEST RATES!
Activity 5 It is necessary to plan the Internet connectivity, and which services are provided by the ISP and which services must be provided in-house. Larger companies usually provide services in-house, while small businesses and individuals normally rely on an ISP to provide these services. Most ISPs offer a variety of services and service levels.
Solution:
Internal Services regarding networking and security
With the passage of time, different security parameters have been established that are benefiting certain business operations. In this case, security threats of networking system have been increased, which need to be solved. Priority Advertising Company is trying a lot to provide security to the company both externally and internally. The main objective of the company relies on reducing the imminent threats and securing overall network under which the company could easily operate without any fear. This could be done by protecting devices, external drives and other computing devices.
For this purpose, the company can consider the services of MitechOne, which is a leading information technology system and provide secure networking services (MitechOne, 2017). It does provide security to the internet, PDAs, smartphones and beyond these devices. It simply tries to provide accessibility to another country through which a company can easily enhance productivity and collaboration. Moreover, company can also use the service of AT&T which offers a number of cybersecurity products and services (AT&T Business, 2019). With the help of these services, company can secure the whole network and will allow the customers and employees to work in a safe environment. It can provide the best opportunity for the company to form a stronger and loyal relationship with its customers internally and externally.
Both of these security companies can manage and provide monitoring services too. It can provide assistance to the company in managing certain tasks, keeping track of the programs, providing quality services etc. It can be a beneficial situation for the company and for the customers. The cybersecurity devices will keep the company away from critical situations such as information threat or stealing of personal information. It will create certain firewalls in every computer system that will protect the operations of the country from dangerous situations.
|
ISP Name
|
Service
|
Network
|
Security
|
|
Access Providers
|
Provide internet access
|
Integrated Service Digital Network
|
Synchronous optical security
|
|
Mailbox Providers
|
Service for hosting electric mail domains
|
Simple Mail Transfer Protocol
|
Protect mails of organization
|
|
Hosting ISPs
|
Provide email, web-hosting, online storage service
|
Virtual Network
|
Malware Protection
|
|
Transit ISPs
|
Pay upstream for internet access
|
Point of Presence
|
Protection to hosting bandwidth
|
Activity 6: Devise subnetting and addressing schemes for Priority Advertising. The schemes must provide servers and some other network devices (where necessary) with a static address and allow all other hosts to be configured via DHCP. Identify and list the details of all internal and external subnets and the ranges of useable IP addresses (and default gateways) for DHCP within each internal subnet, and also assign an appropriate IP address (and default gateways) to network devices that should use a static IP address.
Solution:
Subnetting and Addressing Schemes for Priority Advertising
|
Subnet
|
Network Address
|
Subnet Mask
|
First Usable IP address
|
Last Usable IP address
|
Broadcast Address
|
|
00000010
|
10
|
256
|
192.168.1.1
|
192.168.1.62
|
172.16.31.255
|
|
11111111
|
0
|
128
|
192.168.1.65
|
192.167.1.126
|
172.16.63.255
|
|
00000010
|
0
|
64
|
192.168.1.129
|
192.168.1.190
|
172.16.95.255
|
|
2
|
0
|
32
|
192.168.1.193
|
192.168.1.254
|
172.16.127.255
|
|
Device
|
Interface*
|
IP address
|
Subnet Mask
|
Default Gateway
|
|
5 Buttons
|
NIC
|
192.168.1.1
|
256
|
172.16.1.0
|
|
10 Buttons
|
NIC
|
192.168.1.65
|
128
|
172.16.12.0
|
|
1 Analog stick
|
NIC
|
192.168.1.129
|
64
|
172.16.1.5
|
|
2 Analog Sticks
|
NIC
|
192.168.1.193
|
32
|
172.16.12.1
|
The above tables describe the subnetting and addressing scheme for the Priority Advertising Company. It basically provides servers the relevant addresses and hosts to configure the whole system. It identifies the internal and external subnets and ranges for the IP addresses that are usable with default gateways for DHCP within the subnets that are internal. The assigned IP address and default gateways to the network devices.
ENROL WITH NETWORKING PLAN ASSIGNMENT HELP AND HOMEWORK WRITING SERVICES OF EXPERTSMINDS.COM AND GET BETTER RESULTS IN NETWORKING PLAN ASSIGNMENTS!
Activity 7: Priority Advertising is concerned that their files and resources may be vulnerable through the wired or wireless networks. Explain how the use of public and private IP addresses together may address this concern and provide a security plan that allows only Priority Advertising employees to connect to the network and gain access to company information and resources.
Solution:
When there is an advancement that is being commenced in this world there will be advancement in all the fields associated with threats. There are various aspects of the malicious software that can intrude the system and get the information either compromised or deleted(Mathur, 2019). In order to rid all these threats and issues that are associated with the aspects of the information storage and the system framework, all the same, it is quite essential to gain complete security means to our work that is being performed, and it needs to be protected well. A measure is to be taken in order to prevent the intrusion of the solicited access to the system. This is the manner in which the intrusion can be prevented, and this measure is better than the one that is opted to combat the after-effects of the situation and to deal with security breach. There is a need to be certain measure of the collaborative that can be undertaken to avoid the scenario that can prevail the company. The workforce needs to be firm and well-executed after complete thought so as to undermine the factors that are associated with breaches of cybersecurity.
One such measure is the measure of VPN routing. In this method, there is a specific kind of environment that can be created in an exclusive manner to avoid the intrusion from the outside virtual private network. This eases the communication between the authorized VPNs and also maintains a perspective of secure cyber environment(Kim et al., 2017). If these VPN devices are located in a remote position, still they will be able to maintain communication with each other to get work done in a safe and secure cyber environment. In this manner there can be sharing of the contents and services associated with communication within the VPN. Hence the different end devices are allowed collaboration to give them the satisfaction of coordination and allow selective traffic through the router.
Recommendations
A proper security plan has been formed to protect the devices from malware attack, cyber threats and other security threats. Such type of security threats can be removed by using network security services provided by AT&T and MitechOne. After a conclusion and evaluation, some of the recommendations that can be given to the company are as follows:
• Adopting and implementing a proposed plan without any complications
• Ensuring the growth of services
• Increasing the effectiveness of the operations
• Implementing certain security measures
• Restricting access to unauthorized members.
Conclusion
The basic objective of the report is to form a networking and communication plan based on the nature of the work or the operations. For a proper networking and I.T system, it is necessary to consider quality devices, such as routers, switches, access points etc. that can form a complete networking system. Moreover, subnetting and addresses have also been identified within the proper networking system, along with proper equipment and devices. A proper budget plan has been deprived related to the project of Priority Advertising Company.
24/7 AVAILABILITY OF TRUSTED NETWORKING PLAN ASSIGNMENT WRITERS! ORDER ASSIGNMENTS FOR BETTER RESULTS!
Access our assignment help service for below mention course:-
- ICT704 Cloud Database Systems Assignment Help
- ICT702 Data Visualisation Assignment Help
- ICT707 Data Science Practice Assignment Help
- ICT700 Systems Analysis Assignment Help
- ICT709 ICT Industry Project Assignment Help
- ICT701 Managing Data Assignment Help
- ICT706 Machine Learning Assignment Help
- ICT708 ICT Internship Assignment Help
- ICT703 Network Technology and Management Assignment Help
- ICT710 ICT Professional Practice and Ethics Assignment Help
- ICT705 Data and System Integration Assignment Help