ARE YOU LOOKING FOR RELIABLE DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT HELP SERVICES? EXPERTSMINDS.COM IS RIGHT CHOICE AS YOUR STUDY PARTNER!
MN504 Networked Application Management Assignment - Network Analysis using Wireshark, Melbourne Institute of Technology, Australia
Purpose - This assignment is designed to develop deeper analytical understanding of different distributed network conditions. At the completion of this assessment students should be able to:
a. Analyse performance and deployment issues for networked applications;
b. Compare appropriate industry tools and techniques to manage networked applications;
Description - The aim of the assignment is to develop an analytical understanding of performance and management of different types of networked applications. The assignment will provide an opportunity to understand network performance and management issues of networked applications using state of the art tools. These exercises provide an opportunity to demonstrate analytical ability of evaluating distributed systems performance, Quality of Service and service management.
Answer - Network Analysis using Wireshark
Project Scope and Overview
The purpose of the undertaking is to develop an interpretive understanding of execution and the leading group of different sorts of composed applications. The undertaking will allow to get orchestrate execution and the administrators issues of organized applications using top tier gadgets. These exercises allow displaying orderly limit of surveying circled systems execution, Nature of Service and organization the board.
There is a need to catch parcels on two systems, at their home system and at MIT arrange while getting to the accompanying sites. One site is of a news channel and the other one is a site for live spilling. The understudies are required to catch bundles of various pictures from the news channel site and catch parcels from the live stream site while spilling for 10 minutes once at MIT in a gathering and after that on their home system separately.
In assessing application limit necessities we need to think about applications that require a lot of limit just as those that require a particular esteem (crest, least, supported) or scope of limits. The sniffing tools like Wireshark or NMAP are tools that can get the information using TCP or UDP protocols for the outgoing and incoming packets, this make the users easily detect the data flow and the packet loss , the reasons for this loss. The packet loss is not only the reason for using these tools, the throuput, delays and the IP address of servers and illegal attacks on the network are other issues that are addressed by these.
SAVE YOUR HIGHER GRADE WITH ACQUIRING DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT HELP & QUALITY HOMEWORK WRITING SERVICES OF EXPERTSMINDS.COM!
Project Requirements
Delay
Analysis of these systems-how they work and interoperate-is secured in detail later in this book. System and framework unpredictability is nonlinear. System advancement must consider contending and frequently clashing necessities. Also, numerous gatherings with varying thoughts and wants (e.g., clients, corporate administration, organize staff) impact the system structure. The system is either structured by board of trustees or through a precise methodology that the gatherings can concede to. Systems have developed to fuse increasingly refined abilities. Early (original) systems concentrated on supporting essential availability between gadgets and on the best way proportional systems to help developing quantities of clients (e.g., dividing systems utilizing extensions or switches). Second-age systems concentrated on interoperability to extend the degree and size of systems to permit associations among numerous unique systems. We are presently at the phase in organize advancement where administration conveyance is essential to the achievement of clients and their applications. This stage can be viewed as the third era of systems administration. Delineates the different ages of systems administration and their connections. We are starting to see ventures toward cutting edge capacities, for example, simple basic leadership inside the system. It might be normal that parts of the system will advance to end up self-configurable and reasonable, particularly for those systems that must be arranged or regulated by end clients (e.g., remote workers, clients of versatility/convenientce administrations). Without a doubt, this will turn into vital as the multifaceted nature and execution of systems increment and as administrations offered by systems become increasingly refined. Matrix systems are a reasonable advance in this heading. Clients, applications, and gadgets are likewise developing progressively advanced capacities. A case of this is the dynamic among progression and assorted variety that can be found in the present Internet. As application and gadget traffic streams develop to fuse data in regards to quality, execution, and cost (e.g., constant
Throughput and performance
Execution is the course of action of levels for point of confinement, deferment, and RMA in a framework. It is commonly charming to streamline these measurements, either for all (customer, application, and device) traffic streams in the framework, or for in any event one loads of traffic streams, in light of social affairs of customers, applications, and also devices. In assistance of execution in the framework, an execution building is the arrangement of execution frameworks to configuration, work, administer, game plan, and record for resources in the framework that help traffic streams. The execution configuration shows where these segments are associated inside the framework, and the plans of internal and outside associations among this and other part structures. In this area we get some answers concerning framework resources and about segments to control additionally, administer them. A critical bit of structure up this plan is choosing the execution targets for your framework.
DO YOU WANT TO EXCEL IN DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT? HIRE TRUSTED TUTORS FROM EXPERTSMINDS AND ACHIEVE SUCCESS!
Website I - 89.9 TheLight | Positive Radio
Website II - ABC iview
Part 1 - The first part of the report should be about general statistics of all four captures using Wireshark that must include: 1. Start time of capture, 2. Total number of captured packets for each protocol, 3. Total Number of lost packets and 4. IP addresses of the client and server.
