MN603 Wireless Networks and Security Assignment Help
Assignment Description
Smart home or home automation technology provides homeowners' security, comfort, convenience and energy efficiency by enabling them to control smart devices, via an app on their smartphone or other networked device. This technology enables you doing things such as turn the lights on/off, stream music to a speaker, lock/open the doors remotely, and much more.
This assignment aims to simulate a smart home using IoT technology in Cisco Packet Tracer. Students will purely practice with the IoT component offered by the Cisco Packet Tracer to be used in the home. Those IoT devices will be connected to the home WLAN that enables the users to control the things through wireless technology. The users should also be able to control the things when they are outside home (remote access). This means the WLAN should be connected to a global network that enables the users to have control on devices when they are at work. Hence, there is another WLAN at work that is connected to the global network. Note, you need to make sure that the WLANs are secure.
This assignment requires the students to design, analyse, and implement a smart home, considering the ethical implications. The students are required to complete the following tasks and submit a report on Moodle.
1. Explore the ethical implications in the design and implementation of WLANs.
2. Design, analysis, and implementation of a smart home WLAN and an enterprise WLAN where the following aspects of security should be considered:
a. Confidentiality
b. Integrity
c. Availability
d. Authentication
e. Authorization
3. Test and prove a successful of connectivity between users and IoT devices when they are at home and when they are at work. You need to take a snapshot for each step of testing followed by the explanation.
4. Demonstration in Week 11 during the Lab.
SPARKPLUS
SPARKPLUS is Self and Peer Assessment and Feedback for group assignment. It is an individual and compulsory task for each student. SPARKPLUS RPF factor is a value between 0 and 1 which is generated by the SPARKPLUS website as soon as the group members do the SPARKPLUS review task. Please read Student's SPARKPLUS Guideline in the assignment folder for how to use it.
Dont miss your chance to excel in MN603 Wireless Networks and Security Assignment Help solution! Hire tutor of Expertsminds.com for perfectly written MN603 Wireless Networks and Security Assignment solutions!
Introduction
Home automation is the task of automating and makes communicating electronic devices, electrical devices and technology based devices of home with reduced the human interfaces. To make home automation, it requires various hardware, software and network devices. Home automation is otherwise called as demotic. The home that has automation is called as smart Home. An example for such smart is when the person enters into the home the door will be opened automatically. The person sits on sofa the television and fan will be turn on. When the person start sleeping the television will be turned off or volume will be reduced. This is an example for home automation or smart home. The smart home makes human being more comfortable and luxuries. It reduces most of the human task at home.
Application of home automation
• Computer enabled air conditioning system
• Installation of internet to all components of home
• Security devices are enabled with internet features such a surveillance cameras
• Connect and communicate electronic and electrical appliances of home
Advantage
The advantage of home automation is remote accessing, controlling and monitoring of home devices. For the home automation, monitoring apps are used to monitor the entire devices in the smart home and updates the current status of the devices. The fully controlled system give the details of whether is door is opened or close, lights or switch on or off, any gas leakage exists or not. The surveillance camera capture any potential system, home automation can be made to send the alert message to the house owner or to the nearby police station. If there is any gas leakage occurs, the automated system can send the information to the nearby fire station. Apart from the security system, the user can manage the entire home from the remote location. The user can switch on the light at day time, switch off the light at night time etc.
Many manufacturing companies are continuously delivering smart devices and sensors for the automation tasks.
The components or devices of home are connected and communicated through either wired medium or wireless medium. The home automation system requires management software for the entire system, sensors for motion as well as temperature, controllers.
Ethical implications in the design and implementation of a secure enterprise wireless network
Wireless networks are increase more in most of the places such as business organization, homes and educational institution etc. The transmission medium for wireless network is air. The medium has the ability to connect with unknown devices until deploying the security features for the Wireless network.
The standard 802.11 provides various security features for wireless transmission. The transmission medium of wireless network is open. The control for this medium is limited. The physical medium has the control over the transmission. The transmission waves can be received by anyone in the air using radio receiver.
