Steganography In Biometric Data
Research Proposal On State Of Steganography Application In Biometric Systems
ARE YOU LOOKING FOR RELIABLE STEGANOGRAPHY IN BIOMETRIC DATA ASSIGNMENT HELP SERVICES? EXPERTSMINDS.COM IS RIGHT CHOICE AS YOUR STUDY PARTNER!
Abstract: Biometric characteristics of individuals has been utilized from a very long time too advanced authentication and verification technology that is not dependent on password protection and therefore this has been a topic of discussion for many researchers. In this research proposal, a detailed literature review on integration of steganography and biometric have been provided which aims to fulfill the objectives of the research. The research has also stated a problem that can be solved by use of appropriate strategies and existing literature on steganography and biometric.
The research aims to identify the current state of application of steganography and the field it has been utilized. However, existing literature have failed to identify the integration of biometric and steganography methods into real-world setting.
In the light of the literature identified, the future research should focus on identifying better opportunities of steganography in securing the biometric systems. A timeline has also been provided to systematically approach with the research.
Introduction: As opined by Somanchi and Telang (2016), in today's modern era, security has been a major concern because of the day by day increase of frauds. The use of biometric systems security applications helps in assessing the control in many fields. According to Kaiwartya, et. al. (2017), Biometrics deal with the physical and behavioral characteristics of an individual for recognition and authentication. In order to recognize and authenticate the identity of an individual, there are existing biometric systems which utilizes a fingerprint, Iris, palm print, facial and voice identification, finger knuckle print, and hand geometry. As opined by He and Wang (2015), the biometric concept provides several advantages over passwords, pin systems and token methods which cannot be lost easily. The use of biometric systems have evolved rapidly and are used in almost all areas health services, banking and government agencies, private companies, airports, border security and law enforcement. Gofman, et. al. (2016) have stated that in recent years, companies like Apple and Samsung have utilized biometric systems in their mobile devices that can be unlocked with user's fingerprint or face recognition. The reason behind the popularity of these biometric systems is that they have the ability to distinguish between the authorized user and an unauthorized user. Currently fingerprint and face recognition are considered as most commonly used biometric systems as they are convenient to use and are less expensive options to maintain security in comparison to other systems. However, as opined by Gupta, Agrawal and Yamaguchi (2016), the concerns of security and confidentiality has given rise to development of many such applications. But even biometric systems are susceptible to various threats. This is where the role of Steganography technique comes in light that has the potential to make biometric systems more secure. As stated by Singh and Kant (2017), Steganography can be described as a data hiding technique that aims at protection of private information and securing information transmission. In Steganography the data is hidden in such a manner that cannot be detected by the human eye. Steganography has been in existence from a very long time and its applications for biometric data has proved to be sufficing the requirements of security and confidentiality.
As suggested in the research conducted by Setiya and Kant (2016) to improve the safety and security of the biometric systems by use of Steganography techniques and it also has provided opportunity for hidden information but the only issue can be due to breaching of the systems. The existing Steganography applications for biometric data have benefited many fields but there is a room for improvement. As suggested by McAteer (2019), a successful Steganography algorithm depends on the fulfillment of requirement such as the invisibility of the technique, covert communication, and use of statistical steganalysis technique, security against image manipulation, identification of unsuspicious files, and identification of different file formats. As highlighted by Hashim, et. al. (2018), LSB is one of the most common techniques of steganography which hides the secret message and undetectable by the human eye. There have been message hiding techniques developed by researchers but the scope of these research continue to be identified to maximize the future opportunities. The proposed opportunities will be able to safeguard and build robust biometric systems by use of steganography. The aim of the research is to identify the state of the art of existing steganography applications for biometric data and if there is a future scope for improvement in the existing systems.
Question 1: Problem statement
a. Describe the problem that your research will address in as much detail as possible.
Answer: Description of the problem: The integration of biometrics and steganography methods provides in-depth security of the biometric systems but the efforts have failed to transition from several research into real-world applications.
b. Specify and describe your main objectives and sub-objectives.
