GET ASSURED A++ GRADE IN EACH NETWORK INFRASTRUCTURE ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!
HS1011 Data Communication & Networks Assignment - Holmes Institute, Australia
Purpose (with ULO) - The purpose of this assignment is to exercise and develop skills required to analyse and design networks to address the need of clients. Students will be able to:
1. Discuss the need of electronic data communication and networking to achieve business goals.
2. Explain and apply various networking and data communication technologies in the context of a specific business need.
3. Evaluate and assess hardware and software requirements of a data communication and networking infrastructure.
4. Define, prioritise and evaluate the requirement of the business to provide data communication and networking requirements.
5. Understand, evaluate and describe importance of network and data communication for a business operation and assess and suggest troubleshooting suggestions for a data communication and networking problem.
6. Communicate using an effective oral and written communication, act in a professional conduct, be an effective team member or team leader and be creative and innovative.
7. Understand the ICT profession and professional expectations in data communication and networking.
Purpose of this assignment - In this assignment, you are required to identify the resources needed to design and setup a network infrastructure for the new campus for Holmes Institute in Melbourne. You also deal with problem solving which includes the identification and determining the specification of the problem, strategies for its solution. You have to critically evaluate the solution provided through the reflective report writing. Then present and justify an appropriate networking solution to meet specified requirements.
NO PLAGIARISM POLICY - ORDER NEW NETWORK INFRASTRUCTURE ASSIGNMENT & GET WELL WRITTEN SOLUTIONS DOCUMENTS WITH FREE TURNTIN REPORT!
Requirements - Assume that the network described Assignment 1 is expanded to include two new schools and an IT centre. A new IT centre has just opened up. It aims to provide student labs, provide computers for its education and administrative staff and set up a web server. Holmes has just purchased one Metro Ethernet connection from HLNET providing 10Mbps for upload and download. It has also purchased the 202.175.177.128/26 network from HLNET.
Solution - DATA COMMUNICATION & NETWORKS
Part 1: Introduction
The term "Data Communication" mainly refers to transferring digital kinds of information among different devices like computers or laptops etc. Data network is the process of transferring data between the mediums. Data communication can be done in the wireless medium and wired medium as well. In the architecture of computer networks, the information is conveyed in kinds of packets. The equipment that receives and transfers data is called as nodes. Various types of data networks are there like - one is "Local Area Network" in small LAN, which mainly used for small areas. LAN can be installed in a small building or something that. Another type is "Wireless Area Network" in short WAN which covers a wide range of areas. This WAN is used to connect LANs and other various types of networks that can help the computers to interact with the other computers in different regions. The 3rd kind of network is "Metropolitan Area Network" in a short MAN which works as connecting the computer resources and users that is a little bit larger than LAN but not larger than WAN. There are lots of different components of Networks that are there like "Servers which hold programs, files, and operating systems. Clients can access the data which is stored in the server network. Transmission media by which the client can access the data in the form of files from the server network, which can be wireless as well as the wired medium. Others are like Switch, Network Interface Card, Hub and Network Operating System". Network Architecture can be distinguished like "client to server, peer to peer" etc.
Analysis
1. The term" Web Hosting" is a giant computer where people stock different types of websites. It gives the technology and space to the server to be penetrated on the connecting of the Internet. The data centres and web hosting are the same types, and they used to work together. Web hosting is of different types like "shared hosting" when one website distributes the space of servers with various websites. "Dedicated Hosting" where the website distributed with only one server. "VPS Hosting" where one website is connected with multiple serves [1].
2. A "File Server" is a giant computer that is connected to a network that gives a proper location for accessing the shared disk and the files can be of different types like sound, image, video, etc. By the use of this "File Transfer Server" the students of "Holmes Institute in Melbourne" can access the different types of data from home.
3. A "DNS" server which I a computer server which consists of different types of "public IP addresses" and the "hostname" as well. It used to work to translate, resolve those IP addresses when it needed to. DNS mainly works for communicating with each other with the help of different IP addresses with individual protocols. The students of "Holmes Institute in Melbourne" can communicate with the server with different hostnames and IP addresses [2].
4. There are three rooms in "Holmes Institute in Melbourne" to create computer labs, and each one of the rooms is having different numbers of computers and connecting all the computer networks need to access the internet, attached devices and network printers and other systems on that network. The computer can be connected by the use of "Ethernet cables which is Wired Network" or the "Wi-Fi wireless network" [Referred to appendix 1].
ENDLESS SUPPORT IN NETWORK INFRASTRUCTURE ASSIGNMENTS WRITING SERVICES - YOU GET REVISED OR MODIFIED WORK TILL YOU ARE SATISFIED WITH OUR NETWORK INFRASTRUCTURE ASSIGNMENT HELP SERVICES!