Wireless network face a big problem in data security. It is very important to enabled security features’ for the transmission medium. The wireless access can be accessed from anywhere. Network has deferent protocol. Each protocol has different security mechanism. Protocol information is highly confidential for transmission.
Eavesdropping is one the attack for the encrypted data. It extracts the encrypted data. Injects is another attack where the packets are hacked. The hacker attack tries to adopt the security features from the internet.
While the user is accessing the wireless network the attacker trying to access the users. The interference attack is another type of attack. In this attack, the attacker blocks the server for the user access with the server. Attack the highly confidential details such as bank account details.
The protocol 802.11 offers certain security features such as authentication with shared key, authentication with secured system and authentication with centralized.
Wireless Smart Home with Internet of Things
Various approaches are available for home automation such as internet of Things with cloud, Wi-Fi connectivity with smart phones, applications of android with remote access, home automation with RF etc.
Home automation using Wireless Local Area Network with Internet of Things is an emerging technology to control the home devices remotely.
Project Requirements
- Devices of IoT
- Server of IoT
- Wi-Fi router
- Model
- Switches
- Routers
Design, Analysis, and implementation of a smart home
Smart home involves the connection of electronic devices in the home and centralized controlling over the devices. The devices in the smart home are communicated with each other. The appliances of home like television, security system, refrigerator, lighting system, desktop, laptop, watering system etc. are all interconnected and accessed remotely. Mobile is the small devices which is available in most of the hands. Through the mobile the entire home can be operated through the internet.
Rapid Application Development is selected for the implementation of smart home. This model is powerful for the implementation of software. This model is the incremental model, function and components required for the implementation of smart home is developed parallel.
In RAD model, the entire project is divided into small functions. Each function is executed individually. At last, all the functions are combining to complete the entire project. Each function of the project has various sub functions such as analysis, design, code and then text. The model completes the project with short time. The model completes the project within 60-90 days.
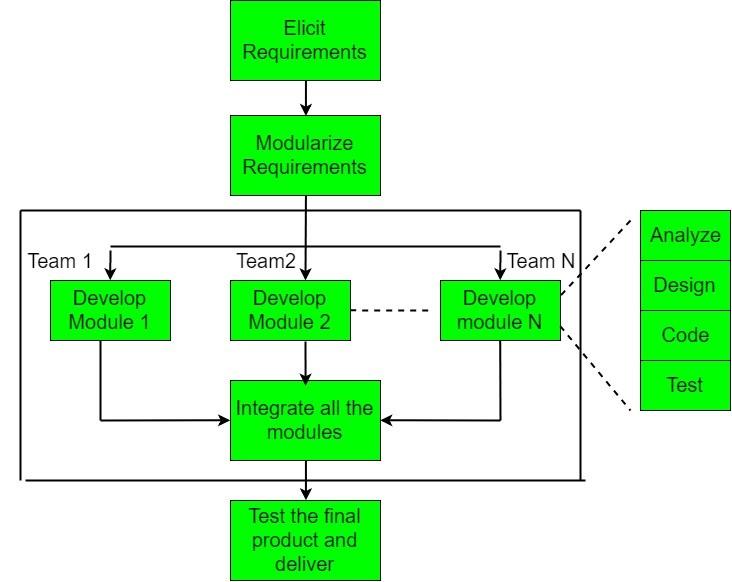
The RAD model has various phases such as planning of requirements, description from user and construction.
Planning of requirements
It includes various techniques to collect requirement for the project using various techniques such as analysis of forms, analysis of task, scenarios of users etc. based on that retirement, the final model will be created
Description from user
This phase developing the proto type with the user specified requirements. In this phase, the requirements are reanalysed with the users
Construction of the model
The actual model is constructed with the powerful tools. It transforms the user requirements and prototype type into the actual working model
Construction
The independent modules are combined and interfaces are established in between the modules to make the complete working model.