Answer: Objectives of the research: The objectives of the research are:
• To identify the existing Steganography applications for biometric data
• To focus on the issues with secure Steganography
• To analyze the future potential of integration of biometrics and Steganography
c. Define the scope and limitations of the research.
d. State any assumptions that you are aware of.
Answer: Scope and Limitations of the research: The scope of the research will be to identify the potential application of biometrics and Steganography in the real world. Although there have been few research conducted on integration of biometrics and Steganography, there is a further scope of improving the biometric systems from threats such as cybercrime, loss of identification data of individuals and loss of confidential data.
Every research conducted carries potential risks attached to it which requires to be resolved in order to successfully continue with the research. The challenges associated might arise due to conducting systematic literature review of the research previously conducted integration of biometrics and Steganography. Since the research were carried out by different people, there may be risks from merging previous findings. Further, it might be difficult to analyze the quality of the studies conducted in past with regards to strengthening of biometric by application of Steganography. There can be lack of information on the proposed topic which might consume some time in conducting further research.
GETTING STUCK WITH SIMILAR BIOMETRIC ASSIGNMENT? ENROL WITH EXPERTSMINDS'S STEGANOGRAPHY IN BIOMETRIC DATA ASSIGNMENT HELP SERVICES AND GET DISTRESSED WITH YOUR ASSIGNMENT WORRIES!
Question 2: Literature survey
a. Overview of research that has been conducted on the problem that you are investigating.
b. Want to show how your research relates to and differs from existing research.
c. Identify the main players in the field.
Answer: Overview of biometric systems: As opined by Bhagabati and Sarma (2016), Biometric authentication become one of the most reliable and popular access control technique that has helped secure systems of various fields. The secure storage of biometric features in any given digital database for subsequent biometric template matching will facilitate requirement of any biometric related application. As suggested byRani and Euphrasia (2016), a secure encryption will determine the safety and confidentiality of the storage of such sensitive data. Steganography can be useful to improve the security of biometric systems during the encrypted data transmission. This will ensure authentication of individuals by their fingerprint, face recognition and other biometric systems. As suggested by research conducted, there lies a threat with exploitation of personal information of individuals by cyber criminals either to steal confidential information, conduct identity theft or conduct monetary theft. As suggested by Zahrouni, et. al. (2017), Biometric data can be stolen by cybercriminal to conduct substitution attacks in order to procure personal information of an individual such as their security numbers, debit and credit card numbers, identity proofs and other personal information which can potentially be used against them either to threaten them or cause potential harm. Therefore it is important to consider all the barriers that can potentially be a threat for an individual's sensitive data. As stated by McAteer, et. al. (2019) in their study on the Defense in-depth security model which provides security to the information by use of multiple defensive layers. These defensive layers are built with different strategies that will help to provide security to the information even when any one of the layer is breached, it will not affect the overall security of the system. The integration of biometrics with steganography provides a better opportunity in the future by analyzing the current status of the existing research and whether steganography will be helpful strength and layers of security.
As identified by Wright (2019), Biometrics is widely used in almost all areas such as in healthcare sector, retail sector, safety of information of organizations and government departments. The most commonly used in biometric systems use of fingerprint scanning to authenticate the identity of an individual which is considered to be way more better than use of complex passwords. Sarhan, Alhassan and Elmougy (2017), each of the methods of biometric systems such as the fingerprint identification system, Iris and retina detail, facial recognition, hand geometry, odor recognition, voice recognition and signature have evolved in the recent times to provide better security and safety of authentication processes. As suggested by Ngo, Teoh and Hu (2015), there are several parameters for the use of biometric technology which can depend on how easily they can be used, what are the sources of error, how users are accepting the system, how accurate the biometric scans are, the stability of the biometric systems and the costs of the level of technology used in biometric systems.
Advantages of biometric system: There have been several researches conducted to analyze the perceived advantages as well as the disadvantages of biometric methods that provides a safe and secure system of storing information.