5. "Holmes Institute in Melbourne" also needs seven numbers of computers which is needed for the class tutor for each of the classes. Internet connection of these seven computers will provide from the wireless adapter which will be installed on those computers. Instead of a Wireless adapter, those computers can also use cable connection or modem's internet. The modems must be connected with the routers to get the connectivity of the internet [3].
6. "System Administration" indicates the management of software and hardware systems. System administration is used to do with the help of an IT expert for all institutions of organization. The jobs of a "system administrator" are to maintain the systems and monitoring the condition of the system. Here also in "Holmes Institute in Melbourne" provides two computers to the system administrator and their job is to maintain the system as well as to give any kinds of internet services to the computer which will be used by the student and the teachers as well. In order to have some difficulty in the systems, the system administrator will take care of that.
7. "Holmes Institute in Melbourne" decided to provide five more personal computers to the system administration and 3 for the tutors but they also decide that those computers will not have any internet connection, but those computers can still access file servers and the web. It can be done by the use of "Local Area Network". All those eight computers must be connected with the server and can interact with the help of "wireless point to point connectivity". The web application can also be assessed by the help of the internal IP address of the central server [4].
8. "Holmes Institute in Melbourne" wants to make available for their students to access the web file and servers without having internet connection so that when the students are not having any kind of internet connectivity, then they can also access those files. It can be done with the "Wired Area Network (WAN)". WAN can be connected with a DSL modem or cable, and it can clog into the existing network that is in their place. LAN is also helpful to access the web files and servers but only when the student is in the institute premises as LAN is "Local Area Network" and it can be in only small areas. When the students are in the home at that time, they can use the "Wide Area Network" to access the web servers and files [5].
9. "Virtual Private Network" in short VPN permits to make secure connectivity with other networks by the internet connection. VPNs are used in organizations or institutions for years, just focusing on security. A firewall is used to secure the data from a computer, whereas VPN is used to secure the data or information on the web. VPNs usually use "advanced encryption protocols and secure tunnelling techniques" to protect all the online transferring of data. "Holmes Institute in Melbourne" decides to use VPN technology so that the students or tutors can access data or files from anywhere without having any interruptions. Integrity checks are the method that can make sure that is there any data is lost or not and that connectivity is not hijacked. VPNs mainly work over proxies [6].
10.
HELPING STUDENTS TO WRITE QUALITY NETWORK INFRASTRUCTURE ASSIGNMENT AT LOW COST!
11. This type of testing is called "Functional Testing". This test can be done for the use of functional operation. Here there are various paths of functions and paths by which network can be designed.
12. There are different types of methods that can make better security to a network, and one of the methods is-
"Segment and Segregate Networks and Functions"- the architects who are responsible for giving a better secure network, must take care of the whole layout of infrastructure, as well as "Segmentation and Segregation". The correct segmentation of the network is perceptual security mechanisms that can block a hacker from inseminate moving around a private network. If a network is poorly segmented, then the hacker can easily access that network and gain intellectual property and sensitive information. A protected "segregated network" can accommodate a venomous activity, low down the impact of the hackers in the activity that they achieved perched somewhere into the network [7].
13. "The International Organization for Standardization (ISO)" models of management of network states about the different types of functions areas are there in according to the network management. Those aspects are as below-
"Fault Management" - "Detect, Isolate, Notify and correct" faults detects in the management of the network.
"Configuration Management" - In this management, different aspects are configured like "file management, inventory management, and software management".
"Security Management" - Given access to "network devices and corporate resources" to commissioned individuals.
"Performance Management" - Counseling and counter various methods of performance so as to maintain the overall performance to a specific acceptance level [8].
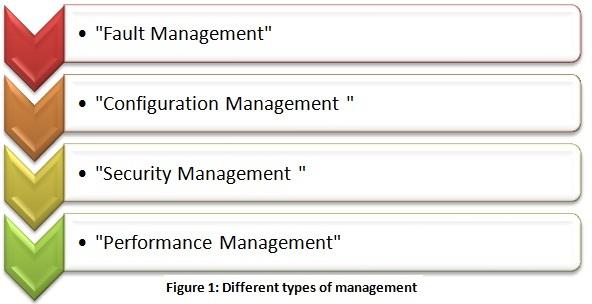
All these above aspects can make the network of "Holmes Institute in Melbourne" in a successful way.