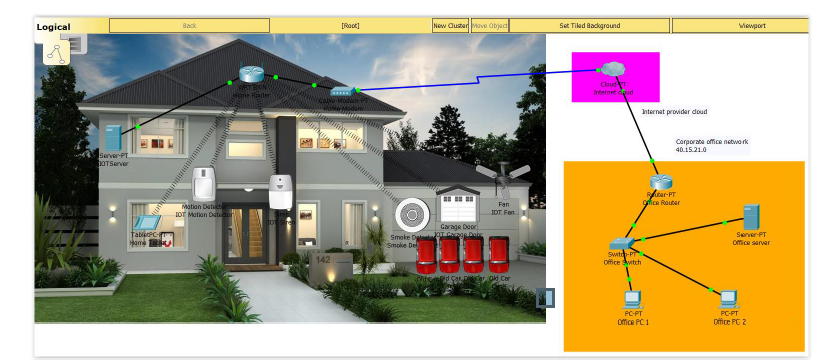
Logical design of smart Home
The logical design of smart Home depicts the home with wireless LAN is connected with enterprise WLAN. The home is controlled from the work place. Both stations are connected through cloud internet.
Physical design of smart Home
The physical design illustrates the smart Home is constructed with different hardware devices, software devices and network components such as switches, routers, model, cables, internet cloud etc. All the physical components make the actual implementation.
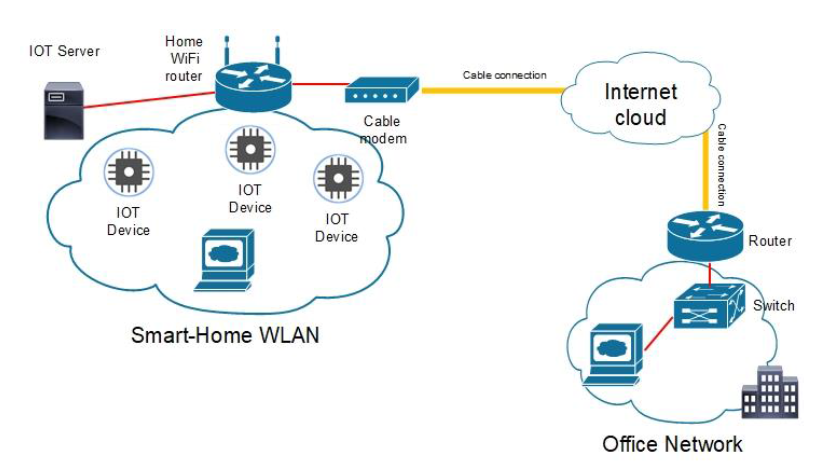
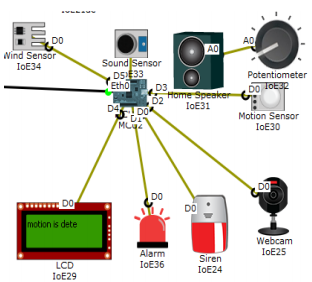
Below diagram shows that a smart IoT based automation in WAN with enterprise connected to the public cloud
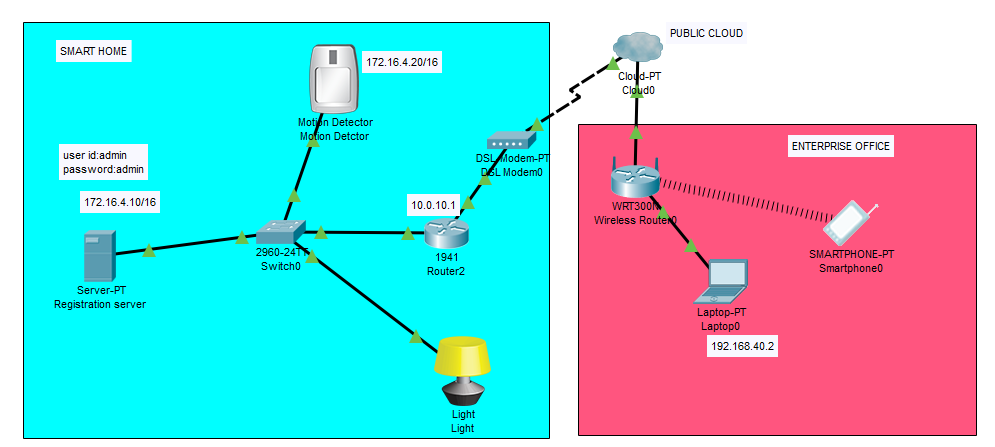
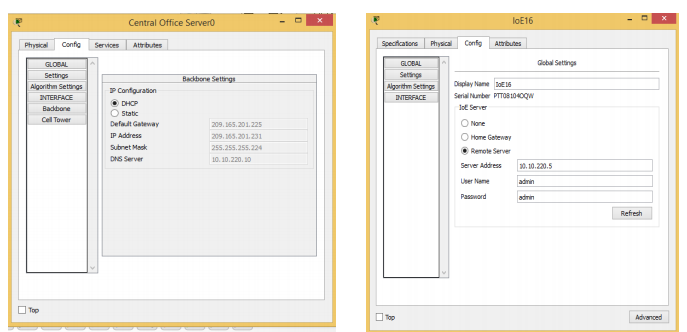
Here we have selected the Server-PT, Switch, Motion detector, Light detector connected to the server and then to cloud.
