BN303 Wireless Networks and Security Assignment Help
Wireless network and security “Secured design of wireless LAN”
The purpose of the assignment is to design a secured wireless LAN. Students will be able to complete the following ULOs:
d. Apply wireless network security techniques in the context of ethical implications;
e. Design and implement secure enterprise wireless networks.
Do you want to hire tutor for original BN303 Wireless Networks and Security assignment solution? Avail Quality Assignment Writing Service at Best Rates!
Introduction
Security and protection of information is the real necessity for wired and remote system. In any case, there is have to concentrate on right gadgets with the goal that it can communicate just secure association with all. Switch and modem gadgets when associated in rehashing mode then it can communicate secure heading. Nonetheless, because of wide scope of prerequisite and college grounds is enormous there is need of big business class switch which can be utilized to set up top of the line wired and remote association.
Analyse
Hardware requirement
It is essential to break down equipment and programming necessities with the goal that it will be anything but difficult to associate the gadgets.
Systems administration gadget Cisco undertaking class switch
Repeater-it tends to be utilized to rehash the current system with the assistance of upheld gadgets.
Passage It can be utilized to communicate a similar remote system to more range and capacities.
Fiber optic link it tends to be utilized to set up LAN association with the goal that fast can be exchanged to the gadgets. At the point when gadgets are associated through LAN availability then they can even share records and organizers in disconnected mode as well. On the off chance that any issue happens in online network then clients can shared information inside with the assistance of these LAN associations, (Mitchell, "How Might You Secure a Wi-Fi Network with WPA2?")
DSL and ADSL connection
It is the web input which is required to be given in systems administration gadgets with the goal that solitary wired or remote web association can be communicated from the systems administration gadgets. Mounting gadget it very well may be utilized to help mounting of the systems administration gadgets with the assistance of stand and different highlights that way. Stand and different things are extremely important to hand the gadgets on divider with the goal that further issue can be settled.
Programming prerequisites
Switch programming with the goal that it tends to be utilized for setup
WPA2 and WPA security system
Macintosh Address
IP table distribution
Design
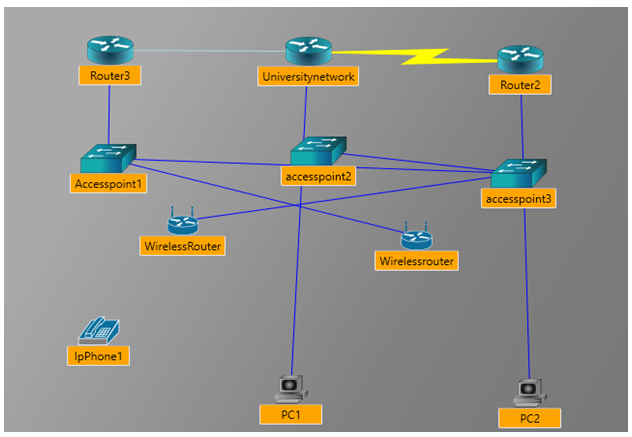
In the above system college arrange is associated with two different switches and further same system has been reached out with the assistance of passageway. Remote switch can be utilized to interface gadgets in any case, design of gadgets will be done to protect the system with remote instrument. Beyond what 3000 clients can be associated with the above system. When we utilize remote system is broadened then that can be utilized to associate with portability gadgets accessible in system.
There are a few variables to be considered while planning and conveying remote system. Anyway a large portion of the gadgets give common range to the gadgets they fabricate. In view of the sort of receiving wire utilized it give effectiveness of the sign and client can make choice dependent on this. Anyway dependent on the kind of receiving wire utilized in gadgets scopes of the systems administration gadgets can be chosen. In spite of the fact that there is have to consider all obstructions too on the grounds that like furnishings, roofs, impedance from hardware, electrical cables, and other electronic gear's accessible in the network.("Wireless security conventions: The contrast between WEP, WPA, WPA2") Transmission and gathering of the sign is likewise significant in light of the fact that when signal bob off the articles that can be issue in keeping up satisfactory sign quality. Another significant factor is that when gadgets do not bolster most extreme speed and progressively number of clients associated at once then that is likewise an issue for compelling pace. Establishment and arrangement ought to be done dependent on the accomplishment of solidarity and receiving wire signal. At the point when there is top time in abundance and tweak then parcels can be moved in improved speed anyway if there should be an occurrence of polarization regardless of it is vertical or even there can be unsettling influence in exchanging of packets.("Understanding 802.1X Authentication", Arubanetworks.com").However there are exceptional programming for remote radios and it keep up various sign dimension. In any case, on the off chance that receiving wire is put in poor area at that point that can likewise be an issue for network. In this way we have examined how WLAN set up ought to be done and what are the consideration to be taken while introducing gadget to make remote network in different gadgets at once.