Answer 1 -
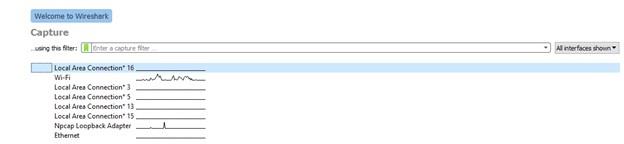
Start time of capture
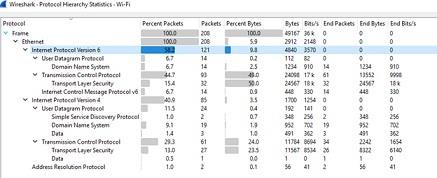
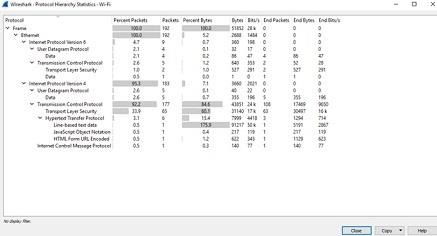
Captured packets for different protocols
Two kinds of collaborations are dominating inside this segment engineering: exchange offs among tending to and sending systems, and exchange offs inside tending to or inside sending. Tending to and sending systems impact the decision of steering conventions and where they are connected. They additionally structure an tending to chain of command whereupon the directing progression is overlaid.
Answer 2 - Start time of capture
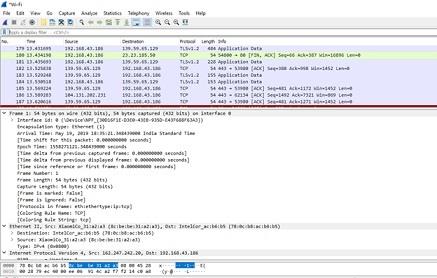
From the above figure it can be seen that the start capture time is 18:35:21 and date is may 19 2019
Captured packets for different protocols
Part 2: The second part of the report must include screen shots of packet capture, screenshots of different statistics from Wireshark and complete analysis of those screenshots for both websites for all two networks. Only screenshots of the graphs or other statistics will not get any marks as those must be analysed in detail to discuss the quality of service for a particular application. The students are required to analyse the network performance for the assigned websites considering following aspects: 1. Throughput, 2. Round Trip Time and 3. Packet Loss.
EXPERTSMINDS.COM ACCEPTS INSTANT AND SHORT DEADLINES ORDER FOR DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT - ORDER TODAY FOR EXCELLENCE!
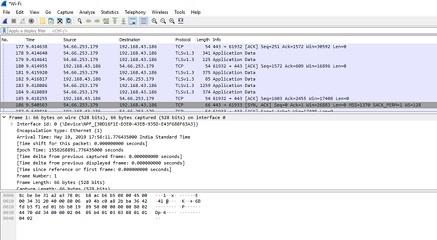
Answer 1 - IP addresses of the client and server
Communications between tending to/directing and arrange the executives. Tending to/steering can be utilized to design limits for system the executives. For instance, self-governing framework (AS) limits show where one administration space closes and another starts. Communications between tending to/directing and execution. Execution can be firmly combined with tending to/directing through components, for example, MPLS, Differentiated and Integrated Services, and RSVP. Be that as it may, while directing convention straightforwardness is a high need, execution might be decoupled from tending to/ directing. Execution can likewise be combined with tending to/steering through the utilization of IPv6, which gives data handle that can be utilized by execution systems. Associations between tending to/directing and security. Security systems are regularly meddling as they capture, examine, and control arrange get to what's more, traffic. Thusly, they can affect the directing conduct of the system. Similarly as security borders or zones bound execution (from Chapter 8), they can likewise bound steering. System address interpretation (NAT) can be utilized to upgrade security just as give private tending to space to a system. By framing a limit between private and open location spaces, with interpretation of addresses between these spaces, outside access to the system can be progressively controlled. The IP address of the source is the client that connects its host device to the server and sends or receives data from the server.
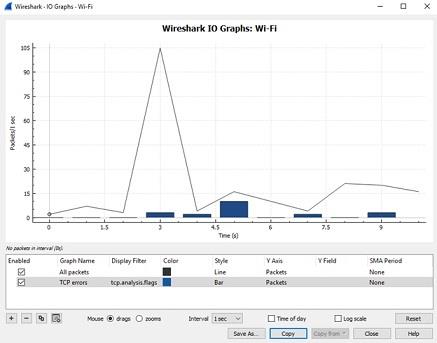
The figure above shows the packet being sent and received in given time , the graph shows the peak packet flow is during 3 seconds .