In the enterprise we have the WAN connection established with Wireless router to the office devices and in-turn connected to the Public cloud.
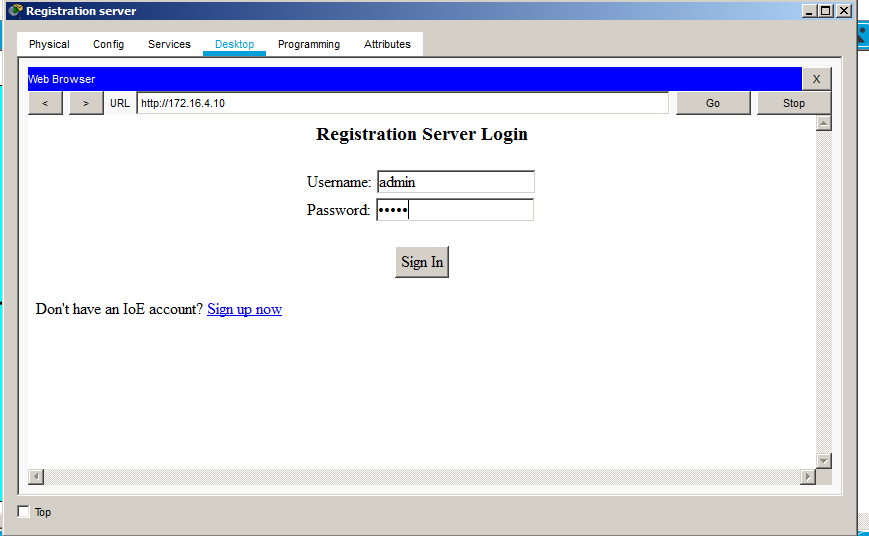
Below Figure gives that Registration server login for the IoT devices. In the login we have
User Name: admin, password:admin
After logging we need to configure each IoT devices to be connected in the network and firewall is setup.
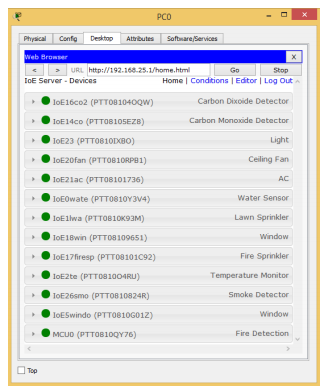
After logging in to the server we can see the status and get to know how it could be connected.
Each device configuration are shown and their activation is shown. If any fault in the circuit then here we could find the problem and can be rectified.
IP configuration for each devices are done the method to do is to configure at each entry point.
The end point could be the output device connected.