Fingerprint: Many organizations use fingerprint as a safe method of storing identification information of individuals. This is highly popular because of its ease of use, and it is inexpensive. Fingerprint scanning is not available on smartphones and other devices and there is stability in the characteristics over time.Although there are minor disadvantages such as threat from use of prosthetic fingers to steal information, damage from wear and tear on ridge patterns.
Facerecognition: This is again has become a popular method of application of individuals. Since it is easy to use and provides no direct contact with the subject along with low costs, it is highly in demand. Companies like Apple and Samsung have utilized face recognition in their smartphones.
The disadvantages can be varying facial expressions and light conditions.
Iris and retina method: Iris and retina identification have been popular in the recent times and utilized in smartphones and other gadgets which can be easily used and provides maximum security. But on the contrary use of iris identification can be an expensive option and requires the subject to be in close proximity of the device the system is used. The retina identification cannot be easily used especially when people use contact lenses.
GET ASSURED A++ GRADE IN EACH STEGANOGRAPHY IN BIOMETRIC DATA ASSIGNMENT ORDER - ORDER FOR ORIGINALLY WRITTEN SOLUTIONS!
Use of steganography in biometrics: According to, steganography refers to a process that involves hiding of information or a message in an appropriate career. As suggested by Omolara, et. al. (2018), Steganography has been in existence from a prolonged period of time which allows users to hide large amount of information either in image,audio or text files. According to Singh and Siddiqui (2018), research conducted, steganography and Cryptography has been closely related since they both are helpful in hiding information.Steganalysis is considered as art of detecting steganography. It is a process that helps to identify the existence of hidden message in the media and recover if it is available.There can be several reasons to hide information and data ultimately the objective of hiding these data is to protect them from unauthorized people so that they are unaware of the message it contains. Steganography has been very useful to the business world in hiding information and the prospected plans of companies. Companies of utilized location of steganography operations for sending out trade secrets without anyone knowing. Steganography has also been prevalent for terrorist activities. This sounds nefarious but it has helped terrorists to communicate secretly and co-ordinate their attacks. As stated by Yu(2017), Watermark is one of the newest applications of steganography which copyrights the information. Some researchers have identified that steganography has been used for decoding hidden messages that are stored in CDs and DVDs.In one research it has been identified that which increases the security of biometric data exchange by use of steganography. Another research has identified the use of fingerprint and face recognition as an important biometric system. There have been researches that have identified several attacks on host images and that is why human visual systems have been utilized.
Very few research papers have addressed on the use of steganography in biometric systems. There are lack of research papers in the field of E-health and cyber security. Although there are several uses of steganography, there have been number of research papers only on fingerprint and face recognition. As stated in the article by McAteer (2019), companies like Akoura Biometrics Inc. have used steganography in their systems and became the first company to integrate steganography and biometrics. The company utilized the application of steganography to overcome the issues of secure transmission of information in the financial and health sector. But there are certain biometric system manufacturers who have not utilized the use of steganography in their systems such as UniLink and NeoFace.The achievement of integrating biometrics with steganography can be done through embedding and encrypting biometric data into an individual's image to diversify verification of access control. It can also be achieved by covert transmission of data.In the research by Galterio, Shavit, and Hayajneh (2018), it has been highlighted that fingerprint and facial images are available easily for research purpose and this is the reason why fingerprint and face recognition scanners are comparatively cheaper than any other biometric device.
Skin tone detection is a newer entry in the biometric methods which is useful for encrypting data using steganography. This can be used for face and gesture recognition, image editing, controlling the browsing behavior of users and video surveillance. But research shows the non-utilization of steganography in these applications. Few researchers have proposed the use of steganography and biometrics in online voting system as well as online shopping sites. But all these proposals have not been yet applied in the real world. However, the use of cryptography to encrypt data has been useful for secure method for transmission of sensitive information of individuals. According to the research by Williams and Woodward (2015), hacking has been considered as a risk while transmission of data. The development of any technique in the future will consider security at first and therefore steganography in biometrics can be a viable future solution to solve the issues identified in this research.