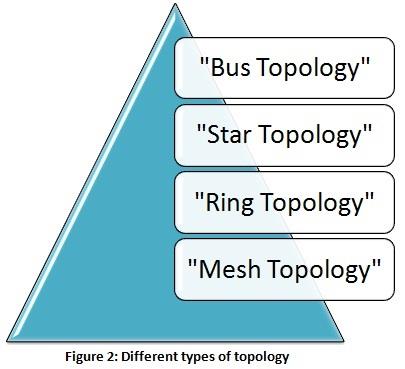
14. Different kinds of Topologies are as follows-
Bus Topology- Here every "network device and computer" are connected in one single table.

Ring Topology - Here, each computer is connected with their neighbour computers.

Star Topology - Here, all the systems are individually connected with the HUB.

Mesh Topology - Here, every system are is connected all together with each other.

GET READYMADE NETWORK INFRASTRUCTURE ASSIGNMENT SOLUTIONS - 100% PLAGIARISM FREE WORK DOCUMENT AT NOMINAL CHARGES!
15. Equipment needed to set up a network-
"Cables and connectors" - average cost $20
"Router" - $40-$260
"A wireless access Point" - $120
"Internet Connection" - $300
"Hardware Firewall" - $1000- $2000
Part 2 -
1. "Content Delivery Network" provider or operators face some challenges when service, retaining consumers and the competition and dynamic gets on the market of CDN. "Streaming video" in live or playout mode consists of the central part of the traffic of CDN. The cost is one of the main issues for the customers when they use video streaming in mobile devices and connectivity in many countries.
2. A. The reasons for congestion are -
- "Too many hosts in the broadcast domain."
- "Broadcast storms."
- "Low Bandwidth"
- "Adding Retransmitting Hubs"
- "Multicasting"
- "Outdated Hardware"
- "Bad configuration Management."
- "Rogue Adapter Broadcast"
- "Border Gateway Protocol"
- "Artificial Congestion"
B. Approaches of congestion control -
- "No explicit feedback from the network."
- "Congestion inferred from end system observed loss, delay."
- "Approach took by TCP."
- "Routers provide feedback to end systems."
- "Choke packet from router to sender."
- "Explicit rate sender should send at."
- "Single bit indicating congestion."
MOST RELIABLE AND TRUSTWORTHY NETWORK INFRASTRUCTURE ASSIGNMENT HELP & HOMEWORK WRITING SERVICES AT YOUR DOORSTEPS!
3. A. In "Software Defined Networking" control and data plane are disconnected by Open Flow or API but for "Conventional Network Design" those plans are mounted on that same plane, updated protocol for each service.
"SDN" is capable of block o prioritize particular packets, but "CDN" processes all the packets in a similar way.
"SDN" is simple to program as per the user and application needs and can be moderate immediate by the use of up-gradation of software, but "CDN" is hard to alternate the old programs with updated ideas and jobs as per the tables of packet-forwarding [9].
4. A. The difference between DASH and streaming protocol are as follows-
- "HLS is older and widely supported" whereas "DASH is newer, more efficient and has become a standard".
- One advantage of HLS is, it accommodates the bandwidth of the user, whereas DASH is an open-source that helps the "media content publisher community" to update and changes.
5. A. "Frame Relay" which is having a minimal amount of "Quality of Service (QoS) manageability" and that can be one of the reasons behind the replacement of MPLS. If an app works well on a Frame delay, then that apps will work better by the use of MPLS. That can be another reason for the replacement of MPLS.
6. A. "Data Center" can be likeable as a benefit whose job is to control a massive kind of data. It is conceptually made of application-based software. Data centres need capabilities to make sure that data services are working correctly and, many technologies are there which can be utilized to commit their goal. Data centres can become capable of running 24*7*365 without being interrupted by anything. Unplanned or planned downtime can do damage to the users of the business.
7. A. "Code Division Multiple Access" in short CDMA is basically a "digital cellular network standard" that used the technology of spread-spectrum which combines with the "analogue-to-digital conversion". This CDMA technology does not compress the bandwidth of digital frequencies or signals but distributes it through multiple channels of division. Therefore there are modified capabilities of data and voice communication and a better private and secure line. CDMA provides more capacity of airspace compared with the "Time-division Multiple Access (TDMA)" based system globally for "Mobile Communication Standard (GSM)" [10].
B. In the area of telecommunication the term "Long-Term Evolution (LTE)" is a division for "Wireless Broadband Communication" for data terminals and mobile devices and that depends on GSM technologies. It is a 4G "wireless communication standard" created by the "3rd Generation Partnership Project (3GPP) that structured in such a way so that it can provide a speed of 10x of 3G networks for equipment like tablets, Smartphones, notebooks, etc. "4G technologies" are designed to give IP-based data, voice and multimedia streaming of at 100 Mbit/second speed and it expands up to 1 Gbit/second.