Testing:
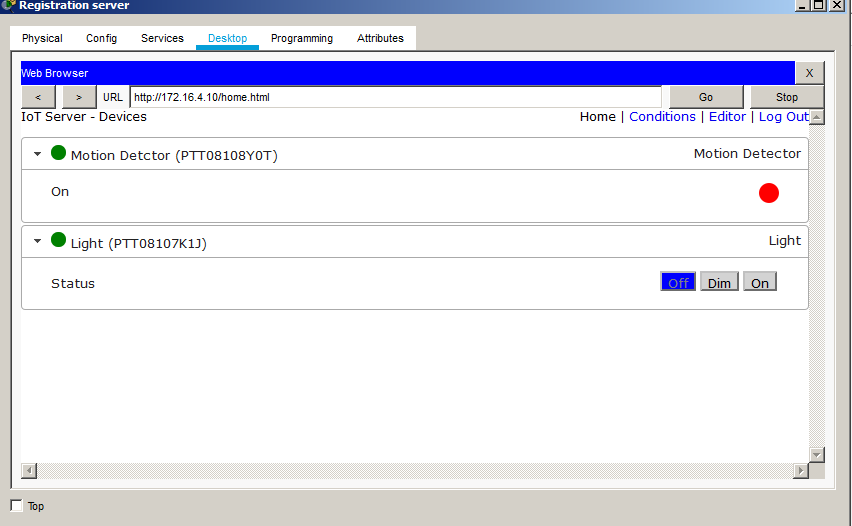
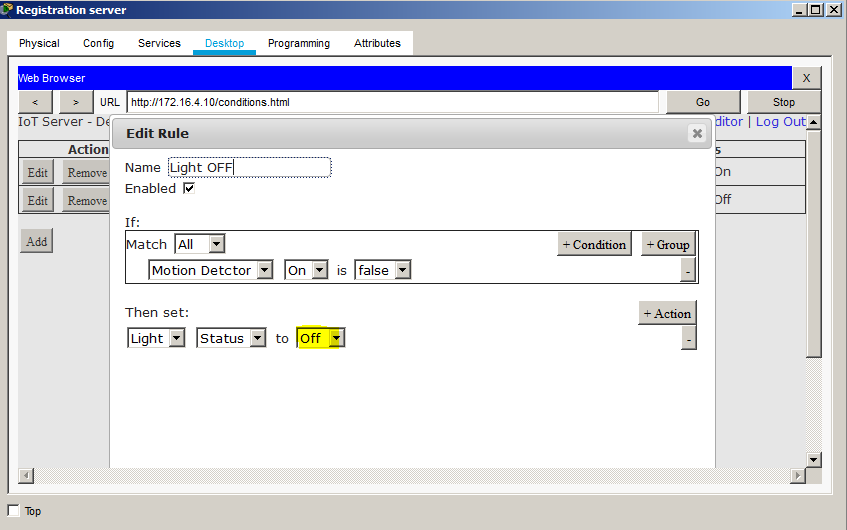
The devices could be tested in the web server by addition of any rules. The rules could be when motion detector is ON, then we could switch ON the Light.
The below rules are configured for LIGHT ON conditions
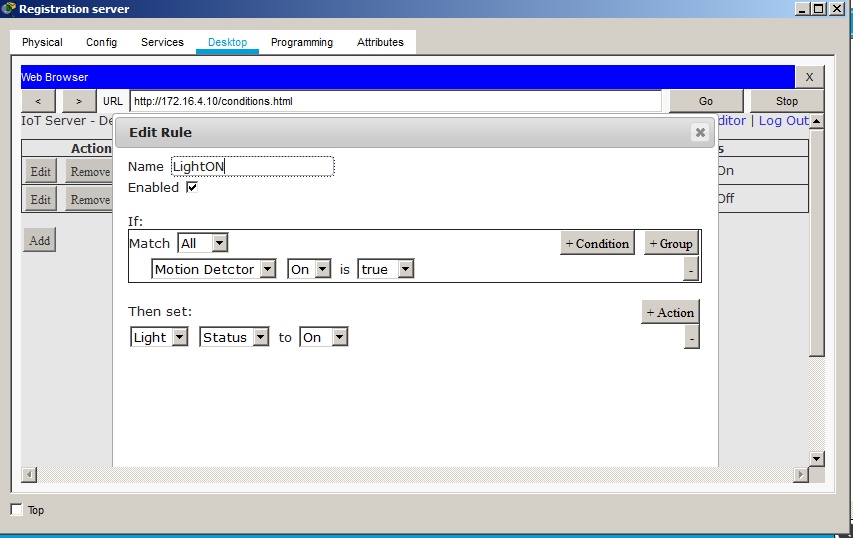
At the same time, by default when the Motion detector in FALSE, then we could see the Light Status to OFF conditions. These values can be viewed in Wireless devices which is configured to provide the monitoring status.