IP addresses of the client and server
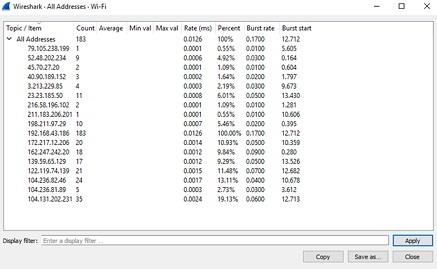
The server is the destination in this case , as it can be seen from the figure below the source IP address is the private address which cant be forwarded or advertised in the internet.where as the destination address is public IP address which can be used in global internet as it is unique and don't conflict with any other IP address in the internet. The network address translator is used for the conversion and getting the destination of the LAN IP if it is using private IP address.
As it can be seen, the
Client IP is 192.168.43.186
Server IP is 54.66.253.179
Packet Loss
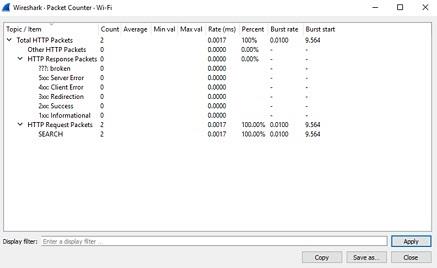
As it can be seen there is no packet loss, as the HTTP broken packets are 0%.
NEVER LOSE YOUR CHANCE TO EXCEL IN DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT - HIRE BEST QUALITY TUTOR FOR ASSIGNMENT HELP!
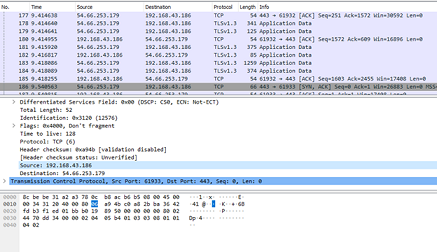
Answer 2 - IP addresses of the client and server
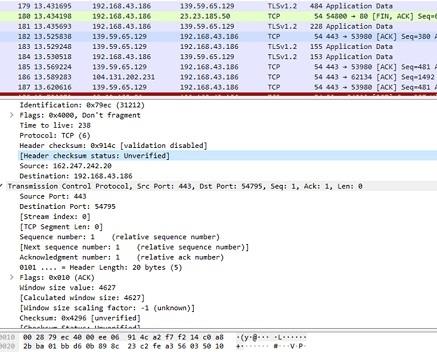
TCP shows the source and destination IP address.
Packet Loss
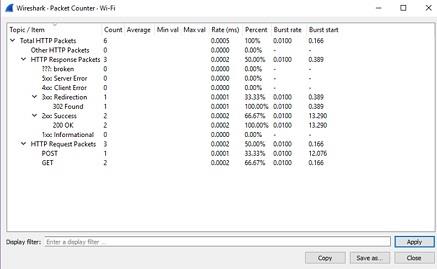
Thus the lost packet is 0%.
Part 3: The third part of the report is about comparing the collected Wireshark statistics of the two different networked applications on two different networks. The throughput graphs and TCP retransmission statistics for web page transfer and live streaming (provided in part 2) need to be compared with each other and for all two networks. The differences of the performance to be identified and reasons must be provided for such differences.
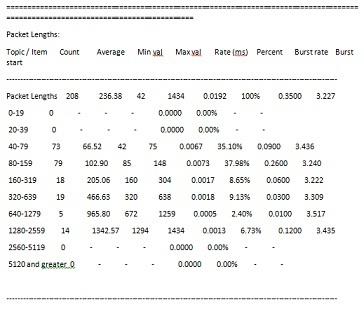
Answer 1 - Throughput of the network
This methodology is like an ensured administration. There is an exchange off between these two ways to deal with asset assignment in a organize. Despite the fact that a best-exertion arrange enables access to the same number of traffic streams as conceivable, execution corruption over the majority of the traffic streams can happen. Affirmation control jelly assets for traffic streams that have just been dispensed assets yet will reject extra traffic streams when assets are depleted.
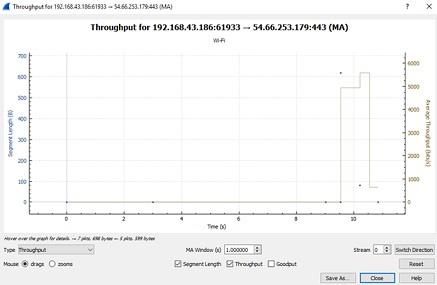
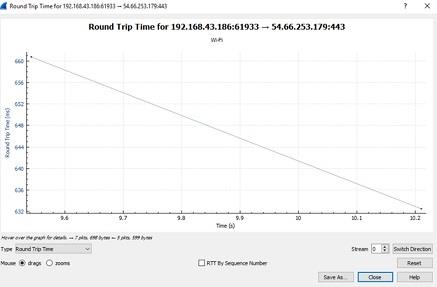
Round Trip Time
We talk about this in progressively critical detail in the segment on framework the administrators building Intuitive mass applications, incomprehensibly, are those for which getting ready at the contraption or application section is the mind-boggling deferral. This is basic to see, as the framework defer essential by that application ends up being less basic, since it is starting at now darkened by application just as contraption delays.