SAVE DISTINCTION MARKS IN EACH NETWORK INFRASTRUCTURE ASSIGNMENT WHICH IS WRITTEN BY OUR PROFESSIONAL WRITER!
C. "802.11" is an emerging family of characteristics for "wireless local area networks (WLAN)" created by a committee of the "Institute of Electrical and Electronics Engineering". 802.11 characteristics utilize the "Ethernet protocol and Carrier Sense Multiple Access (CSMA)" with "Collision Avoidance (CA)" for sharing of the path. The primary modulation utilized in "802.11" was "Phase Shift Keying (PSK)".
8. A. An "Authentication Protocols" states a claim of the identity of the network. "Good security design," thought that a network snooper might detect all packets which need to convey among the authentication server and the client so that the protocol must remain secure. There are various types of authentication protocols like - "Password Authentication Protocol (PAP), Shiva Password Authentication Protocol (SPAP), Challenge Handshake Authentication Protocol (CHAP), and Time Based One-Time Password (TOPT)" etc.
B. "Pretty Good Privacy" is a scheme used to encrypt and decrypt the files which are digital in nature and interact through the help of internet connection. It was initially released with a "BassOmatic symmetric key algorithm", but later on it gets replaced by the "International Data Encryption Algorithm (IDEA)" to avoid the individual flows of BassOmatic. PGP is a freely available package of software for the security of email. It gives permission over the utilization of digital signature.
9. A. "Voice over Internet Protocol (VoIP)" is a technique that permits to generate "voice calls" with the help of internet connectivity of broadband rather than an analogue phone line. It sometimes also helps to make calls to other people using a similar service, but others might permit to make calls to anybody who is having a telephone number as well as long-distance, local, international and mobile numbers. There is some number of VoIP which only permits to some kinds of particular VoIP phones or computers. "VoIP service" transfers the sounds into the "digital signal" and that moves over the internet connection.
B. "The Real-Time Transport Protocol (RTP)" is an "Internet protocol standard" that articulates a sequence for managing the program to the transmission of "real-time multimedia data" over multicast or uncast services of the network. "RTP" was structured by the "IETF's Audio-Video Transport Working Group" to provide the conference of video graphics with the participants of geographically dispersed.
"Session Initiation Protocol (SIP)" is a protocol of signalling utilized for modifying, maintaining, and terminations the sessions of real-time that combines voice, video, texting and other types of communication services and application among the two or more IP networks.
C. "Quality of service (QoS)" indicates any technology which controls the traffic of data and lows down the latency, packet loss and jitter over the network. QoS manages and controls the resources of the network by providing priorities for particular kinds of data over the network.
Conclusion:
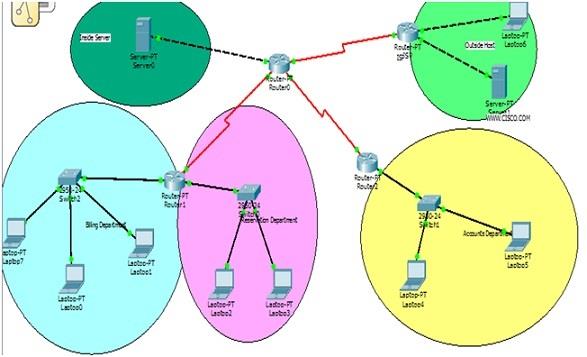
In this research of "Data communication of Network," different types of network strategies and various kinds of network architecture is elaborated and designed by the use of network diagrams. This research
Discussed different types of terms and different kinds of network topologies have discussed, and their diagram is also designed about how the security of the network can make secure, this thing also discussed in the above research work. The logical diagram is also designed by the use of Packet Tracer in the above research work.
HIRE PROFESSIONAL WRITER FROM EXPERTSMINDS.COM AND GET BEST QUALITY NETWORK INFRASTRUCTURE ASSIGNMENT HELP AND HOMEWORK WRITING SERVICES!
We offer reliable and genuine Holmes Institute, Australia Assignment Help service for related course and units, such as:-
- HS2011 Systems Analysis and Design Assignment Help
- HS2021 Database Design and Use Assignment Help
- HS2031 Human-Computer Interaction Assignment Help
- HS2041 Enterprise Systems Assignment Help
- HC2051 Web Applications Development Assignment Help
- HS2061 Information Systems Project Management Assignment Help
- HS3011 Information Security Assignment Help
- HS3021 Strategic Information Systems Management Assignment Help
- HC3152 E-Business Applications Assignment Help