The below diagram shows that when the sensor is ON, we could enable the LCD to display the message and provide an alert to the mobile phone which is out of the current network. But the network will show the full status.
Security aspects for smart Home and enterprise WLAN
Smart home inter connect all the devices of home through internet. Internet is the large network. It includes many vulnerabilities and threats. It is important to secure the devices of the home. Otherwise it will lead security vulnerabilities for the home devices. Security features are provide the security for the networked devices from the attacks. The most important security concepts are confidentiality, integrity, availability, authentication, authorisation and access control.
Confidentiality
Confidentiality is the concept deals about the protection of information from an authorized access. No authorised persons should not access the information. The information should be confidential between the two parties of communication. Confidentiality can be achieved cryptographic keys such as public key, private key.
The sender uses the key and transmit the content into encrypted format. The content cannot be read by everyone. It is an understand format. Using the decryption key either the same key of encryption or other key is used to decrypt the information.
Another way of achieving the confidentiality through the network is VPN. Virtual Private Network provide secured transmission through encryption. The transactions are transmitted over the network in an encrypted format.
Integrity
The information or data should not be altered by authorized persons. The information should be trustworthy. Only the authorized person only can modify the data. In smart home the devices can be controlled only by authorized person either locally or remotely. The unauthorized should not be allowed for accessing and controlling the devices.
Availability
The data should be available for right person at right time. The hacker or attacker hacks the data. The data may be deleted, encrypted, moved to other locations etc. due to hacking. But the trustworthy data should be available.
Authentication
To access the resources on the network, the user should prove the authenticity whether the user is the legitimate user to access the resources. This process is called as authentication. To access mail system, users are providing email and password. This is an example for authentication. The user is proving their authenticity to access the resource.
In smart home, to control the devices the user should be the authorised person. That information should ne authenticated.
Authorization
The task of assigning rights to the user to access the resources is called as authorization. Only the authorized users can access the resources. To access the resources, some systems require finger prints. When the finger prints are true means the user can access the resources. Otherwise cannot access the resources.
Access control
For the authorised person, access right over the resources are fixed by the administrator. Access right includes read, write read and write etc.
Fixing security policies for smart Home devices
• To make more secure connection using strong Wi-Fi encryption is preferable. It make the communication more secured
• Don’t assign the name for the router as the name given by the manufacturer
• Create separate network to access IoT devices. Don’t allow other network to access the IoT devices
• Use authorization details to access the IoT devices. The program embedded in the IoT device verify the authenticity of the users.
• Create accounts for IoT devices, routers to block unauthorized access into the local network
• Fix strong unbreakable password for accounts
• The firewall and antivirus software are updated frequently
• Disabling the unwanted features of IoT
• Frequent check of the IoT Devices
• Block public network into IoT device private network
• Monitoring vulnerabilities
Conclusion
Smart home or home automation enables the users of home to control the different devices of home. The system make the device to communicate and interconnect with each other. This make the home environment friendlier with the devices. The human tasks are reduced more. The management of home is very simple either locally or remotely.
The system improves the security features for home. Various technologies and techniques are supported for home automation or smart home. One such innovative and latest technology is the IoT. The project used the IoT technology for the automation of home with Wireless LAN. The proposed system controlled the IoT devices either home or at work.
The project included the logical design, simulation of smart home with WLAN connection and the cisco packet tracer is used for simulation of Smart homes. The Network shown in the Logical design gives the user to connect any number of IoT devices provided the Security is ensured by having VPN connection established.
Are you looking for reliable MN603 Wireless Networks and Security Assignment Help services? Expertsminds.com is right choice as your study partner!