Answer 2 - Throughput of the network
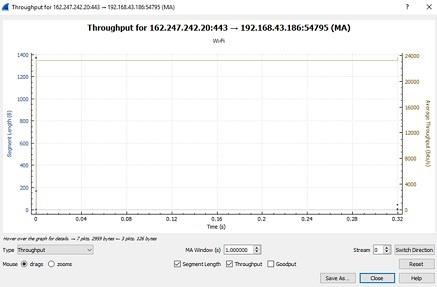
Thus throughput is constant.
ORDER NEW DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT & GET 100% ORIGINAL SOLUTION AND QUALITY WRITTEN CONTENTS IN WELL FORMATS AND PROPER REFERENCING.
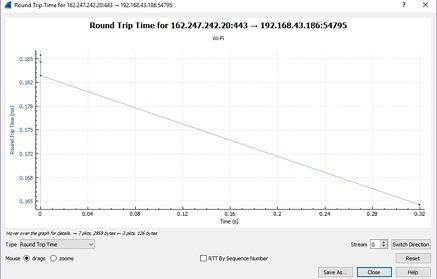
Round Trip Time
Comparison with Wireshark and NMAP
Measurement of multifaceted design:
Wireshark:
The graphics based sniffing tool that is used for the data traffic analysis, it shows the TCP/IP, HTTP and source and destination IP being used for connection. The LAN connection setting and examination is can be seen in this tool. The input output throughput and delay round trip time is also analyzed in this sniffing tool. Thus tool is mainly used in to identify the external attackers or unauthorized access to the network.
NMAP:
NMAP is a CLI based sniffing tool which is free of cost.
Included features:
Wireshark
- cross platform like UNIX and Windows.
- live capture of data.
- TCPdump / WIndump.
- Packets are imported from the group data from the internet source.
- Display packs with clear show information.
- Save pack data got.
- Export a couple or all groups in different catch record positions.
- Filter packages on various criteria.
- Search for groups on various criteria.
- Colorize group show subject to channels.
- Create various estimations.
GET GUARANTEED SATISFACTION OR MONEY BACK UNDER DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT HELP SERVICES OF EXPERTSMINDS.COM - ORDER TODAY NEW COPY OF THIS ASSIGNMENT!
NMAP: The NMAP is a sniffing tool which examines the traffic flow of the internet with the device , this sniffing tool is used for connection analysis , synchronization , ping , UDP connection analysis, this a cross platform and command line interface .
Advantages: both are free of cost, works in cross platform, easy to use, detailed information about the packets, vendors can be multiple and the there is no interference that is disturbed by this to network.
Disadvantages: information can only be received but not sent , and the unauthorized attackers can use this to hack the network.
Summary: In this project the Wireshark sniffing tool is used to get the required information of the two different websites and analyze them in details. The two different free sniffing tools are examined and the advantages and disadvantages are reported as per research on these. The Wireshark and NMAP are cross platform and free of cost tools that can get the detail information of the data flow from device and the internet. The analysis of internet gateway and the data flow information give better understanding about the internet packet loss and any authorized access, it increases the reliability and sustainability of the network design.
DO WANT TO HIRE TUTOR FOR ORIGINAL DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT SOLUTION? AVAIL QUALITY DISTRIBUTED NETWORK CONDITIONS ASSIGNMENT WRITING SERVICE AT BEST RATES!
Acquire our Melbourne Institute of Technology, Australia Assignment Help services for major related courses and academic units such as:-
- MN501 Network Management in Organisations Assignment Help
- MN502 Overview of Network Security Assignment Help
- MN503 Overview of Internetworking Assignment Help
- MN506 System Management Assignment Help
- MN604 IT Security Management Assignment Help
- MN507 Overview of Software Engineering Assignment Help
- MN611 System Architecture Assignment Help
- MN612 Enterprise Architecture Assignment Help
- MN610 Virtual Private Networks Assignment Help
- MN622 Software Defined Networking Assignment Help
- ME605 Cloud Engineering Assignment Help
- MN603 Wireless Networks and Security Assignment Help
- MN623 Cyber Security and Analytics Assignment Help
- MN691 Research Methods and Project Design Assignment Help
- MN692 Capstone Project Assignment Help
- MN621 Advanced Network Design Assignment Help
- MN624 Digital Forensics Assignment Help