WIFI ensured get to layer 2 is the kind of security which can be utilized to secured remote system with the goal that speed in remote can be improved in secure condition. It is one of the substitution of less ensured security WEP and update of the WPA innovation. In any case, WPA 2 security is being used after 2006 in all the equipments and it deals with the premise of 802.11i encryption system. This sort of security can be utilized in little district just as in wide area as well. Aside from this there are numerous other kind of security highlights which can be empowered in these systems administration gadgets to make it increasingly secure. At the point when WPA2 security will be empowered with most grounded and high security includes then they can be associated with the traffic and can see the subtleties of the traffic be that as it may, they can't do changes in the accessible information. A standout amongst the most significant component of this set up is that programmed IP setup can be empowered in these gadgets. DHCP mode once empowered can give IP address consequently to the associating gadgets.
Assessment
WPA and WPA 2 security is one of the security convention which can be utilized to verify remote association. It encourages clients to make SSID and secret word and that can be utilized to associate with the system. Notwithstanding, client are required to pick alphanumeric character for secret key. In the event that client make alphanumeric character as secret phrase, at that point that is difficult to break. WEP security is likewise one of the regular strategy for security however that isn't much verify as WPA and WPA2. It contains just numbers as secret key and that is anything but difficult to hack. ("L. C. Mill operator, "Remote Security Protocols: WEP, WPA, and WPA2 - fakers")
When programmers can go into the system then they can acquire data put away in that server. Regardless of how quick the wired speed is remote speed constantly used to be low than wired. To improve speed in remote one can utilize repeater or passageway associated with that organize so remote system can be extended to more range. Any systems administration gadgets has some constraint and extend and in the event that clients are associated more than its ability, at that point the gadget will carry on improperly. At the point when there is more number of gadgets than availability at that point there can be increment in rush hour gridlock. At the point when there is increment in rush hour gridlock then it very well may be an issue for the security of server and capacity. Virtualization of system is significant so that on the off chance that there is separate in area of the gadgets, at that point that can be associated with the assistance of remote association.
802.1x confirmation component
It has three principle variations accessible in the system. Clients who need to verify is known as suppliant. Server which performs verification is known as RADIUS server and it is known as validation server. The gadgets accessible in system between remote passages are known as the authenticator. These three terms combinable makes the significance of confirmation component of 802.1X. It is commonly used to give full access to the clients who are mentioning to get validation for the availability of system. (J. FITZPATRICK, "The Difference Between WEP, WPA, and WPA2 Wi-Fi Passwords", How-To Geek) NETGEAR prosafe layer 2 is the validation component has all these verification system and that can be utilized related to CISCO undertaking class switch to communicate system with the end goal that it can bolster most extreme number of clients at once.
Conclusion
While finishing up this report we have talked about the plan of remote system further we have connected remote instrument in this. WPA 2 verification convention can be utilized to verify the system. We have additionally talked about the system plan for the required set up. In the given system structure we have examined how gadgets can be associated in the system. Further we have examined about the definite elaboration of system configuration to comprehend the prerequisite of broad clients.
Never be caught in plagiarism, Avail BN303 Wireless Networks and Security assignment help service of Expertsminds.com and save higher marks!
Get our Melbourne Institute of Technology Assignment Help for the below mentioned courses like:-
- BN101 Effective Participation at Work Assignment Help
- BN206 System Administration Assignment Help
- BN107 Multimedia Systems Assignment Help
- BN104 Operating Systems Assignment Help
- BN208 Networked Applications Assignment Help
- BN205 Project Management Assignment Help
- BN105 IT for Users in Organisations Assignment Help
- BN201 Professional Issues of IT Assignment Help