Question 3: Methodology
a. Identify the methods that you plan to use to address your objectives.
b. Must tie back to your research objectives.
c. Should be clear that selected methods are appropriate (explain why alternative methods not proposed).
Answer: Research Approach: Research approach refers to the plants and procedures which consists of the steps associated with the collection of data, analysis and the findings of the research interpretation derived from it. The research reports can be categorized into collection of data and the approach of data analysis. The research approach will be focusing on the research problem identified and accordingly bring a value to the study conducted. This will help in validating the accuracy of the findings and this will also help in relate the literature to the research questions framed. The following research will be conducted by use of quantitative and qualitative secondary data which will help to develop rationale to the study. In this research proposal, the qualitative data will be procured by use of inductive approach of analysis and the quantitative data will utilize the deductive approach. The data collected will hold acceptable data collection methods that are authentic and help to derive the desired results.
Data Collection: The following research with involve information based on various applications of steganography especially in the field of biometrics. This will require to identify the collection of secondary qualitative and quantitative data. In this following research proposal, secondary qualitative and quantitative data refers to collection of existing information on integration of steganography and biometrics. The qualitative data will be collected from the existing research conducted on the topic.
The qualitative data will comprise of articles stating the integration of steganography and biometrics, scholarly journals, books and researches conducted on and biometrics utilized in different fields which can be identified by using specific keywords Steganography, Biometrics and steganalysis. The research will focus on identifying existing studies conducted to analyze the application of steganography in the field of biometrics and its future scope.
The quantitative data will be collected from Google scholar, and data related to distribution of steganography methods and its application, information related to companies who have applied the use of in their biometric systems. The data will also be derived from previous published researches on steganography. The proposed research will utilize analyzing the existing standard LSB algorithms, data extraction techniques and embedding techniques.
Data Analysis: The following research proposal will be a well-documented report on the state of the art of existing Steganography applications for biometric data and identify the scope of improvement. The findings from the secondary research will be analyzed in this section of the research proposal. The information collected from the previous research will be helpful in analyzing the secondary qualitative data. The findings will help to analyze the integration of steganography and biometrics in different areas of operation. The analysis of both qualitative and quantitative data will give rise to two potential applications of Steganography in biometrics. First, the data analyst will be helpful in proposing online voting systems and securing the information. This will utilize a combination of both LSB steganography and Cryptography into biometrics. Secondly, online shopping systems can be secured by use of a software that will electronically generate an internet shopping card that will hold customer information, their identification details, fingerprints and face recognition details, and their transaction details.
The data will also focus on acceptable level of embedding, implications of manipulating the source medium by use of steganography, and strengthening of steganography key exchange. The data will be identified keeping in mind its future application in the real world setting and how better opportunities can be framed for the integration of biometrics and steganography.
Planning
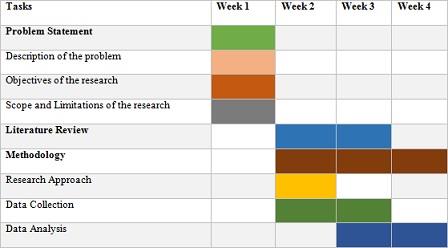
From the above time table prepared, research proposal will start with identifying the problem of the research which will help in framing the problem statement. This will be conducted in the first week of the research proposal. The next step will be to frame the objectives of the research. This will again be conducted in the first week of the research proposal. Along with that, the scope and limitations of the research will be identified in the first week of the research proposal. The literature review will be conducted in the second and third week of making the research proposal. The next step will be identify the appropriate methodology. This will include writing the research approach, and appropriate data collection methods. The data collection methods will involve the use of both quantitative and qualitative data which will be carried in the second and third week. The data analysis will be conducted in the third and fourth week. This planning process will help to systematically conduct the research.
24/7 AVAILABILITY OF TRUSTED STEGANOGRAPHY IN BIOMETRIC DATA ASSIGNMENT WRITERS! ORDER ASSIGNMENTS FOR BETTER RESULTS!